Trojan viruses explained (plus tips on how to remove them)
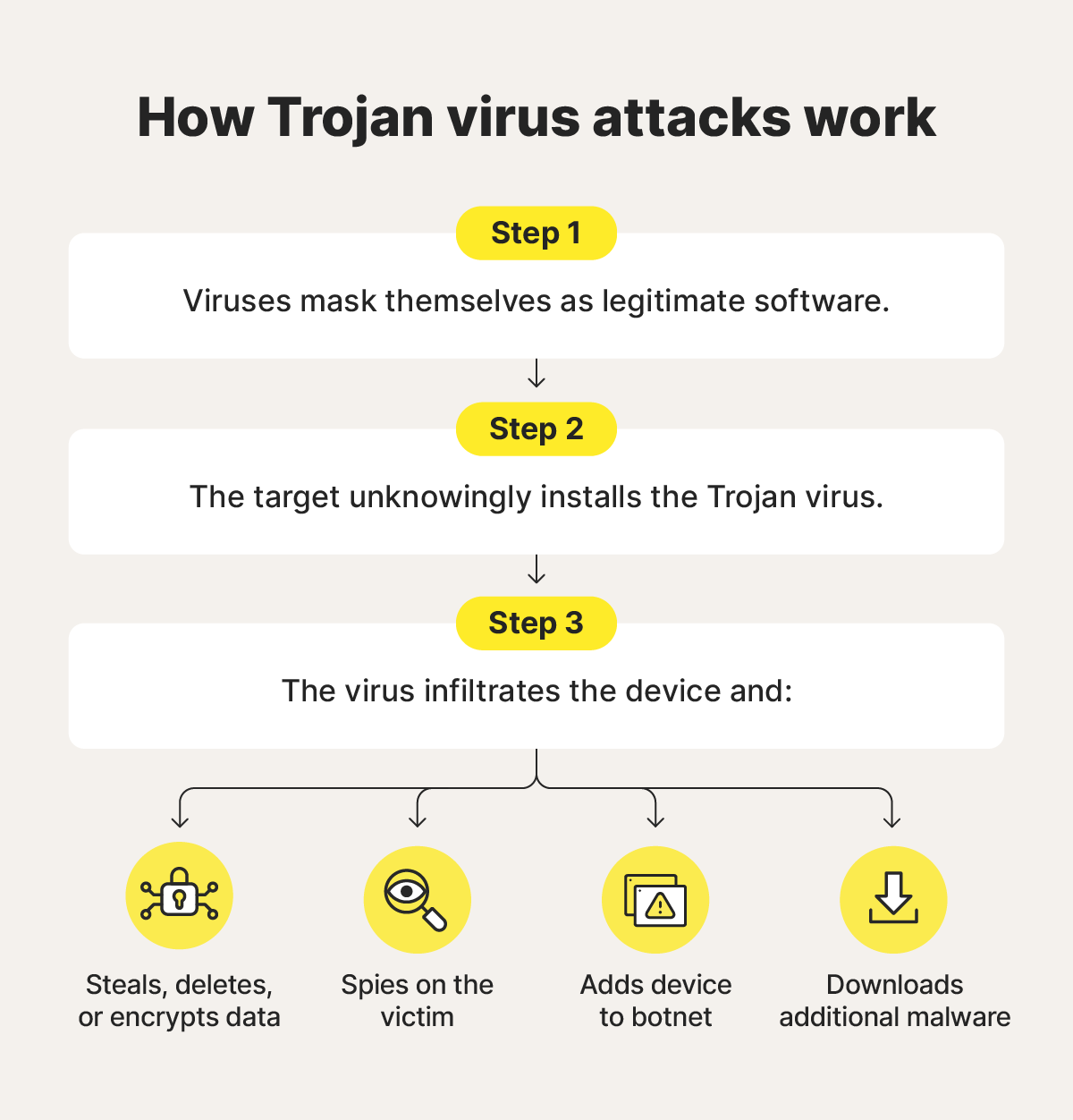
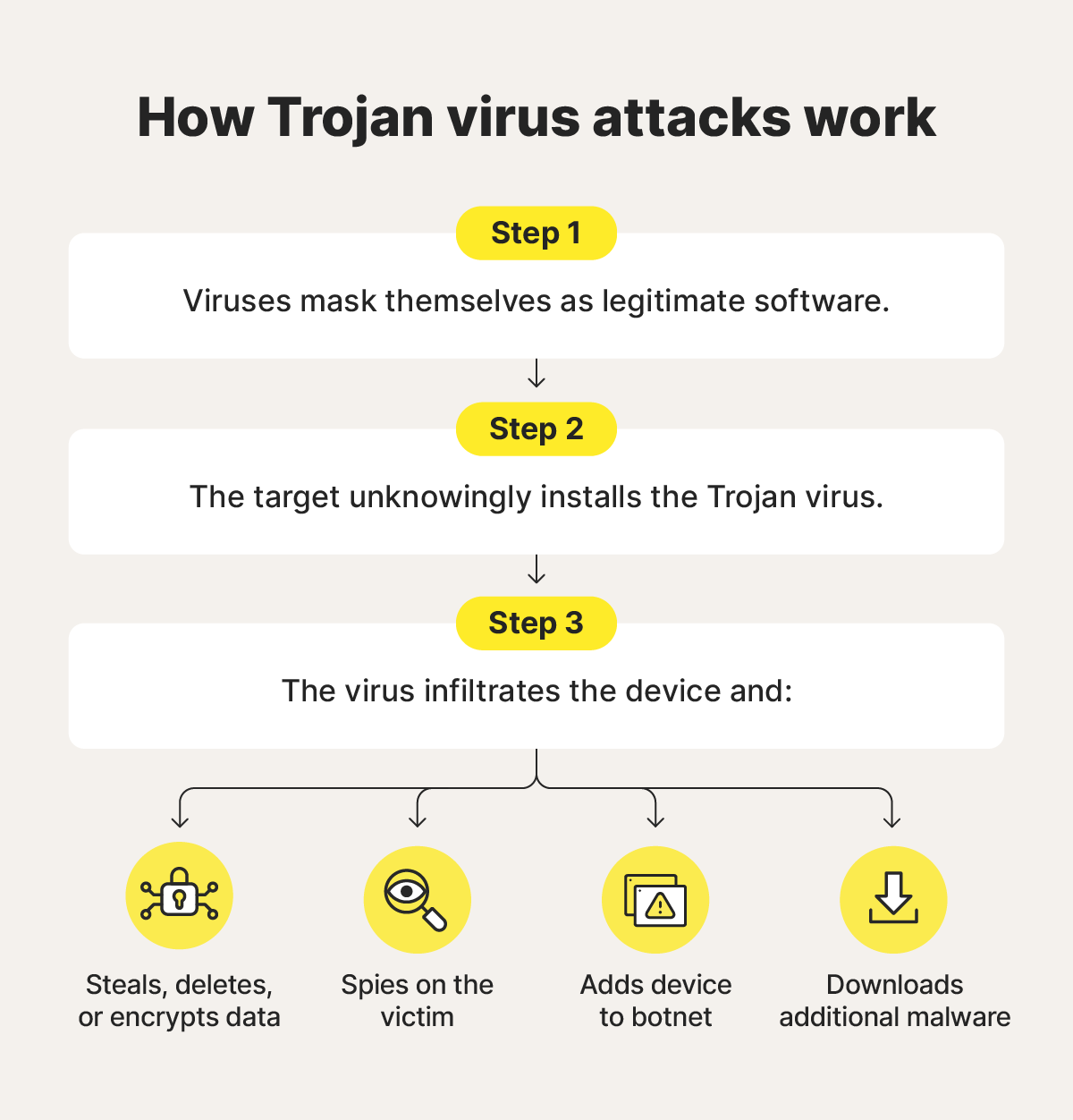
Trojan viruses disguise themselves as harmless files to trick you into installing them, giving hackers access to your system. Learn more about Trojans, how to spot and remove them, and how anti-malware software can help protect against Trojans and other online scams.

A Trojan virus is like a wolf in sheep’s clothing — or, like in the Homeric legend it’s named for, offensive threats hiding in a massive wooden horse. Trojans mask themselves as legitimate files to sneak into an unsuspecting victim’s device. Learn more about what Trojans do, the different types, and how you can help protect against these dangerous viruses.
What is a Trojan virus?
A Trojan virus is a type of malware that hides within a legitimate file or program to gain access to your device. Trojans are often hidden in otherwise normal looking application downloads, software updates, or email attachments.
Unlike traditional computer viruses, Trojans can’t self-replicate, meaning they can’t copy themselves and automatically spread to other files or devices. Instead, the user must fall for the ruse and (unknowingly) install the virus, usually by clicking an infected link or downloading a harmful file.
After installation, Trojans can spy on victims, steal or destroy data, and wreak system-wide havoc. This enables attackers to commit financial fraud, identity theft, and other crimes.
What does a Trojan virus do?
Trojan horse viruses can carry out a range of malicious activities across various operating systems, including Android, iOS, Linux, macOS, and Windows — although execution and impact vary between platforms. The viruses can steal, manipulate, or delete data; install other malware; create backdoors for remote access; and eavesdrop.
Here’s a closer look at some common actions Trojans perform:
- Data manipulation: Trojans can steal sensitive data from your computer, such as login credentials, credit card details, and personal files. They can also potentially encrypt data to extort a ransom.
- Data destruction: Certain Trojans are programmed to delete files, corrupt data, or even reformat entire hard drives.
- Botnet recruitment: Some Trojan horses are designed to turn infected computers into part of a botnet, a network of compromised devices that cybercriminals can control remotely.
- Espionage: Trojan horses can be used to monitor a user’s activities, capture screenshots, and record keystrokes to covertly gather sensitive information.
- Malware installation: Trojans may install additional malware, allowing attackers to expand their control, escalate privileges, or carry out further malicious activities.
History of Trojan viruses
The concept of the Trojan virus is based on the legend of the Trojan horse — a story about Greek soldiers hiding in a large wooden horse. The Greeks presented the horse to the Trojans as an apparent gift, and once inside the city walls, the hidden soldiers emerged and ambushed unsuspecting citizens.
Here’s a timeline of how Trojan malware has advanced since its creation to the current day:
- 1970s: An early, relatively harmless version of the Trojan virus emerged as a guessing game called ANIMAL. To users, it appeared as a 20-question guessing game. Behind the scenes, the game spread across shared directories and entire networks.
- 1980s: Trojans became a threat when the AIDS Trojan was copied onto 20,000 floppy disks and mailed to participants at a World Health Organization convention. It lay dormant until the victims’ computers had been rebooted 90 times, at which point it encrypted their files and demanded a ransom for their release.
- 1990s: With the rise of internet usage, Trojans began to infect email attachments, targeting more people faster.
- 2000s: The rise of botnets allowed attackers to remotely control networks of Trojan-infected computers, using them for spam, distributed denial-of-service (DDoS) attacks, and data theft.
- Today: Countless types of Trojan viruses are currently circulating; cybercriminals continuously develop and adapt them to suit their objectives.
Types of Trojans
There are several types of Trojans in use today, with some overlap between several of them. Some give attackers remote access to devices, while others download additional malware, and others steal data.
Here are some common types of Trojan horse malware and what they do:
- Backdoor Trojan: These Trojans create a “backdoor” on the victim’s computer, granting attackers unauthorized access. This backdoor allows them to control the system, steal data, and introduce more malware.
- Rootkit Trojan: A rootkit Trojan embeds itself deep within an operating system, making it difficult to detect. It allows attackers persistent and often complete control over the compromised device.
- SMS Trojan: An SMS Trojan is a type of malware that sends or intercepts text messages on an infected mobile device, often subscribing victims to premium services or intercepting two-factor authentication codes.
- Ransom Trojan: A ransom Trojan, or ransomware, encrypts the files on a victim’s computer and demands a ransom payment, typically in cryptocurrency, in exchange for the decryption key.
- Banking Trojan: A banking Trojan targets online banking credentials and financial information by capturing keystrokes, form data, or website content, enabling attackers to steal money directly from the victim’s account.
- Mailfinder Trojan: A Mailfinder Trojan harvests email addresses stored on your device for spam and phishing attacks.
- Downloader Trojan: The primary purpose of a downloader Trojan is to download additional content, such as more malware, onto the infected computer.
- Infostealer Trojan: As the name suggests, this type of Trojan steals sensitive data from the victim’s computer, like passwords, credit card information, or personal files.
- Remote Access Trojan: A RAT gives the attacker complete control over the victim’s computer, effectively turning it into a tool for cybercriminals to exploit.
- Distributed Denial of Service Attack Trojan: These Trojans perform DDoS attacks, flooding a network with traffic to overwhelm and crash it.
- Spy Trojan: A spy Trojan secretly monitors user activity, such as keystrokes, browsing history, and screenshots, and transmits this information to attackers, enabling identity theft, surveillance, and theft of sensitive data.
Trojan virus examples
Modern Trojan computer viruses come in various forms with different purposes and capabilities. Here are some examples of well-known Trojan malware and details about what criminals use them for:
- Rakhni Trojan: Rakhni is a Trojan known to act as both a data-stealing Trojan and ransomware, allowing attackers to not only exfiltrate sensitive information but also encrypt files and demand a ransom. If no Bitcoin-related files are found on the infected device, it may instead install cryptocurrency mining software.
- Tiny Banker: Tiny Banker, also known as Tinba, is a lightweight Trojan specifically designed to steal online banking credentials and other sensitive banking data through malicious forms and pop-up windows.
- Zeus: The Zeus Trojan orchestrates sophisticated attacks to acquire banking credentials and extract sensitive financial data. Its precision has made it a popular choice for cybercriminals, and since peaking in the early 2010s, it has left a trail of compromised financial systems.
- Emotet: Emotet started as a banking Trojan but was quickly adapted to help execute different kinds of cyberattacks. It can spread various types of malware, including ransomware, and is highly unpredictable and difficult to detect.
- Crocodilus: The Crocodilus Trojan is a new and sophisticated threat targeting banks and cryptocurrency wallets to compromise credentials.
- Petya: Is a family of encryption malware that explicitly targets Microsoft Windows systems by infecting the master boot record. That move causes a process to begin that encrypts the file system table of the hard drive, preventing Windows from starting up.
- DarkComet: Once a legitimate tool for remote computer management, DarkComet has been hijacked by hackers and become a RAT. This tool allows cybercriminals to steal sensitive data and money by secretly gaining unauthorized access and controlling computers without a user’s knowledge.
- CryptoLocker: As a type of ransomware, CryptoLocker encrypts files on a victim’s computer until a ransom is paid. It was one of the first ransomware strains to demand Bitcoin for ransom payments.
How to detect a Trojan virus
Since Trojan horse viruses disguise themselves, they can be tricky to spot at a glance. To detect a virus, you should run a full system scan with antivirus software, especially if you notice warning signs of a virus, like:
- Poor computer performance: Your computer may run slower than usual, applications may take longer to load, or the system could freeze unexpectedly.
- Slow data: Internet speeds may slow, or you might notice excessive network activity, even when you aren’t actively using the internet.
- Pop-up ads: There could be a sudden increase in intrusive and persistent pop-up advertisements, even when you aren’t browsing the internet.
- System settings changes: You might observe changes to your desktop background, browser homepage, default search engine, or other system settings that you didn’t make.
- Application glitches: Applications might start behaving erratically, crashing frequently, or displaying unusual error messages.
- Redirects to malicious websites: Your web browser might unexpectedly redirect you to unfamiliar or suspicious websites when you try to access legitimate pages.
- Unfamiliar icons in your taskbar: You might see new and unfamiliar icons appearing in your system tray or taskbar.
- Missing or newly encrypted files: Some of your files may go missing or be replaced with files you can’t open.
How to get rid of a Trojan virus
If you think your computer is infected with a Trojan virus, get rid of it immediately. To do this, you need to stop the malware from communicating with attackers, remove the infected files, and take steps to protect against future attacks. Here’s how:
- Disconnect your computer from the internet: Going offline helps prevent the malware from communicating with its command-and-control servers, limiting further harm.
- Reboot in Safe Mode: Restarting your computer in Safe Mode means that only the basic, necessary programs, drivers, and apps are running. This reduces the attack surface for any infection and limits the number of files and programs you need to scan with an antivirus tool.
- Install a reputable antivirus tool: A trusted antivirus tool, such as Norton AntiVirus Plus, can help identify, quarantine, and remove the Trojan. Run a full-system malware scan and follow the prompts to delete any threats.
- Take preventive measures: After you’re rid of the Trojan malware, keep your software updated to help protect against future malware infections. Also, use a firewall to monitor and block suspicious network activity. If you’re using Norton AntiVirus Plus, its built-in Smart Firewall can help with this.
Get the powerful protection your devices deserve
Trojans, viruses, and other malware haven’t gone away — they’re still a very real, persistent threat. That’s why taking a proactive approach to online security is as important today as it’s ever been.
Norton AntiVirus Plus provides multiple layers of security, including built-in hacking protection, a firewall, and real-time monitoring for scams and viruses to help keep your devices and personal information safer.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.










Want more?
Follow us for all the latest news, tips, and updates.