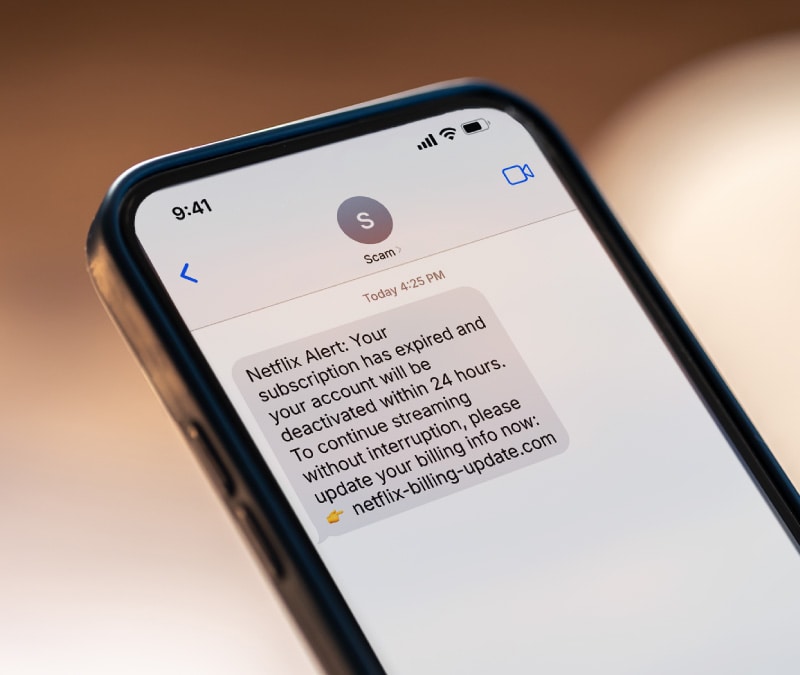
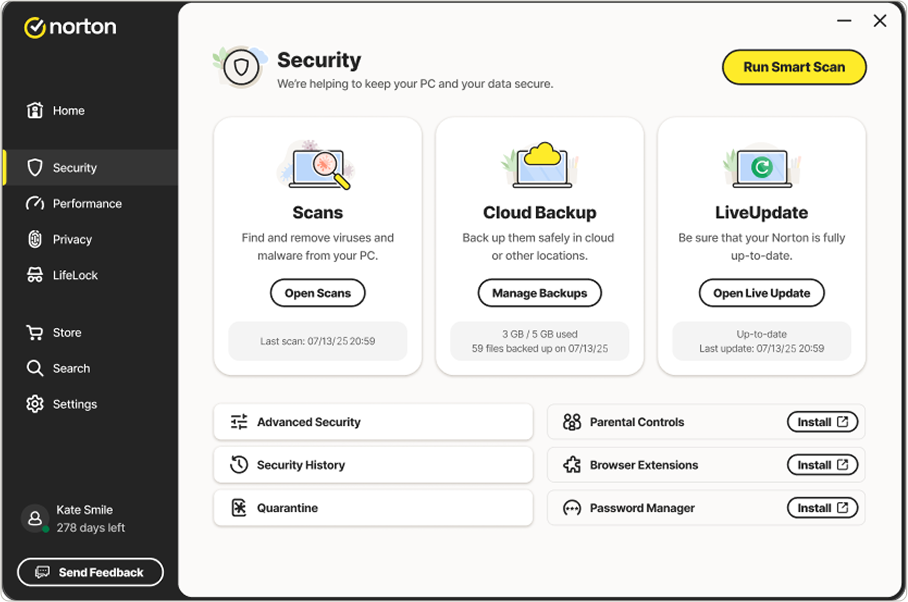
New scam alert: Scammers using calendar invites to push fake Norton subscriptions
Learn how the new calendar scam works and how scammers use fake invites to push false Norton subscription charges. See how to spot the signs and protect yourself.
Published December 15, 2025







































































































































Want more?
Follow us for all the latest news, tips, and updates.