14 ways to avoid vendor fraud and other precautions for a cyber-safe wedding
Vendor fraud can pose a real threat to your wedding. Learn how to avoid it and other risks for a Cyber Safe wedding.

Spring has sprung and it is officially almost wedding season. While blushing brides and grooms are ramping up to exchange their vows, online predators are saying “I do” to making a quick buck off the happy occasion. The icing on the cake? These cyber scammers just might be hiding in plain sight — as your vendors!
Vendor fraud is a very real threat — and one that can set you back a lot of money (bye-bye, deposit!) so it’s important to be cautious and do your due diligence while wedding planning.
With the whirlwind of emotions leading up to your wedding, there’s a lot to keep in mind. Cross off one item on your to-do list by understanding what vendor fraud is. Doing so can help you vet your vendors and feel confident footing the bill.
What is vendor fraud?
Vendor fraud involves a fraudster manipulating payment systems for illegal personal gain. In the case of weddings, this would be a scammer posing as a DJ, florist, wedding planner, or photographer who asks you for money (usually in the form of a deposit) with no intention of providing services.
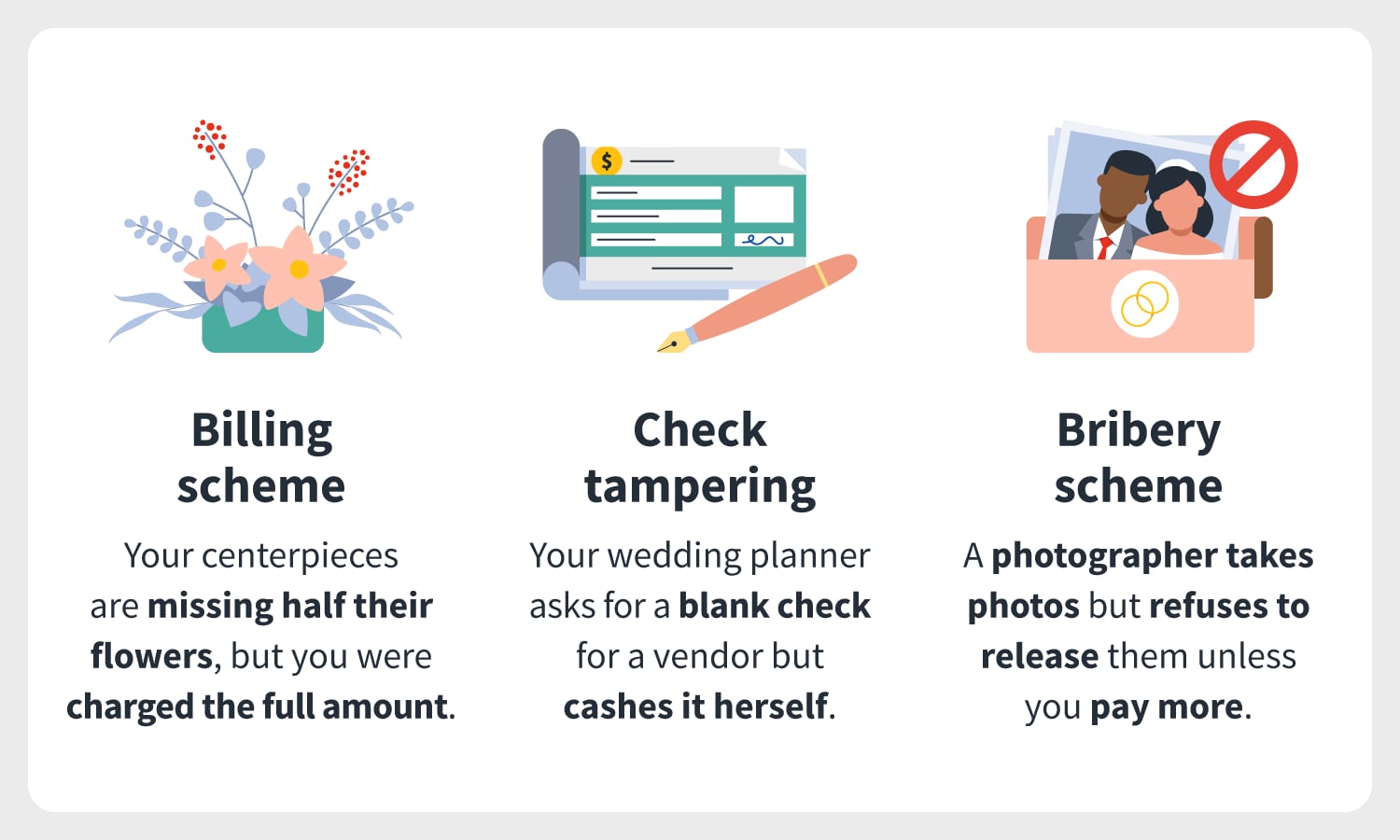
Vendor fraud generally falls into three types of schemes: billing schemes, check tampering schemes, and bribery or extortion schemes but they may blur the lines when it comes to your wedding. We’ll provide examples of what each scheme might look like amid the wedding planning process.
Types of vendor fraud + examples
Explore the following schemes to watch out for when shopping for vendors.
Billing schemes
In a billing scheme, a fraudster creates a false invoice or alters a valid one in order to trick you into making a false payment. For example, a vendor might ask for a deposit, provide a false invoice, and then bill you without ever providing the services.
While this is just one example of a billing scheme, couples can run into all kinds of vendor issues, whether it's fraud, negligence, services not as described, last-minute cancellations, or businesses going under.
In addition, couples might experience problems with vendors that are not always directly related to money. For example, you could receive cheaper flowers or notice last-minute menu changes from your caterer indicating costs were cut.
Two common types of billing schemes are fictitious billing and duplicate invoice payments.
Fictitious billing
Fictitious billing is where a fraudster will create a fictitious vendor for the purpose of committing fraud, which bills you for payment. This can be accomplished by any type of vendor from a videographer to a wedding planner — all they need is a fake name and a post office box.
Duplicate invoice payments
Duplicate invoice payments are where a fraudster manipulates the account of a legitimate vendor, causing double payment or legitimate invoice. The fraudster then sends the payment to a bank account under their name. This scheme can also be called overbilling where a vendor pads invoices to charge for more services than delivered or charge a higher price than agreed.
Check tampering schemes
Check tampering schemes occur when a vendor physically alters checks so that they are deposited into other accounts under their control. These types of scams can be done through forgery, altering payee information, or issuing inappropriate manual checks.
One common scenario is among wedding planners. They will ask for a couple of checks written out for a specific amount but without filling in the payee because, you are told, it’s up in the air as to who’s going to be booked. The scammer cashes all the checks, no one is hired, and you’re left without a wedding planner, vendors, or your cash.
Bribery or kickback schemes
Bribery or kickback schemes differ slightly from the other types of vendor fraud, as these are seen more commonly between vendors. Bribery or kickback schemes include the offering, giving, receiving, or soliciting of a thing of value to influence a business decision.
For example, your wedding planner might receive a kick-back for recommending you to a certain vendor’s business, charging you a higher price for services. Another common twist is for your photographer to show up and take pictures but refuse to release photographs afterward unless you pay more money.
How to recognize vendor fraud
Now that you understand the different vendor fraud schemers that might be trolling the web, you can learn mechanisms for identifying and preventing vendor fraud from happening to your wedding.
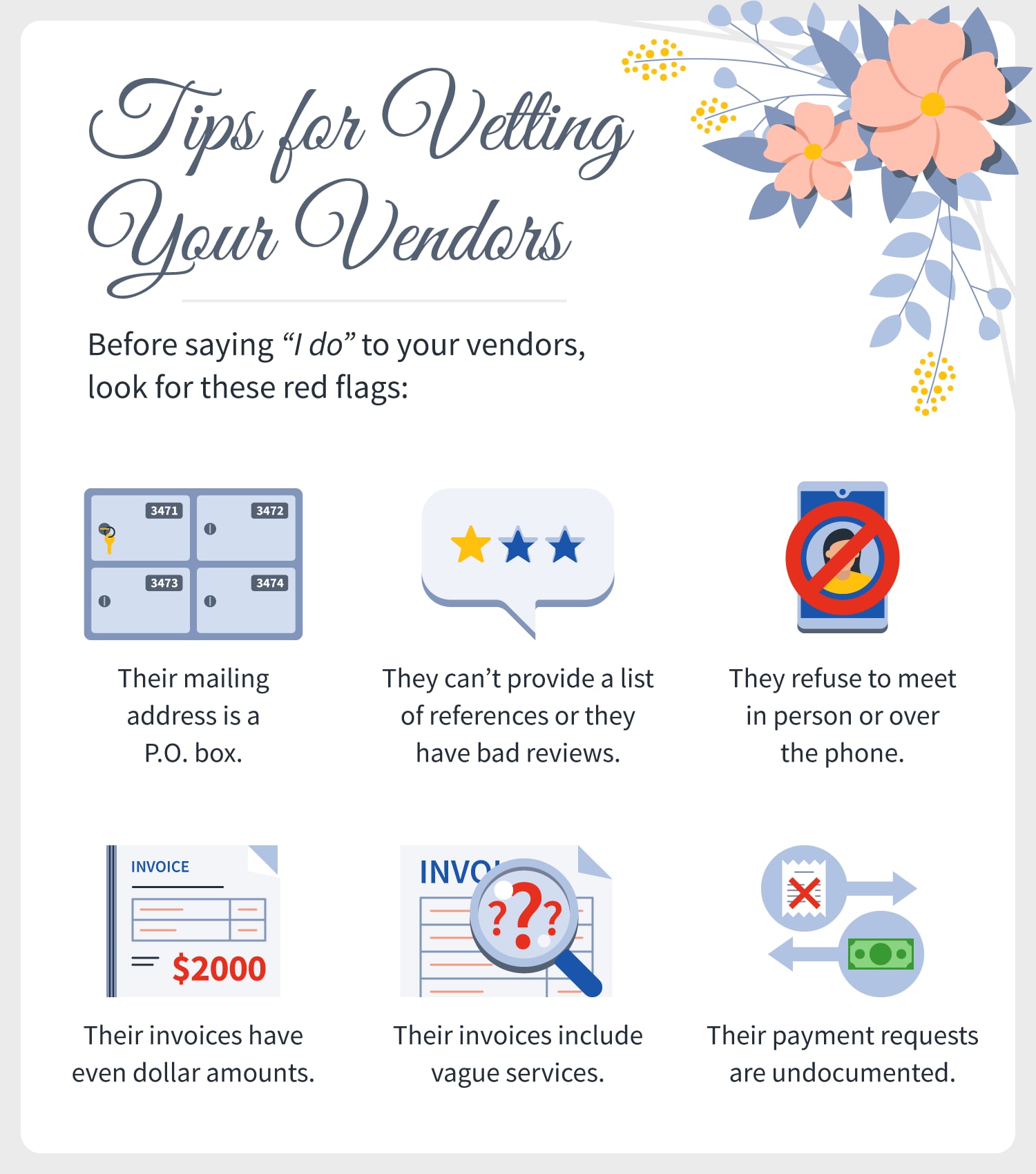
During vetting mode, note everything from their website to how they request transactions. “Some of the red flags to look out for that might clue you into wedding vendor fraud is the vendor's fee and fee structure,” Leah Weinberg, of Color Pop Events, says. If a vendor's pricing seems incredibly low and too good to be true, it probably is.”
Shannon Tarrant, owner of Wedding Venue Map, recommends being especially cautious with anyone who asks you to pay 100% upfront or offers you a discount to do so. “Companies that only take cash or checks or ask for payment in full upfront leave zero protection for the consumer if they were to go out of business or close,” she says. If in this situation, she says, “Consider asking the question of how many weddings they have booked for the next 18 months and compare that to other vendors in that category. ... If the number seems very low, that can be a red flag.”
Attorney Mark Schondorf of Hecht Schondorf LLC echoes Tarrant’s sentiment, saying one of the best ways to recognize vendor fraud is checking the legitimacy of the company. "If the vendor is an LLC or corporation, look them up on your Secretary of State website and find out when they were formed,” he says. "If your state identifies officers of the LLC or corporation, research those people or other entities they owned.”
Scam artists will often start a company, and when they are found out, they'll just create another one. Schondorf says “There may be bad reviews of those old companies, which can clue you into whether a vendor is legitimate."
In terms of preventing your wedding from being a victim of vendor fraud, expert planners recommend booking vendors with years in the business, a lot of connections, and most importantly, referrals. Dezhda “Dee” Gaubert, owner of No Worries Event Planning, says, “They’re interconnected with the wedding world in your area and thus have a reputation to protect.”
If you’re “the first” in your group to get married or simply don’t know where to look for referrals, Gaubert says “venues routinely work with legit, reliable, above-board vendors, and are great resources for referrals.”
Once you're seriously interested in a vendor, don’t stop there. Due your due diligence to ensure you are protected both on your end and on theirs if the deal for some reason were to fall through.
Consider paying for everything you can with a credit card if possible. “Your credit card company guarantees your purchases from fraud or companies going bankrupt," Gaubert says.
Lastly, make sure to ask if a vendor has business liability insurance and a business license. “You can even ask for proof of this before hiring them,” Gaubert says.
Below are a few more ways you can successfully vet vendors for vendor fraud:
- Look for vendors whose mailing addresses are P.O. boxes.
- Ask for a list of references who can verify the vendor’s legitimacy.
- Make sure you are confirming your leads are real people.
- Look for invoices with even dollar amounts or no taxes added.
- Flag invoices for vague services or services that don’t seem necessary.
- Look for payments without supporting documentation.
- Look for drastic changes in prices, services, or products provided by a particular vendor.
The importance of saying “I do” to cybersecurity
Vendor fraud isn’t the only type of cybercrime you need to be aware of when planning your wedding. 92% of brides-to-be are checking off virtual to-do lists via their smartphones and other digital devices making planning tools a breeding ground for hackers and cyber scammers. From wedding dress shopping to live streaming your wedding, there are different moments in your wedding journey where you might be at risk.
14 ways to plan a cyber-safe wedding
Most couples know that the wedding journey is a long one, as the planning process alone can take anywhere from 12 – 18 months. We’ll walk you through the different ways to stay cyber-safe while enjoying and planning every chapter of your wedding. From preparation to jet-setting on your honeymoon, we’ll offer tips for being cyber-safe every step of the way.
During pre-wedding planning
During wedding planning mode, you are most likely researching gowns, tuxes, and various vendors, sharing announcements, managing registries and creating personal websites. Keep the following tips in mind for safe and secure wedding planning.
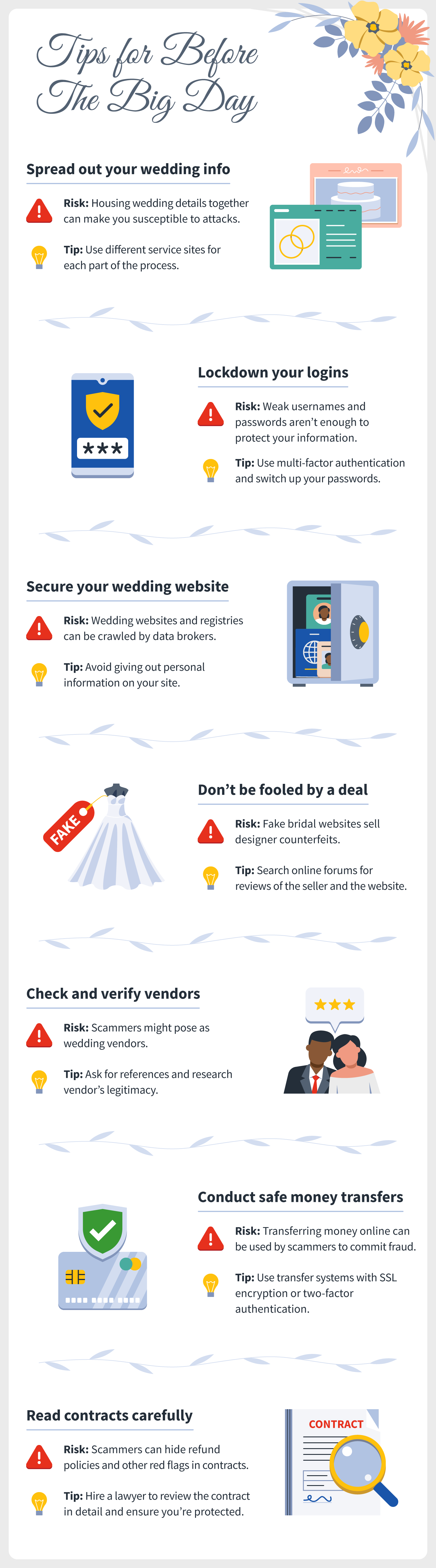
1. Spread out your wedding information
It’s a good idea to use more than one site or tool to plan your wedding. A single, centralized tool could make you vulnerable to cyberattacks. If one vendor gets compromised by a cybercriminal, it could mean your connected information (name, phone number, address, etc.) could be exposed as well. Make sure that your personal information isn’t a one-stop-shop for cybercriminals by using different service sites for each part of the process.
2. Lockdown your logins
During wedding planning, you have so many different devices, accounts, and digital tools that you are using to keep track. Usernames and passwords aren’t enough to protect your wedding details and you could be risking your family and friends’ contacts, your credit card information, and various social media platforms’ information.
Here are a few tips for securing your logins:
- Use multi-factor authentication: Multi-factor authentication can help fortify your online accounts by enabling the strongest authentication tools available, such as biometrics, security keys or a unique one-time code through an app on your mobile device.
- Practice good password hygiene: Using the same password for longer periods could put your information at risk if a data breach occurs so change account login passwords every month or two.
- Make better passwords: A strong password is a phrase or sentence that is at least 12 characters long. Focus on positive phrases that you like to think about and are easy to remember. Use a combination of upper- and lower-case letters and spaces, too.
- Pick a different password for each account: Having separate passphrases for every account helps to thwart cybercriminals.
3. Secure your wedding website
Like any website, your wedding website and registry could fall victim to being crawled by data brokers. Data brokers collect every single piece of data that they can about individuals, connecting the dots to build robust consumer profiles. They then make money by reselling the data they compile.
There are a few ways to fight back against the sale of your data to third-party data broker sites, including:
- Opting out of information collection and publication on registry sites
- Not giving out your personal information on your wedding site
- Use a burner email address
4. Don’t be fooled by a sweet deal
Cost-cutting brides can find themselves intrigued by websites promising replicas of couture dresses at affordable prices. These types of websites use original designers’ photos and trademarks to mislead brides who think they’ve found a designer gown at an incredibly steep discount. These shady businesses ship about 600,000 knockoff dresses to the United States every year, according to the American Bridal and Prom Industry Association—with some customers never receiving a dress at all.
Here’s how to avoid this scam:
- Search online forums such as SiteJabber.com for reviews of the seller and the website.
- Check the dress designer’s website to see if the seller is listed as an authorized dealer.
- Check prices with multiple sellers. If it sounds too good to be true, it probably is.
- Check the website’s sales agreement to see if there are no terms or conditions. This can make it exceptionally hard to get a refund, particularly if the seller is based overseas.
5. Check and verify your vendors
Wedding sellers aren’t the only type of vendor to watch for. Fake photographers also seek to benefit from vendor fraud. These scammers may offer what appears to be professional photography services through websites with stolen or stock images. They ask for payment upfront and then disappear with your money.
It’s wise to check out all of your vendors from catering to your wedding planner.
Here’s how to avoid this scam:
- Check your vendor to see if they have an actual business location or if they have a P.O. box.
- Vet vendors before hiring them—ask friends for recommendations and look for online reviews.
- Email questions following up and see how quickly you get a response.
- Ask vendors for references and call them. If they can’t provide references, don’t trust them.
- If they ask for a hefty deposit (over 50%) they might be a scam.
- Ask vendors to sign a contract before providing a deposit. Never wire money to someone you’ve never met!
Other similar online scams to be aware of are ads for wedding expos. Scammers will create fake websites claiming to represent big wedding expos. The “event organizers” will require payment in advance to register and you later find out that the expo doesn’t exist.
6. Conduct safe money transfers
Once you’ve vetted your vendors, it’s important to make sure you conduct any money transfers safely.
Transferring money online can be a secure way to pay vendors but can also be used by scammers to commit fraud. There are several measures that money transfer service providers and banks use to secure the movement of money on their platforms from the sender to the recipient.
Here are the things to check for before sending money transfers:
- SSL encryption: SSL or “secure sockets layer” is a form of encrypting data when it is being sent to and from a website. This keeps attackers from accessing that data while it is in transit.
- Two-factor authentication (2FA): Two-factor authentication (2FA) is an extra step added to a log-in process, such as a code sent to your phone or a fingerprint scan, that helps verify your identity and prevent cybercriminals from accessing your private information.
- Industry Data Security Standard (PCI DSS) compliance: Providers who accept, store and process card payments need a PCI compliant data hosting platform. This ensures cardholder data is not compromised thus curbing identity theft.
- Verified by Visa: This is an authentication protocol protected by passwords used to confirm the identity of a Visa cardholder. This applies to providers accepting Visa-branded debit cards or credit cards.
- Mastercard SecureCode: This is an SMS-delivered one-time-password generated by the card-issuing bank whenever a Mastercard user initiates payment using their card.
7. Review contracts in detail
Before paying or hiring a vendor, it’s important to create a contract to ensure your protection. If your vendor does not want to create a contract, that should be a red flag.
If your vendor provides the contract, make sure you are reading it entirely before signing. If you have questions about it, ask! Otherwise, you might be putting yourself at risk for any hidden red flags like cancellation policies or change orders. If you can’t explain the contract in plain English to a friend, then you most likely don’t understand it enough to sign it.
When in doubt, hire a professional to review the contract in greater detail to ensure you’re protected from any potential pitfalls. They will guide you through making changes to any language you don’t agree with and ensuring your protection if for any reason they are a no-show, don’t provide services agreed upon, and so on.
Day of the wedding and post-wedding
The big day is here, and so might be cybercriminals lurking on public Wi-Fi networks or trolling on social media. Follow these cyber-safe tips for safe digital etiquette the day of and time after your wedding.
8. Have a backup plan
It's safe to say that most vendors aren't dishonest and want to make your wedding the event you've always envisioned. That being said, it’s best to have a backup plan if one (or more) of your wedding vendors is a no-show or doesn’t provide the services agreed upon.
Here are a few items to have on your backup plan:
- Refer to the contract: If the vendor you hired didn’t fulfill their duties, what are they going to do to ensure your wedding isn't interrupted.
- Ask for your vendor’s backup plan: Do they have extra team members or products they can send out should you need them?
- Consider other options: If for some reason, there was a miscommunication on scheduling or a vendor is stuck in traffic, you might need to consider other options. Perhaps a friend has the authorization to be an officiant or a family member can step in as DJ—it doesn’t hurt to have alternate options prepared.
- Get wedding insurance: Wedding insurance can cover you for unexpected financial losses resulting from various circumstances, including unexpected illness, cancellation, and the theft of wedding gifts.
9. Live stream safely
Whether you are live-streaming your wedding due to social distancing or just want to include a relative who couldn’t make it, be sure to practice safe streaming. Do not release personal information while streaming and make sure to avoid streaming on unsecure networks. Instead, use a virtual private network (VPN).
10. Be wary of Wi-Fi
Be wary of using your venue or surrounding area’s Wi-Fi. Using an unsecured Wi-Fi connection, an attacker can capture your account’s user ID and passwords, log the data of online traffic accessed on your phone and launch a spam or malware attack on your device.
Do not transmit personal info or make purchases on unsecure networks. Instead, use a virtual private network (VPN) or your phone’s cellular connection as a personal hotspot to surf more securely.
11. Think of your guest’s privacy
Be mindful of your guests’ privacy before posting any pictures and videos of your wedding. Delete less flattering photos or photos that they might not want others to see.
12. Think before you post
While you are on your honeymoon, you may be tempted to share the beautiful resort or adventure you and your new partner are embarking on. Be sure to not share your location or pin your coordinates on social media as doing so can alert criminals of where you are (and more importantly where you are not). If you don’t want to worry about these types of crimes, simply wait until you get back from your honeymoon to post any pictures.
13. Deactivate wedding websites and registries
After your wedding, don’t forget to delete or deactivate any websites or registries online. Many popular wedding planning websites allow you to easily delete your account through an account management page. If you're not ready to delete your whole account, you can remove your wedding website from online search results by making a simple change in your account settings. Be sure to do a site search to double-check that your site was successfully deleted.
14. Spend safely
Lastly, when celebrating your newlywed status, you may be eager to spend some of your wedding gift cash. Be sure to shop or bank only on secure sites. Web addresses with “https://” or “shttp://” mean the site takes extra security measures. However, an “http://” address is not secure.
Check your wedding list once and your vendor list twice to ensure you are planning a cyber-safe wedding and are protecting yourself online.

Cyber threats have evolved, and so have we.
Norton 360™ with LifeLock™, all-in-one, comprehensive protection against viruses, malware, identity theft, online tracking and much, much more.
Try Norton 360 with Lifelock.
Editors’ note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.





Want more?
Follow us for all the latest news, tips, and updates.