
SafeCam:
Webcam security
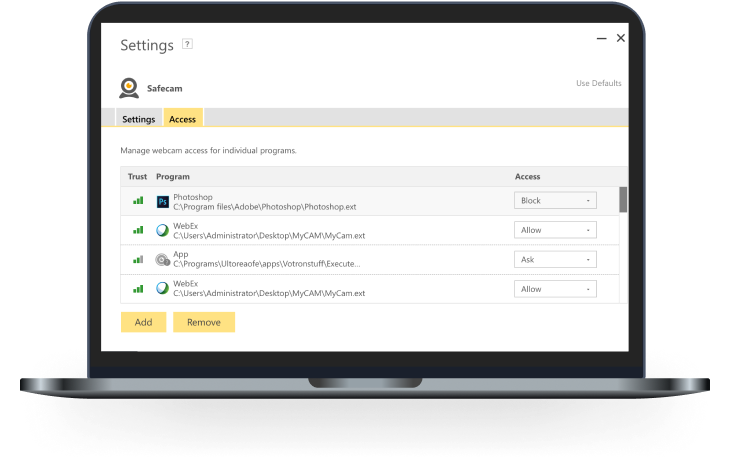
Helps to secure your PC webcam against unauthorized access.
SafeCam alerts you to attempts to access your Windows PC webcam and gives you the option to block those who are not authorized to access it.

What is SafeCam from Norton?
SafeCam helps keep hackers from gaining unauthorized access to a user’s webcam on Windows PCs.
The webcam on your PC is a great way to keep in touch with family, friends, or colleagues. But it can also be vulnerable to hacking. With SafeCam, you’ll get notified when cybercriminals try to use your webcam, so we can help you block them. SafeCam monitors software and users requesting access to your webcam and gives you the option to allow or block webcam use.5

How do webcams get hacked?
Like many types of software, the same type of tool can be used to help or to harm.
RAT: Remote Access Tool or Trojan? RAT can be an abbreviation for any of the following:
- Remote Access (or Administration) Tool
- Remote Access (or Administration) Trojan
The difference between tools and Trojans is that tools are often used to help, while Trojans are used for malicious purposes. A remote access tool can be used for legitimate reasons, such as for remote technical support. Unfortunately, some of the useful features that enable you to get computer help from home are also used in malicious Trojans, and often without the computer user’s knowledge.
Remote access Trojans are good at hiding their presence on a computer, so a victim may not even know it has been installed. Using the Trojan, a cybercriminal can do almost anything that someone physically sitting at the computer can do, including recording footage using the webcam. These types of Trojans are sometimes called “creepware.”
How do computers get infected with Trojans?
How would a cybercriminal infect your computer with a Trojan or “creepware”?
Remote access Trojans (RATs), or what we might call “creepware,” are programs that are installed without the victim’s knowledge and allow a cybercriminal to have access and control of the compromised computer from a remote location. Often, the cybercriminal will trick a victim into installing a Trojan through clicking on a malicious link or downloading a malicious email attachment.
Ways your computer could get infected include:
Drive-by downloads
By visiting a website, the user unknowingly downloads a Trojan onto their computer. This is called a drive-by download.
Malicious links
Malicious links, leading to websites hosting drive-by downloads, are distributed using social media, chat rooms, message boards, spam email, etc. The cybercriminal may also hack user accounts to make it seem like the link is being sent by a friend. Others may try to lure victims by posting enticing messages.
Exploit kits
Potential victims may visit compromised websites or click on malicious links and are then redirected to the exploit kit’s server where a script runs that will determine what exploits can be leveraged. If an exploit is viable, the victim is infected with the “creepware” and the cybercriminal is notified.
Packaged with other downloads
A Trojan can be spread through being packaged with other software or apps, such as with freeware that you might download from a website, app store, or through peer-to-peer file-sharing/torrents. Once you open and run the program, the Trojan could install with or without your knowledge, too.
Once the Trojan gets on a device, the hacker can see what you do online, capture your keystrokes such as when you type a username and password (keylogging), and could take full control of your computer, including your webcam.
The multi-layered protection in Norton 360 helps protect your computer against these cyberthreats. Even if you do inadvertently click on a bad email attachment, a link to a malicious website, or download something that has malware inside, Norton protection has many ways to identify, quarantine, and remove the threat to help your PC stay malware-free.

How does Norton protection help against webcam hacking?
By using a multi-layered defense.
Norton 360 uses multiple different protection technologies working together to help defend against malware, including the types of malware that can lead to webcam hacking. The best way to protect your PC against this threat is to help protect it against malware, and that’s exactly what Norton protection does.
Norton 360's layers of protection help defend against malware on your PC that can lead to webcam hacking:
Working together, these powerful layers of Norton technology help protect your PC against malware of various kinds, and specifically the types of malware that can lead to webcam hacking.
How can you help protect against webcam hacking?

Steps to help protect your device
Webcam hacking starts with your computer getting infected with malware, specifically a type of malware that enables remote access for the attacker. To protect against malware, and specifically to protect against types of malware that can lead to webcam hacking, take these steps:
- Always run up-to-date antivirus and security software that includes sophisticated multi-layered technology, like Norton 360.
- Use security software that includes a built-in feature for webcam protection, like SafeCam.5
- Avoid opening emails from unknown senders and clicking on suspicious email attachments.
- Exercise caution when clicking enticing links sent through email or instant messages or posted on social networks.
- Only download files from trusted and legitimate sources.
What if I accidentally download malware?
What if you make a mistake and don’t realize that you’ve downloaded a malicious file? With Norton protection, you don’t have to worry. If a threat does get through, the multiple security layers in Norton protection all work together to defend in different ways and help keep your computer free of malware, even if you accidentally downloaded it. You also have support from Norton experts as part of your Norton subscription, so you can always reach out for help if you think your computer has malware.

Webcam safety
Help protect yourself from becoming a victim of webcam hacking.
Webcam hacking is one of many types of online threats. To help protect your PC against webcam hacking specifically and malware in general, use security software with a built-in feature to help guard against unwanted webcam access. SafeCam, part of Norton 360, gives you webcam protection as part of an advanced suite of security protection for your PC.
The antivirus and security protection in Norton 360 helps protect against malware and Trojans, and SafeCam is just one more tool in your arsenal to help protect against the threat of webcam hacking.5 The multiple layers of Norton security technology work together to help defend against the many types of online threats that your PC faces today.
SafeCam from Norton
Safeguard the other window into your home.
Your webcam lets you keep in close contact with family, friends, or colleagues, but it can be vulnerable to attack, giving cybercriminals an up-close view into your home, your daily routine, and personal information.
SafeCam alerts you when access to your Windows PC webcam is attempted and helps you block those who are not authorized to access it.
SafeCam is available in Norton 360 plans.
5 SafeCam features are only available on Windows (excluding Windows in S mode, Windows running on ARM processor).
1 https://thehill.com/policy/national-security/295933-fbi-director-cover-up-your-webcam

