What is SIM swapping and how to prevent it
Using SIM swap attacks, cybercriminals can intercept 2FA codes and password reset texts, potentially allowing them to hijack your phone number to take over your accounts. Sounds like a nightmare, right? Learn how to reduce your vulnerability and get Norton 360 with LifeLock Advantage for phone takeover monitoring and real-time scam protection.

If a scammer manages to get hold of your phone number, they can do some serious damage. With access to codes sent through two-factor authentication (2FA) systems, they might be able to access your bank accounts to withdraw your funds, make fraudulent credit applications in your name, or impersonate you on social media.
And these aren’t small-scale scams, either. A cybercrime gang was recently charged with stealing more than $800,000 worth of crypto from victims using SIM swapping attacks.
Understanding how SIM swapping works and, more importantly, what steps you can take to defend against SIM swap scammers, gives you a better chance of staying in control of your phone number and, by extension, your money.
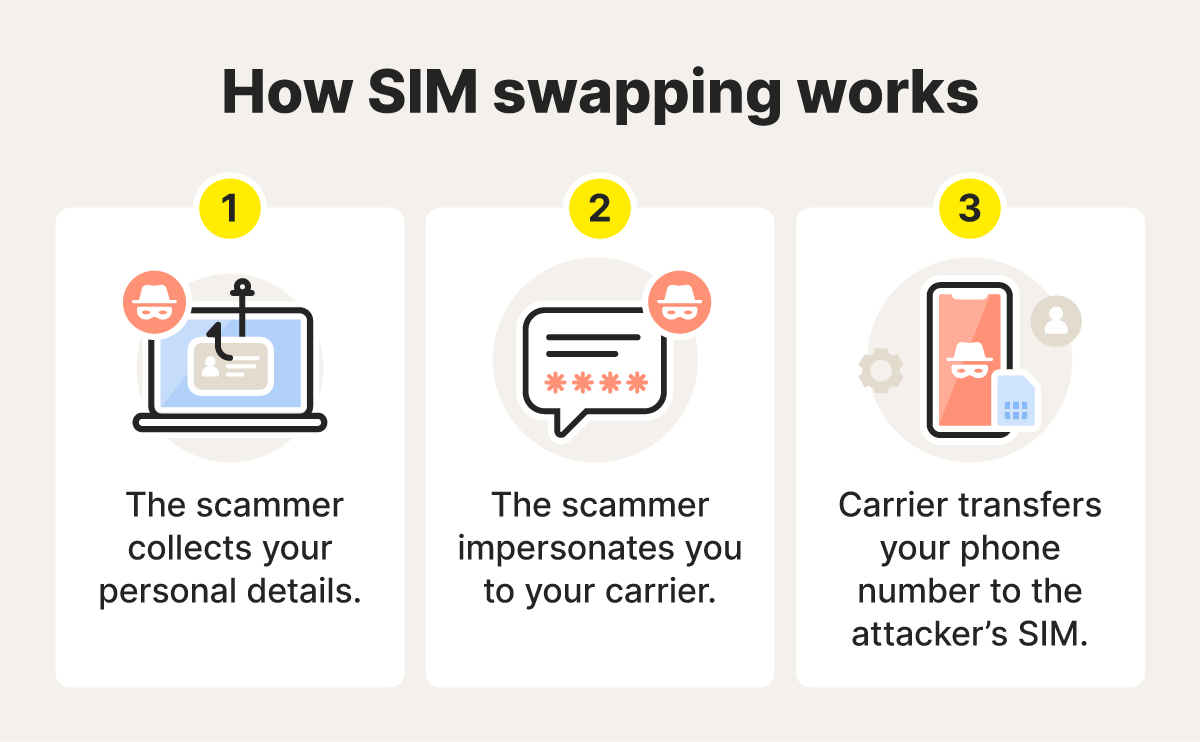
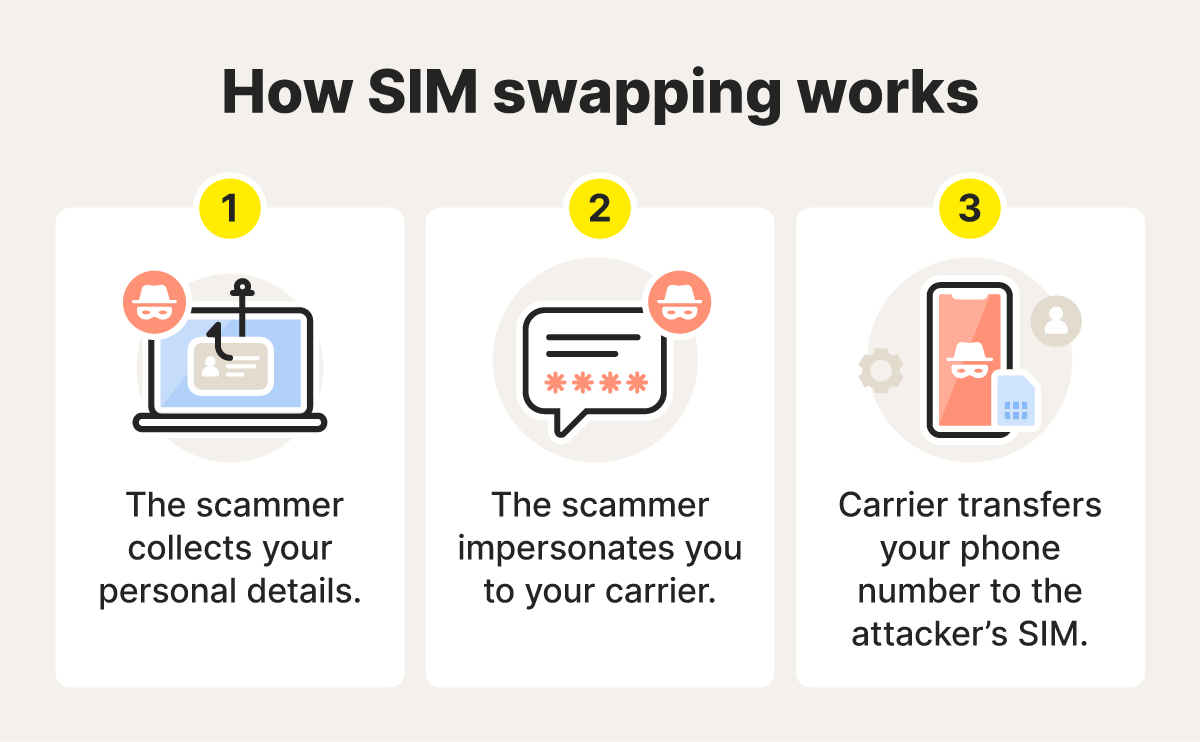
How does SIM swapping work?
SIM swapping is a process where a criminal tricks a mobile carrier into transferring a victim’s phone number to a new SIM card that they control. The scammer can then trigger 2FA or password reset codes to be sent to the number, helping them access bank accounts, steal information, and commit fraud. In 2024, the FBI reported that nearly $26 million had been lost to SIM swap attacks.
Here’s a step-by-step walkthrough of how SIM swapping scams work:
1. The scammer gathers your personal information
The first step in any SIM swap attack is gathering a victim’s information. For a scammer to pose as you when contacting your phone carrier, they need to know certain personal information, such as your name, address, date of birth, and maybe even your Social Security number.
To obtain this sensitive data, they often use social engineering and phishing tactics, convincing you to hand over your information willingly. For example, a scammer might contact you posing as your health insurer, claim there’s an issue with your coverage, and ask you to “verify” your personal details to resolve it. But even people who are careful about phishing scams can be targeted if their personal information is exposed in a data breach.
2. The scammer contacts your mobile carrier
Once the scammer has gathered the necessary information, they will contact your mobile carrier. Pretending to be you, they’ll either claim they lost their phone or need to activate a new SIM card. If the carrier falls for the impersonation, they’ll transfer your phone number to the scammer’s SIM card, deactivating your SIM card and cutting off your service.
3. The scammer gains control of your phone number
Now that the scammer has an active SIM card with your phone number, they can install it on their device and begin accessing your calls and text messages. This includes gaining access to any verification codes you’ve received from banks, email accounts, and other services.
4. The scammer accesses your accounts
Provided the scammer knows your username or email address, they can click the “Forgot password” on an account, request a reset code to be sent to the associated mobile number, and receive the code to their phone. And if they do know your password for an account, they can get through the 2FA process for immediate access.
However they get into your account, they can then reset your password to lock you out. They can then change account details like the associated email address, steal information they can use in fraud or identity theft, or even transfer funds directly to their own account.
What happens after a SIM swap attack?
A successful SIM swap attack can have many consequences beyond financial losses, such as damaged credit and identity theft. Once a scammer has control of your phone, you may:
- Lose mobile service: A sudden loss of cell service is one of the first signs a SIM swap scammer has targeted you, indicating that your service has been moved to another SIM card. It can also be challenging to get your account fixed afterward.
- Experience account takeover: Fraudsters can access and take over your online accounts, such as social media accounts, email accounts, or financial accounts, successfully impersonating you to cause reputational or financial issues.
- Get locked out of your accounts: In addition to taking over your account, criminals can change the associated email addresses, passwords, and usernames, effectively locking you out.
- Lose money: Fraudsters with access to your financial accounts can trigger unauthorized bank transfers, make fraudulent purchases with your cards, and even steal crypto assets, leaving you scrambling to freeze transactions or left hoping your bank refunds scammed money.
- Have your credit damaged: If a fraudster gets access to sensitive information like your SSN, they could open new lines of credit, such as loans or credit cards, in your name. They’ll then fail to settle bills, damaging your credit in the long term and leaving you to dispute credit report errors.
- Have your identity stolen: With access to your online accounts, a fraudster can gather various forms of sensitive or personally identifiable information to completely steal your identity and use it in healthcare or tax fraud.
- Get hit with follow-up scams: In the aftermath of the SIM swap scam, you might receive offers for fake recovery services or law enforcement investigations, which are actually subsequent scams that turn you into a victim once again.
Some real-life SIM swap stories
In a SIM swap attack from 2025, a Florida woman suddenly lost access to her phone account. What followed were days of chaos with the fraudsters spending over $17,000 and attempting to sell more than $50,000 in stocks from a brokerage account. And while another Florida victim was able to get back $96,000 that fraudsters stole, there is no guarantee you’ll get anything back.
Even when fraudsters don’t successfully get a hold of your funds, they can still cause stress and frustration in recovering your accounts. One Reddit user described their cell phone lines being shut down, multiple attempts to access their checking and savings accounts, and hours spent on the phone with their carrier just to restore service. Luckily, no funds were lost, but recovering accounts and untangling the damage took weeks.
Signs that you’re the victim of a SIM swap
It’s important to recognize the warning signs of a SIM swap so you can take steps to shut down fraudsters’ access to your phone number — and all incoming texts and calls — more quickly, hopefully before they cause too much damage.
Here are the six key signs that you might be a victim of SIM swapping.
- You can’t make calls or send texts: Getting errors when trying to send texts or make calls can mean fraudsters have transferred your number to another SIM card and have access to your incoming messages or calls.
- You’re not getting inbound texts and calls: A sudden loss of signal and access to calling is another clear indication that your mobile service has been transferred to another SIM card.
- You’re notified of activity elsewhere: Your phone provider may notify you by email that your SIM card or phone number has been activated on another device.
- You’re unable to access your accounts: If your login credentials no longer work for online accounts like your bank and credit card accounts, it could mean they’ve been changed by someone else who has access, possibly through SIM swapping.
- You find transactions you don’t remember: Unfamiliar transactions on your statements could mean that criminals have accessed your bank or credit card accounts and used them to make unauthorized purchases.
- You receive a phone takeover monitoring alert: If you have a phone takeover monitoring tool, like the one included in Norton 360 with LifeLock Advantage, you should be notified that your number has been hijacked.
What to do if you’re targeted by a SIM swap
If you’ve spotted the red flags of a SIM swap scam and are concerned you’ve been targeted, here are the steps you can take to confirm you’re under attack, stop the scammers, and recover your identity and funds.
- Contact your mobile carrier: Call your carrier as soon as possible and ask if your number has recently been switched to a new SIM card. If it has, request that the new SIM card be deactivated immediately.
- Check your financial accounts: Log in to your online banking account to check if there are any fraudulent transactions. If there are, report them immediately. If the scammer has locked you out of your accounts, call the bank directly. Consider freezing any compromised accounts or credit cards.
- Update your passwords: Refreshing the security on any app or account that’s associated with your phone number with new, unique, strong passwords can help keep hackers out.
- Report the fraud: Consider filing a police report with your local law enforcement agency. You can also report the fraud and identity theft to the FTC, FBI, and CFPB.
- Monitor your credit: Regularly check your credit in the coming months to see if scammers tried to open accounts in your name. Dispute any fraud you find with the credit bureaus, and consider setting up credit monitoring to get automatic alerts of new changes.
The recovery process can be frustrating and time-consuming, as this couple on Reddit discovered. They spent hours on a neighbor’s phone just trying to regain access to their phone accounts. And even after getting their service back, they expect it will take weeks to reverse all the damage done, despite the scammers largely being unable to steal their money. But getting started quickly can help limit the fallout of the scam.
How to protect against SIM swap scams
SIM swapping is on the rise, with the U.K. reporting more than 3,000 cases in 2024, and the FBI reporting just shy of 1,000. To help bring these numbers down, the Federal Communications Commission now requires wireless providers to implement reliable protocols for authenticating customers before redirecting a phone number to a new device or provider, and to alert customers ASAP when a SIM card change occurs.
While providers are doing their part, there are powerful, proactive steps you can take to safeguard your accounts and protect against SIM swap fraud. From updating your passwords to setting up account alerts, here are some tips for safeguarding your SIM.
- Be vigilant: Beware of phishing emails and other ways attackers may try to access your personal data, and don’t click on links in email messages from people you don’t know.
- Secure your accounts: Boost your cellphone’s account security with a unique, secure password and strong security questions with answers that only you know.
- Use PIN codes: If your phone carrier allows you to set a separate passcode or PIN on your SIM, consider doing so. This will add an extra layer of security to your account.
- Use an authentication app for 2FA: Instead of text messages, use an authentication app like Google Authenticator. This ties account access to your physical device rather than your phone number.
- Get bank and mobile carrier alerts: Ask your bank and mobile carrier if they monitor SIM swap activity and can send alerts for suspicious account changes.
- Investigate behavioral analysis technology: Banks can use technology that analyzes customer behavior to help identify compromised devices and not send SMS passwords. Ask your bank if it offers such features.
- Ask for call-backs: Some providers call customers back to make sure they are who they say they are — an extra step that can help stop identity thieves in their tracks.
- Enable account takeover protection: This optional service offered by some wireless carriers lets you set strict verification rules for making any kind of changes to your account.
- Lock your SIM card: Both iPhone and Android users have options for locking down their current SIM card. This prevents the SIM card from being physically stolen and used in another device.
- Get phone takeover monitoring: Trustworthy Cyber Safety services, like Norton 360 with LifeLock Advantage, offer specialized tools that send alerts when suspicious activity is detected that might indicate a SIM swap. This can give you earlier warning, so you can jump into action to protect your accounts.
SIM swapping is one reason a phone number may not be the best way to verify your identity. It’s a breachable authenticator. Adding additional layers of protection could help keep your accounts — and your identity — safer.
Get Norton to help defend against SIM swaps
Norton 360 with LifeLock Advantage offers advanced security, privacy, and identity protection features to help shield your personal information.
Its powerful safeguards help you protect against scams, malware, and phishing. Plus, phone takeover monitoring alerts warn you about attempts to hijack your SIM or port your number to another carrier — helping you stay safer from SIM swap attacks.
FAQs
What is a SIM card?
Also known as a subscriber identity module, a SIM card is a small card that contains a chip that identifies and authenticates you as a subscriber to your mobile carrier’s network. This SIM card is required for sending or receiving calls and sending texts.
How can I know if my SIM card was cloned?
A sudden loss of service, alerts from your mobile carrier, and unauthorized account activity are all red flags that you may be the victim of a SIM swap attack. You should contact your carrier immediately to verify SIM activity on your account.
Does my carrier protect against SIM swapping?
Protection features may be limited and often require extra steps to set up. Some carriers offer account PINs to better protect against this type of scam. Other security features a carrier might offer include account alerts and port-out locks.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.








Want more?
Follow us for all the latest news, tips, and updates.