Website spoofing: What to know about counterfeit domain names
Website spoofing, aka domain spoofing, occurs when a scammer mimics the website of a trusted company with the goal of stealing visitors' personal information.

What is website spoofing?
Website spoofing, aka domain spoofing, occurs when a scammer creates a fraudulent website, mimicking a trusted company, oftentimes with the goal of stealing visitors' personal information.
Many people are under the impression identity theft only affects individuals. The reality is that the identities of businesses are constantly under attack, too. When the identity of a website gets stolen, it’s known as website spoofing.
Similar to how counterfeit clothing can run the spectrum of easy to spot to unbelievably hard to identify, spoofed websites can, too. But when you fall for a fake website, you run the risk of compromising your personal data. Due to the growing threat spoofed domains pose to consumers, it’s important to learn the tactics spoofers use for their scams—and how to avoid them.
What is website spoofing?
Have you ever visited the website of a well-established brand but something about it didn’t seem right? Maybe the user interface seemed outdated, or the grammar was incorrect? That may not have been the brand’s website at all. You may have been visiting a spoofed website.
Website spoofing, also known as domain spoofing, occurs when a scammer creates a fraudulent website for the sake of stealing from its visitors. This starts with registering a domain name that is nearly identical to the intended landing page. Some of these web spoofers are so sophisticated they can accurately mimic the user interface of a legitimate website. But even crudely constructed scams can cost unaware visitors dearly.
After the scammer has gained your trust, they will try to steal your personal information, like usernames and passwords, or they will download malicious software onto your computer.
How does website spoofing work?
Registering a domain name requires little effort and has little oversight. There are some barriers in place to prevent near-identical domains from being created, but scammers are clever enough to find workarounds. If they can mask their website’s identity as something else, their mission is almost accomplished.
After a person has fallen for a spoofed website, they will likely carry on with their normal behavior without a second thought. This could include typing in their username and password or entering in credit card information, which is exactly what the scammer is hoping for.
Even though you think it’s business as usual, the website is saving whatever information you enter. The scammer can then use your login information to gain access to the legitimate website, or any other website that uses the same username and password. Or they will have saved your credit card info to then go on a shopping spree on your dime.
Another danger with spoofed websites is that they can be programmed to drop malware onto your computer. This is potentially more devastating because they could gain access to any information you save on that device.
Website spoofing vs. email spoofing
Website and email spoofing are separate tactics scammers use to get access to your personal information, but they are often used in conjunction with one another. A spoofed email will sometimes link to a spoofed website to make it seem legitimate.
While spoofed websites passively rely on potential victims to find them, email spoofing requires an active campaign by the scammer to find victims.
Spoofing a website entails constructing a relatively convincing fake website, but email spoofing only needs a false sender address. Oftentimes, the spoofer will utilize spear phishing tactics within the email to attain their goal.
Web spoofing examples as cyberattacks
Web spoofers follow similar tactics and make common mistakes in their attempts to dupe their victims. That makes it possible to identify them for what they are.
Incorrect spelling and grammar
Spelling and grammar mistakes in an email or website are a red flag that it has not originated from a professional organization. It is quite common for the text to have been sent through a language translator.
Phishing email makes suspicious requests
The body of the email often contains a shocking accusation that requires immediate action for you to lower your guard. Banks, governments, and retail businesses have standard practices for resolving issues. If an email claiming to be from a trusted source asks you to act out of the ordinary, contact the originator through the official channels.
The website URL is unsecure
The website lacks basic URL security protocols. Sometimes your browser will warn you when it detects that a website is not safe to visit. This shouldn’t be ignored, nor should it be relied on. Your browser can be fooled, too.
Double-check the details
If a scammer executes the spoofed website well enough, it may be hard to distinguish it from the real thing. Before entering your login information or clicking on anything at all, take a moment to double-check these known red flags.
How to spot a spoofed website
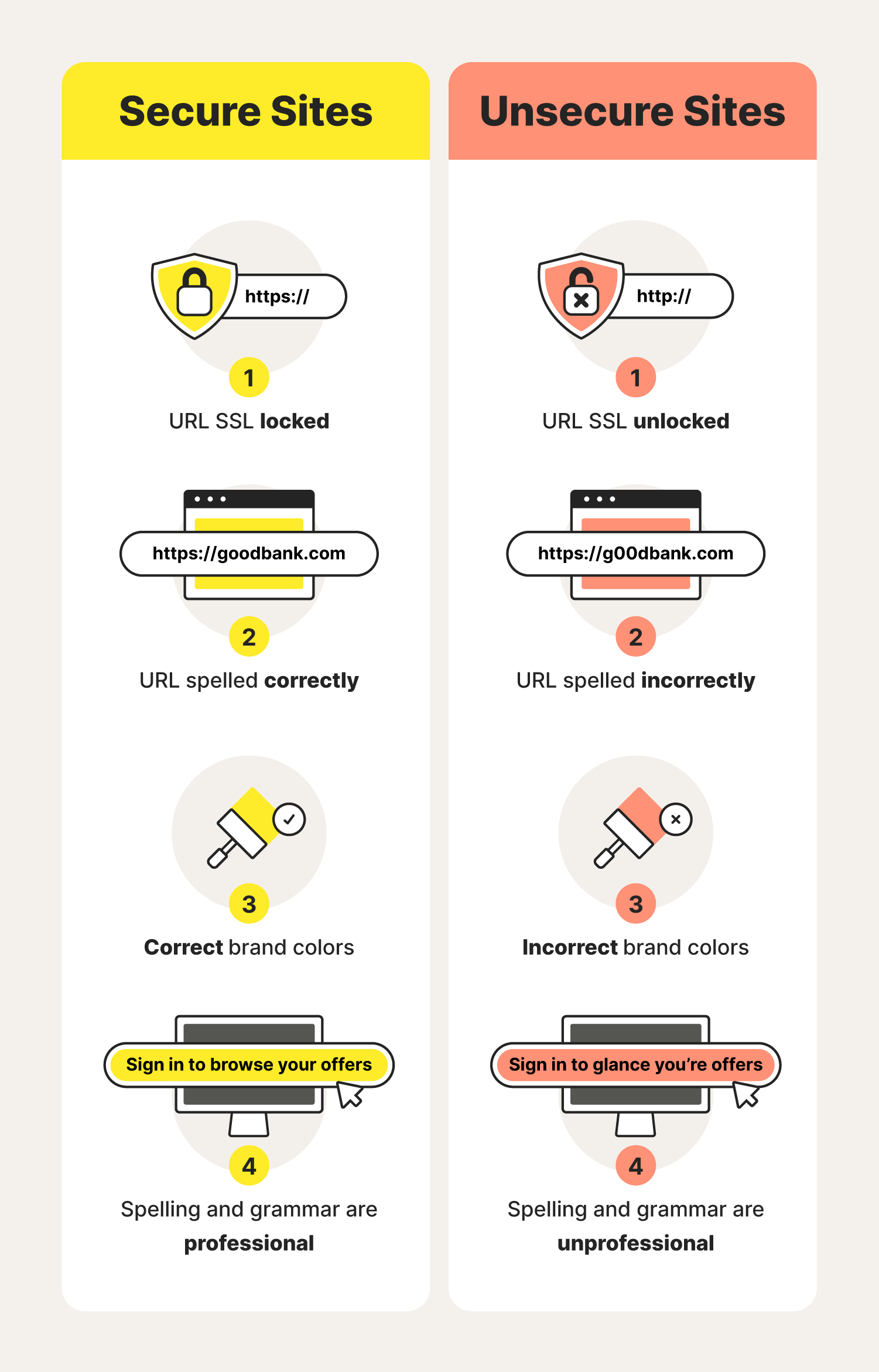
Experienced spoofers will often try to copy the graphic design of a website as closely as possible. But a trained eye will be better able to discern the real thing from a fake by knowing a few key details.
1. Look at the URL
The most common tactic among website spoofers is creating a URL that is nearly identical to a legitimate website. The URL may only be off by one letter, even using the number “1” in place of a lowercase “l”. People can easily direct themselves to the spoofed page by mistakenly typing the wrong key or by only glancing at the URL before clicking through.
2. Check for an SSL certificate
A Secure Sockets Layer (SSL) is an added level of security for every visitor on a website. It is an encrypted link that protects your sensitive information from being shared without your consent. It is usually represented by a lock or green icon next to the URL. An SSL is not a guarantee that a website is legitimate, but it is a solid piece of evidence in its favor.
3. Make sure the domain matches the SSL certificate
Since a third party produces the SSL for the website, double-check the certificate by comparing it to the URL. Click on the SSL icon to validate its security. If it was issued to a website that is different from the domain in the URL, then something fishy is going on and it shouldn’t be trusted. That might be a URL spoof.
4. Avoid clicking mysterious links
With the tactics of cybercriminals continuously improving, not even your own eyes and judgment can be trusted 100% of the time. The best way to evade a malicious link is to avoid clicking it entirely. Manually type the domain name into your browser to increase the likelihood of reaching the legitimate destination.
If you suspect a website is mimicking an established site for malicious reasons, report the website for scamming to protect yourself, other uses, and organizations against phishing, malware, and fraud.

How to protect yourself from website spoofing
For help avoiding this common online scam, follow these best practices. With enough practice, they will soon become second nature.
Use a spam filter
Send spoofed emails directly to your spam folder to reduce the risk of accidentally opening one. The spam filter is not guaranteed to catch everything, however, so stay aware.
Avoid clicking links and attachments in emails
Avoiding clicking unknown links is common internet practice, but what if you think you do know the source of the link? Since there’s a chance the email did not originate from the claimed sender, it is wise to avoid the link anyway.
Use bookmarks for frequently visited pages
Since random links will be left unclicked, it’s convenient to bookmark websites you regularly visit. This speeds up the process of visiting the page while reducing the chance of human error in typing it by hand.
Manually search URLs
If you must visit a page that is not already bookmarked, manually search for the URL. This avoids the risk of a malicious link planting a virus on your device. Take care that the URL is spelled correctly, otherwise, you will not reach the intended page.
Use an antivirus program
A competent antivirus program may make up for shortcomings in user practice. It can block malware before it can download to your device, or it can raise a red flag when you visit a dangerous website.

The freedom to connect more securely to Wi-Fi anywhere
With Norton™ VPN, check email, interact on social media and pay bills using public Wi-Fi without worrying about cybercriminals stealing your private information
Try Norton VPN for peace of mind when you connect online
Even with responsible internet usage, scammers can slip through your defenses. That’s why it’s recommended you clean your devices periodically. Every little bit of extra effort goes a long way toward making yourself a hard target.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.





Want more?
Follow us for all the latest news, tips, and updates.