Are password managers safe? Yes, when you use them correctly
Reusing passwords means a single breach could expose all your accounts. Password managers can help — but are they safe? Learn about their risks and benefits, and see how Norton 360 Deluxe makes it easy to create and keep track of unique, secure passwords.

In 2022, LastPass, a popular password manager, disclosed that an unauthorized party had accessed a third-party cloud server used to store production backups, constituting a potentially serious data breach.
While the company claims no customer data was taken, the incident left many people who use similar tools questioning whether their passwords were truly safe with a password manager.
Thankfully, most password managers haven’t been involved in security incidents as severe as this one. And, many password managers use state-of-the-art security features, like bank-grade encryption, to safeguard customers’ credentials. Read on to learn about password managers, whether you should get one, and how to use them safely.
What is a password manager?
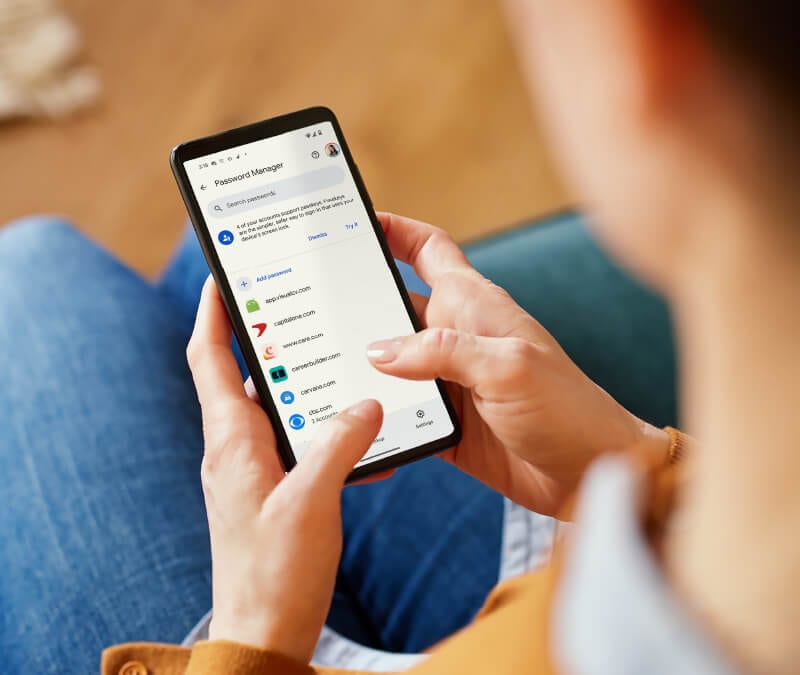
Password managers are software tools designed to help you generate, organize, and store strong, unique passwords and other login credentials. Most are apps or browser extensions. They give you easy access to your login details, eliminating the need to memorize convoluted, unique passwords for each account.
Beyond passwords, many can help you store credit card details and addresses, too. A good password manager, like Norton Password Manager, autofills logins and syncs across multiple devices.


Safety benefits of using a password manager
Password managers offer a range of benefits that help you keep your online accounts secure, including the ability to store passwords in an encrypted digital vault, generate strong passwords, and get warnings about vulnerable logins.
Strong password creation
Password managers can help you generate long, random passwords — often 15 characters or more — so you don’t have to reuse simple, easy-to-guess logins across accounts.
Some services, like Norton Password Manager, also feature a Safety Dashboard that rates the strength of your existing passwords, alerts you to duplicates, and flags old passwords, so you know when it’s time for a change.
Convenience
Password managers simplify a crucial aspect of good digital hygiene: they save your logins and fill them in automatically, so you don’t have to remember or enter them every time. This makes using stronger, more complex passwords much easier.
Strong encryption
A good password manager stores your passwords in a digital vault that’s protected with strong encryption, keeping your credentials safe from hackers. This encryption works by scrambling your data into unreadable code that can only be unlocked with your master password.
Many password managers use Advanced Encryption Standard (AES) because it’s recommended by the National Institute of Standards and Technology (NIST). Norton Password Manager goes a step further by using bank-grade AES-256 encryption.
2FA and biometric login features
Some password managers secure your vault with two-factor authentication (2FA), or multi-factor authentication (MFA) options. This adds an extra verification step — like a code sent to your phone, email, or authenticator app — on top of your master password. That way, even if someone steals your master password, they still can’t unlock your vault without that second factor.
Other password managers, Norton Password Manager included, let you use biometric technology, like fingerprint or facial recognition, to access your password vault.
Breach notifications
Some password managers also monitor for data leaks and alert you if your login details have been compromised. These notifications give you a chance to change compromised passwords right after a data breach, potentially helping you stay a step ahead of cybercriminals and by protecting your accounts before they can be hacked.


Risks of using password managers
Despite the security benefits, there are a few risks to consider when using password managers, like the potential for data breaches and software vulnerabilities.
Data breaches
No organization is totally immune from data breaches — where cybercriminals gain unauthorized access to confidential data. Unfortunately, password management providers are no exception: U.S. authorities recently seized over $23 million in cryptocurrency tied to a $150 million Ripple wallet hack. Investigators believe this was carried out using private keys extracted from compromised password vault data tied to the 2022 LastPass breach.
Single point of failure
Because your vault is protected by one master password, it can become a single point of failure. If cybercriminals steal it, they could gain access to all your stored logins — and in some cases even lock you out and demand payment through a ransomware attack.
You can mitigate this risk by securing your password vault with multi-factor or biometric authentication.
Risk of device compromise
Password managers contain sensitive information that could be stolen if your device is compromised, depending on your setup. If your phone is hacked, criminals could get access to your password manager and all of your accounts.
You have to trust the provider
Sharing your passwords with anyone takes a lot of trust, even if they’re a password management service. According to one survey of just over 1,000 people, nearly 65% of people polled don’t trust password managers. Sketchy password managers could even be fake apps pretending to be legitimate to steal your information.
As such, it’s crucial to choose an established, trustworthy password management provider like Norton —which is the most trusted brand in consumer Cyber Safety.
Software vulnerabilities
Outdated password managers may contain security flaws, such as using unsafe methods to transmit sensitive data. For example, reports allege that Apple’s iOS 18.2 Passwords app exposed users to phishing attacks for three months after launch because it contacted certain sites over HTTP instead of the more secure HTTPS protocol.
Should you use a password manager?
Yes. Although there are certain risks to password managers, using them is much safer than reusing a single password — and more realistic than memorizing a lot of unique ones. And, many of the risks inherent to password managers, like the “single point of failure” problem, can be reduced by securing your password vault with MFA or biometric login.
Password managers significantly reduce the risk of falling victim to brute force attacks, where criminals repeatedly try password combinations to force their way into accounts. They’re also generally considered to be safer than browser autofill.
Norton offers a free password manager that combines industry-leading security with user friendliness. It includes essential features like an encrypted password vault, a Safety Dashboard, and a strong password generator.
Avoid these mistakes when using a password manager
Here are some common mistakes people make when using password managers, and how you can avoid them:
- Using a weak master password: A short, simple password can put all your logins at risk. Use your password manager’s password generator to create a strong passphrase, ideally at least 15 characters long.
- Not enabling 2FA: Always turn on 2FA for both your digital vault and the accounts stored in your manager. This extra step means cybercriminals will need more than just your password to hack into your accounts.
- Storing passwords elsewhere: Writing passwords down or saving them in a spreadsheet leaves your credentials exposed. Instead, install your password manager on all your devices so you can access them securely.
- Ignoring updates: Regularly updating your software resolves vulnerabilities sometimes found in old versions of software.
- Ignoring warnings: Some password managers include safety checkups that notify you of exposed credentials. When you receive these warnings, change your passwords as soon as possible.
- Logging into untrusted devices: Only use your password manager on trusted devices, like your personal computer or phone. Using a password manager on a public computer can expose your password data when the next person uses it.
- Using an untrustworthy provider: Rely on a trusted provider to keep your passwords stored securely. Untrustworthy providers might rely on weak cloud security, which exposes your passwords when syncing them between devices.
Keep your online credentials safer
Securing your online credentials with a password manager is a great first step, but it’s just one part of a strong cybersecurity strategy. Install Norton 360 Deluxe for comprehensive protection that includes award-winning antivirus, AI-powered scam detection, and a VPN — not to mention a password manager. Help safeguard more than just your login credentials: get 360 degree protection for your digital life.
FAQs
Can password managers be hacked?
Cybercriminals can potentially hack vulnerable password managers by infecting user devices with malware, taking advantage of computer vulnerabilities, or using social engineering to trick people into revealing their master credentials.
Which password managers have not been hacked?
Password managers that have not been hacked include Norton Password Manager, Keeper, 1Password, and RoboForm. Some of these password managers have been targeted by cybercriminals in the past, but none have had their systems broken into.
Is Norton Password Manager safe?
Norton Password Manager is safe. It’s owned by the most reputable brand in consumer Cyber Safety, and Norton has a strong track record in cybersecurity, making it an excellent choice for online password management.
What is password peppering?
Password peppering is when you store part of your password elsewhere, while your password manager keeps the rest of it. This helps prevent hackers who have access to your password management account from breaking into other accounts, because they won’t have your full password.
Is Google Password Manager safe?
Google Password Manager is generally considered safe thanks to two-factor authentication and Google’s strong security infrastructure, with no major breaches reported. However, it lacks zero-knowledge encryption, meaning Google could technically access your data — a drawback for many security-conscious users.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.








Want more?
Follow us for all the latest news, tips, and updates.