What are browser hijackers? Removal + prevention tips
Are you getting redirected to random pages or being hit with distracting pop-ups while browsing online? If so, your computer might be infected with a browser hijacker. Thankfully, browser hijackers are often pretty easy to remove. This guide will explain how browser hijackers work, how to recognize them, and how Norton 360 Deluxe can help detect and prevent online attacks.

How browser hijackers work
Browser hijackers work by piggybacking on your preferred browser, altering the settings to redirect you to a different website that generates ad revenue for the hacker. In more serious cases, a browser hijacker installs spyware or ransomware that can steal sensitive information or force you to pay a ransom to regain access to your device.
A browser hijacker infection begins after you click an infected link or email attachment, or when you visit an infected website. Web browser or add-on installations can sometimes include hidden browser hijacker malware. Freeware, adware, and spyware infections might also include this type of malware.
Introducing Norton Neo: The secure AI-native browser
Norton Neo is the first browser to seamlessly integrate AI with comprehensive, built-in security features at its core. With default ad-blocking, anti-tracking, and real-time AI threat analysis, Neo combines world-class browsing protection with intelligent navigation so you can enjoy a safer, smarter internet.
Impact of browser hijackers
Browser hijackers can range from merely inconvenient to downright disastrous, depending on how they work. Here are the most common ways a browser hijacker can affect a device:
- Make changes to your browser: Instead of directing you to your desired webpage, the browser hijacker will send you to a different location, usually to boost the hacker’s traffic or ad revenue.
- Install unauthorized toolbars: Browser hijackers can install additional, unwanted toolbars and extensions.
- Track your online activity: By installing malware or spyware that tracks your online activity, browser hijackers can help scammers build a profile of your location, web searches, and browsing habits.
- Cause an adware infection: Hijackers can install adware that clogs up your screen or slows down your device when you open your browser.
- Lead to identity theft: Once hackers have a foot in the door, they might be able to hijack your entire device and use its contents to steal your identity.
Warning signs of browser hijackers
It is usually fairly easy to tell if your browser has been hijacked. Look out for the following warning signs:
- Redirected searches: Instead of navigating to your desired webpage, you find yourself on a completely different website, potentially an unsafe website.
- Frequent pop-ups: Your browser is flooded with pop-up ads every time you’re online. At best, it’s annoying; at worst, clicking a rogue ad could infect your device further.
- Slow loading: Web pages are suddenly taking ages to load, if they load at all. That could be because a browser hijacker has commandeered your device’s resources or storage space.
- Unwanted extensions: You are seeing new, unwanted programs on your web browser that you didn’t install. These might be toolbars, extensions, or add-ons that popped up seemingly out of nowhere.
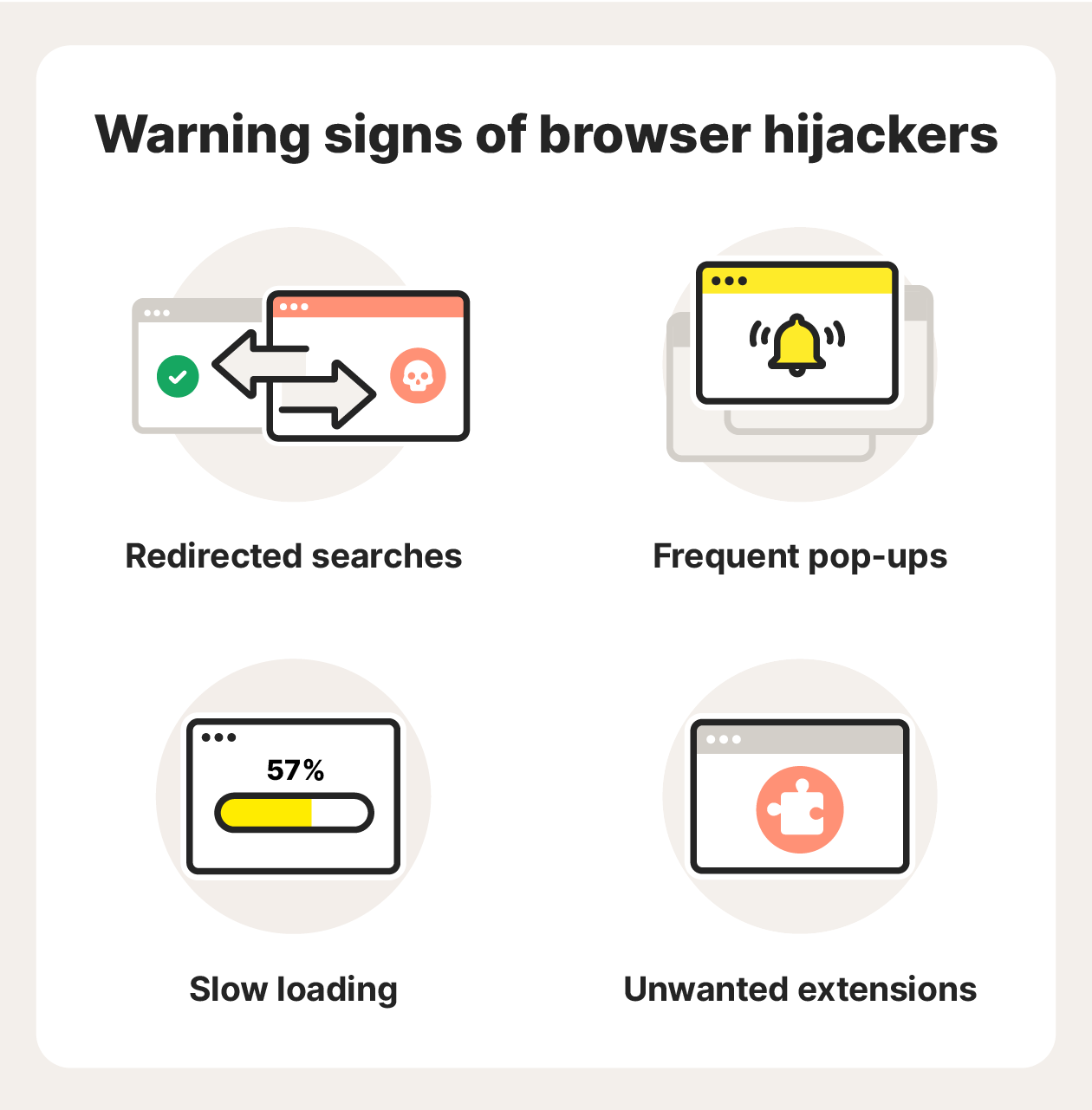
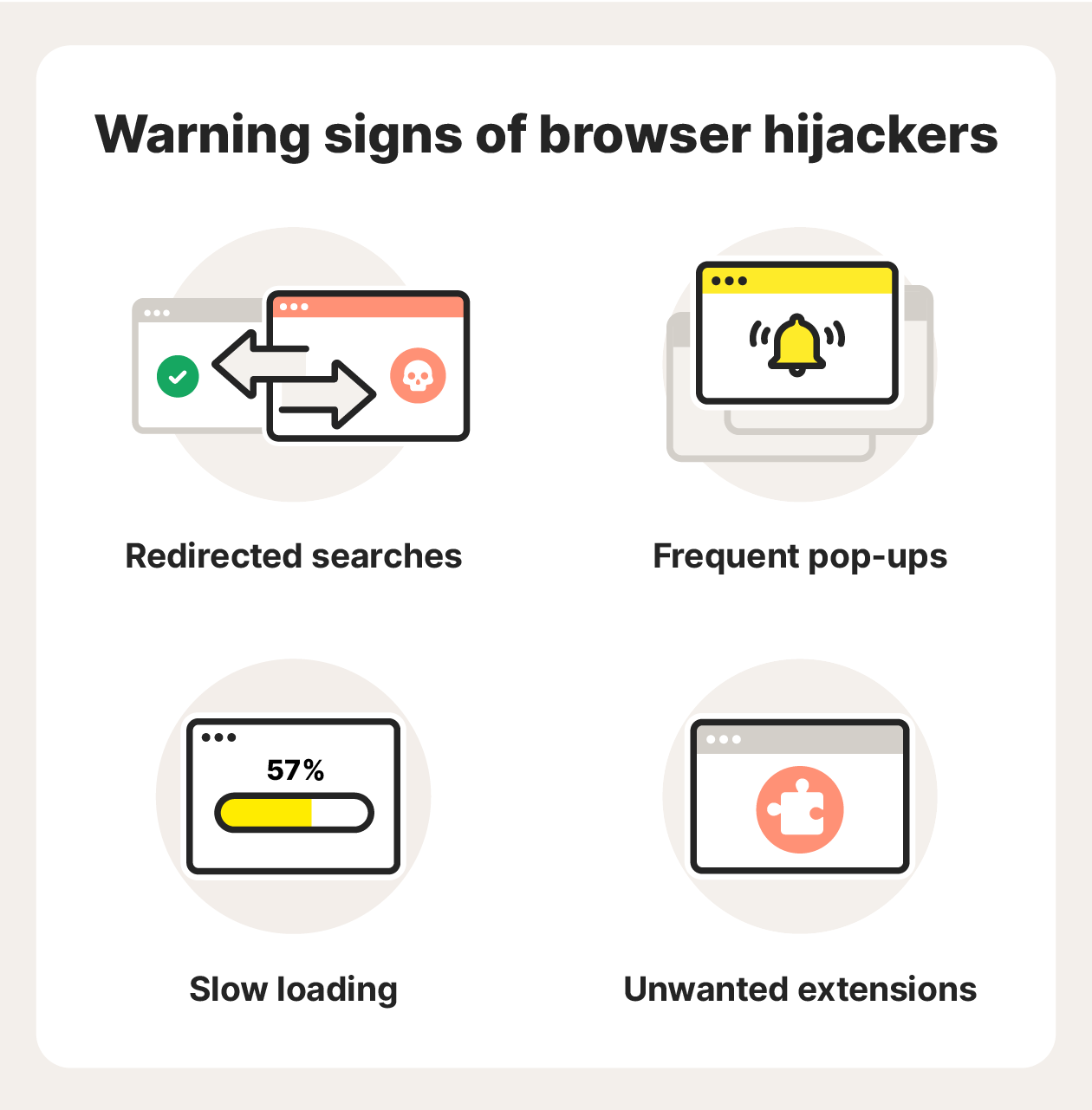
If you experience these signs of malware, you may be dealing with a browser hijacker.
Examples of browser hijackers
Browser hijackers come in many different shapes and sizes. Some spam you with pop-up ads or redirect you to a different website, while others might track your browsing patterns or log your keystrokes to unearth sensitive data such as passwords and credit card information.
Here are some of the more common browser hijackers to look out for:
Ask Toolbar
When you download a free product, it might come bundled with the Ask Toolbar browser hijacker. This will replace your preferred web browser with Ask Toolbar without your consent.
As well as being annoying and intrusive, Ask Toolbar has been linked to security and privacy risks. So if your browser is redirecting to Ask Toolbar, remove it immediately.
GoSave
GoSave is a plug-in that often comes bundled with other downloads without your knowledge or consent. It claims to offer you discounts when shopping online, but its purpose is often to spam you with ads and track your online browsing patterns.
Never click a GoSave ad, as you might be endangering your cybersecurity and opening yourself up to further malware. Clear your browser cache and cookies to keep your browser clear of this annoying plug-in.
Coupon Server
Coupon Server is a type of adware that creates pop-up ads. The Coupon Server homepage is a search hijacker — its homepage is disguised as a search engine. In reality, the site hijacks your browsing session instead of directing you to your desired website.
As well as being irritating, Coupon Server puts your data security at risk by taking over your browser settings and tracking your browser habits without your knowledge.
CoolWebSearch
Instead of being directed to Google Chrome, Safari, Microsoft Edge, or your browser of choice, this browser hijacking spyware will redirect you to its own search engine, CoolWebSearch. Every time you use this search engine, it generates revenue for the site.
Not only that, but CoolWebSearch might infiltrate your bookmarks and search history to add its sponsors, including adult websites and online gambling.
RocketTab
RocketTab is another common adware that hides behind your browser and creates pop-up ads. Like many other browser hijackers, RocketTab is often bundled with a free download without your knowledge.
Always be mindful of what you’re clicking while you browse, and if you find that your websites keep redirecting you to random sites, check the installed programs on your device and start the process of removing the browser hijacker.
How to get rid of browser hijackers
Once you know you have a browser hijacker infection, it’s usually relatively simple to remedy. Follow these tips to get rid of a browser hijacker:
- Clear your DNS cache: Clearing your cache can remove malicious files hiding in your browser, including browser hijackers.
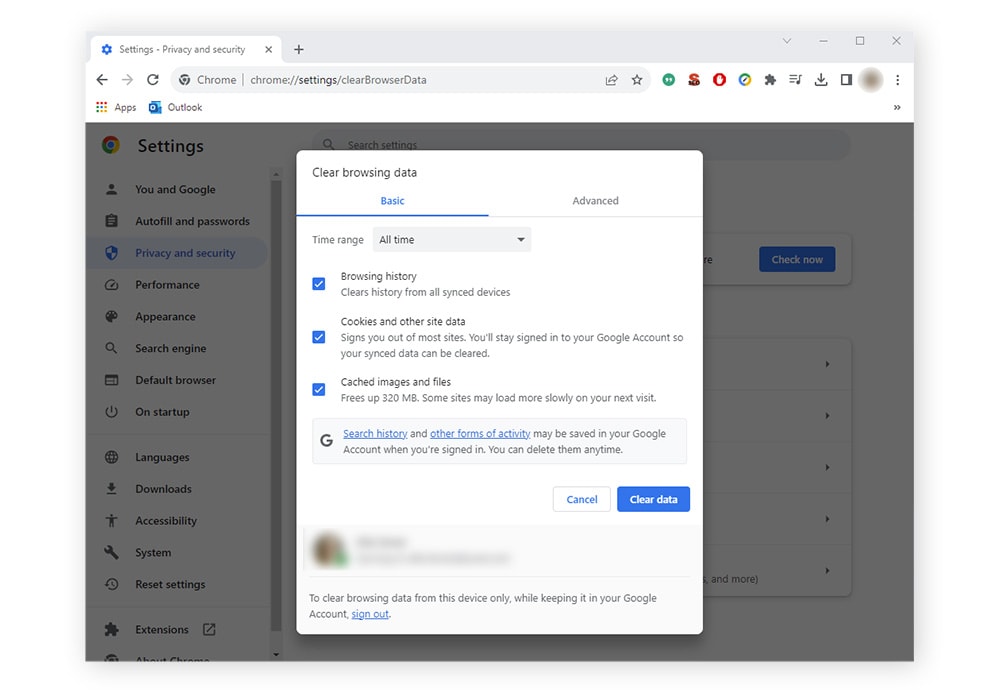
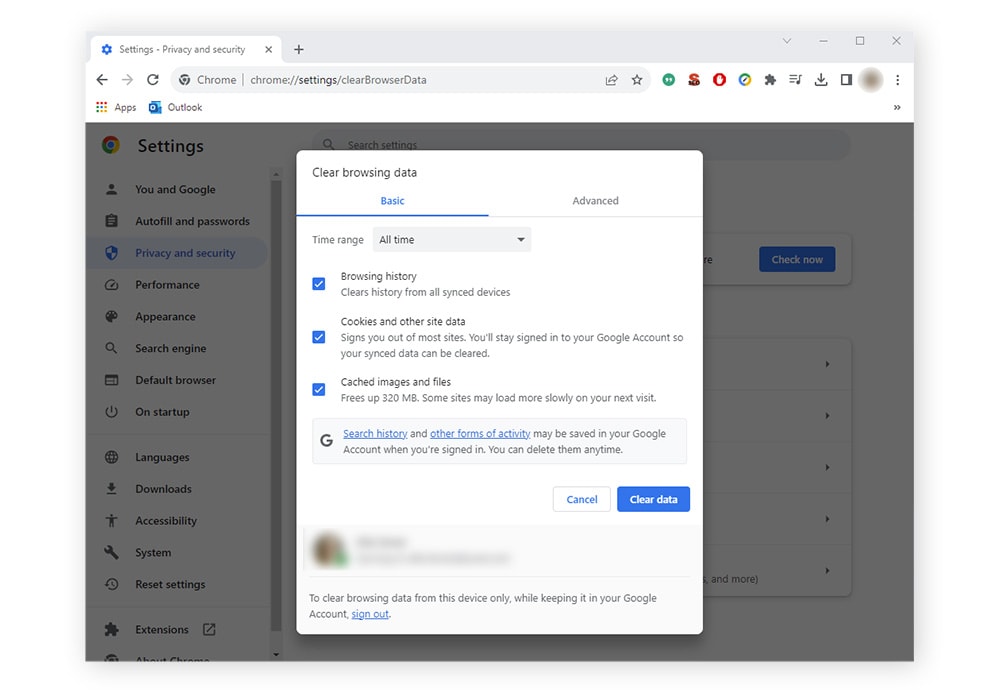
- Reset your browser homepage: In some cases, resetting your browser settings will shake off the browser hijacker malware. You can also try uninstalling and reinstalling your browser to reset the settings.
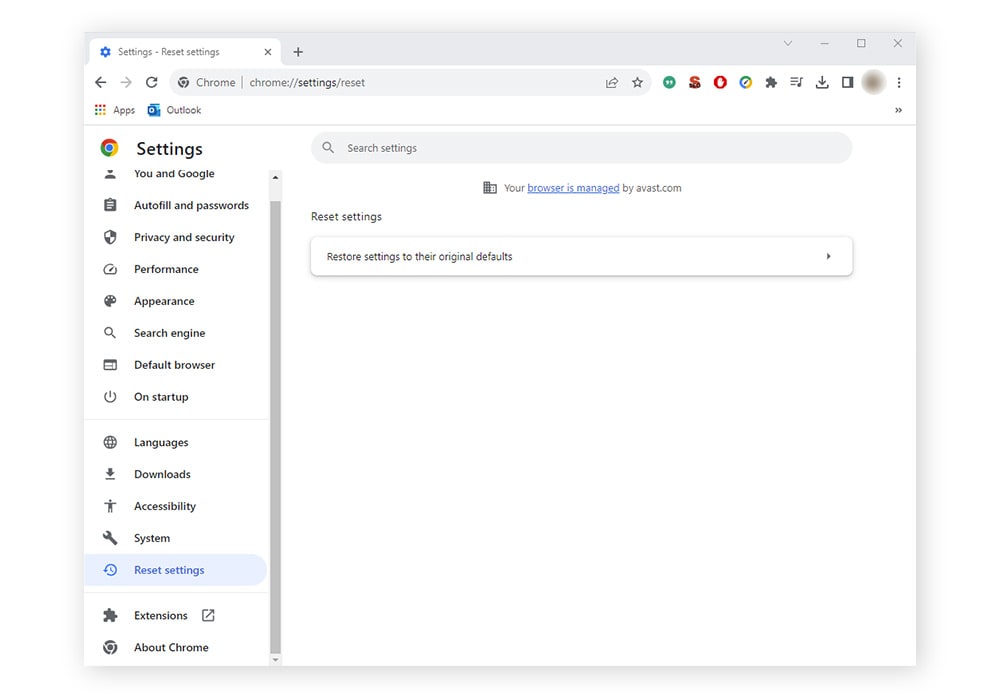
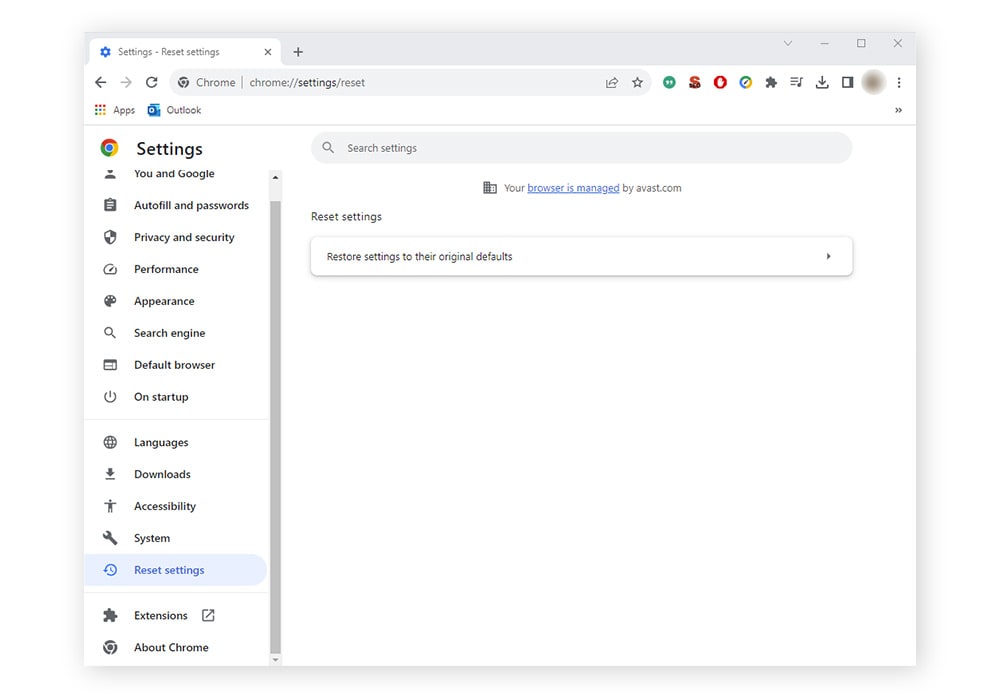
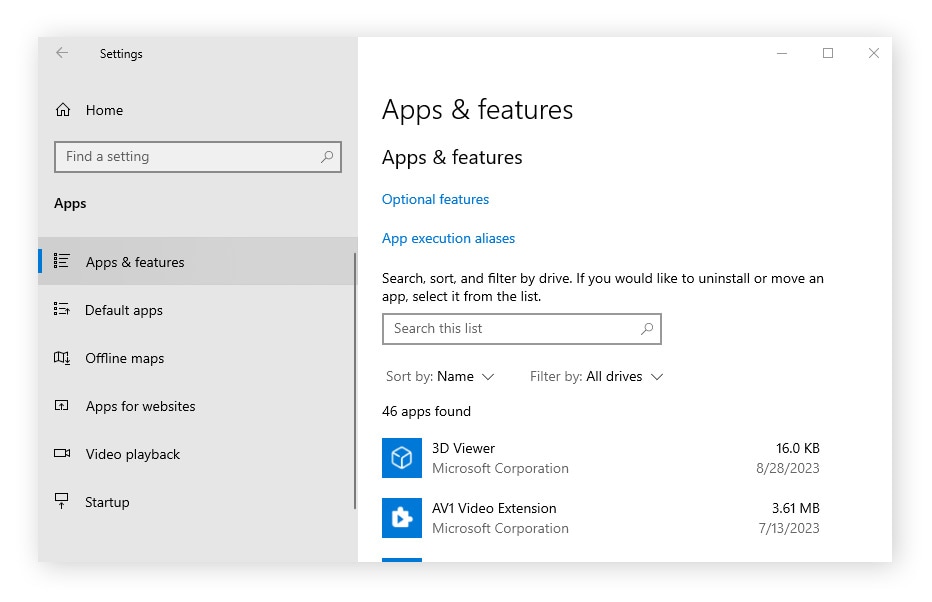
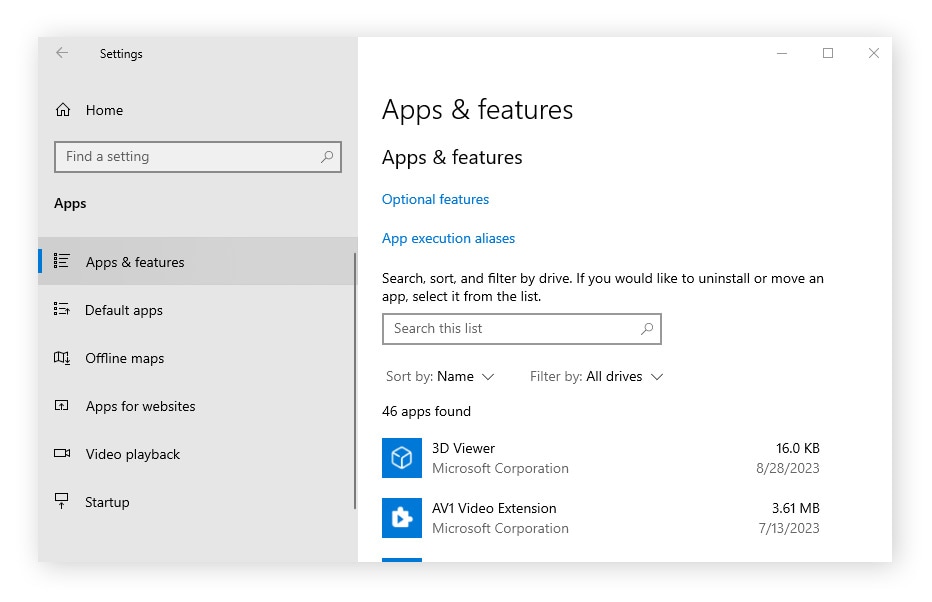
- Manually remove the malware: If you know which program is responsible for hijacking your browser, you can simply uninstall that program manually. On a Windows PC, navigate to Start > Apps & Features. Select the program in the list, then uninstall it.
On a Mac, open a new Finder window, click Applications in the sidebar, then choose the app and uninstall it.
- Use antivirus software: Antivirus software like Norton 360 Deluxe can scan for and help remove malware infecting your device. It can also help keep your browser hijacker-free by helping to prevent you from connecting to malicious sites and blocking malicious downloads.
How to prevent browser hijacking
As they say, prevention is the best cure, and the same logic applies to your digital hygiene. Follow these tips to keep your device safer from browser hijackers and other malware :
- Keep your software up to date: Regularly update your apps, other programs, and device to the latest software versions. This will help patch vulnerabilities and eliminate any weaknesses in older versions that hackers can exploit.
- Avoid suspicious links and attachments: Never click a suspicious link or email attachment from an unknown source, as this can install a browser hijacker or other malware onto your device.
- Use caution when downloading software: Always install apps and programs from legitimate marketplaces that verify apps in their stores, such as Microsoft Store, Google Play, or the App Store. Or go websites you trust and download their software directly.
- Avoid freeware: Free software may come at a cost. Browser hijackers can be bundled into free software and infiltrate your device without your knowledge or consent.
- Use a secure browser: Use a secure browser like Norton Secure Browser that is built with security and privacy at the forefront.
- Use antivirus software: Trusted antivirus software can block dangerous downloads, helping prevent browser viruses and malicious infections from making their way onto your device.
Steer clear of browser hijackers
Norton 360 Deluxe helps to block dangerous downloads and prevent you from connecting to malicious websites. Plus, it features a built-in VPN to encrypt your connection and secure the data you send and receive online.
Get a safer, more private browsing experience and help prevent browser hijacking, viruses, and other malware with Norton 360 Deluxe.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.







Want more?
Follow us for all the latest news, tips, and updates.