What is a heuristic virus and how do I remove it?
Heuristic virus can refer to malware detected by heuristic analysis or the virus Heur.Invader, which compromises a device’s security and antivirus measures.

Heuristic virus is a nickname given to the malware Heur.Invader, a virus that can disable antivirus software, modify security settings, and install additional malicious software onto your computer. Some examples of heuristic viruses include adware and Trojans.
If you’ve ever received a notification from your computer saying that a heuristic virus has been detected on your system, your first reaction was likely panic. Not only has your device’s safety been compromised with malware, but you have no idea what it is or how to get rid of it. You may have heard the word “heuristic” in school or on the internet as a way our minds solve problems quickly, but what does that have to do with a virus?
This post will clear up some understandable confusion surrounding the concept of heuristics in antivirus software and will help you not only get rid of heuristic viruses on your device, but also protect your device from future malware infections.
Heuristic virus vs. heuristic analysis
The terms “heuristic virus” and “heuristic analysis” are often confused and believed to convey the same meaning — the processes used to detect malicious code and software. That being said, the term "heuristic virus" is better suited to describe the specific virus Heur.Invader whereas heuristic analysis is an adaptive antivirus defense that discovers malicious code through educated guesses.
While some people refer to a novel virus identified through heuristic analysis as a “heuristic virus”, this can cause confusion as Heur.Invader is a specific virus that attacks your antivirus software’s heuristic analysis process.
This section will provide a deeper understanding of heuristic analysis to clarify how it is distinct from Heur.Invader and to help you feel confident using antivirus software to identify potential threats to your device.
What is heuristic analysis?
Heuristic analysis is a problem-solving method that involves following rules and making educated guesses to reach a solution. In the world of antivirus technology, heuristic analysis refers to the set of rules that antivirus software uses to detect potential malware on a device.
Let’s explore how heuristic analysis works as well as how you can use it to your advantage when hunting down malware.
How does heuristic virus detection detect a virus?
Older forms of antivirus software used a method known as signature detection to identify specific viruses. Signature detection compares computer code to a known list of viruses to identify whether a computer is infected.
However, there are now so many new viruses — more than 300 million created per year — that this method is no longer as effective at catching malware. This is where heuristic analysis comes to the rescue.
Rather than using a list of viruses as a reference to determine whether a device contains malware, heuristic virus detection spots viruses by identifying files with suspicious behavior or code infrastructure and flagging them as potentially dangerous. It does so through:
- Dynamic scanning: Also known as file emulation or sandbox testing, this process tests and analyzes a file’s behavior in a controlled environment to see if it behaves like a virus, and flags it if it does.
- File analysis: File analysis analyzes the purpose and intent of a file, flagging files with an apparent intent to do harm (e.g., delete other files).
- Multicriteria analysis (MCA): MCA determines the severity or weight of a potential threat to decide whether it’s worth flagging.
Heuristic scanning sensitivity
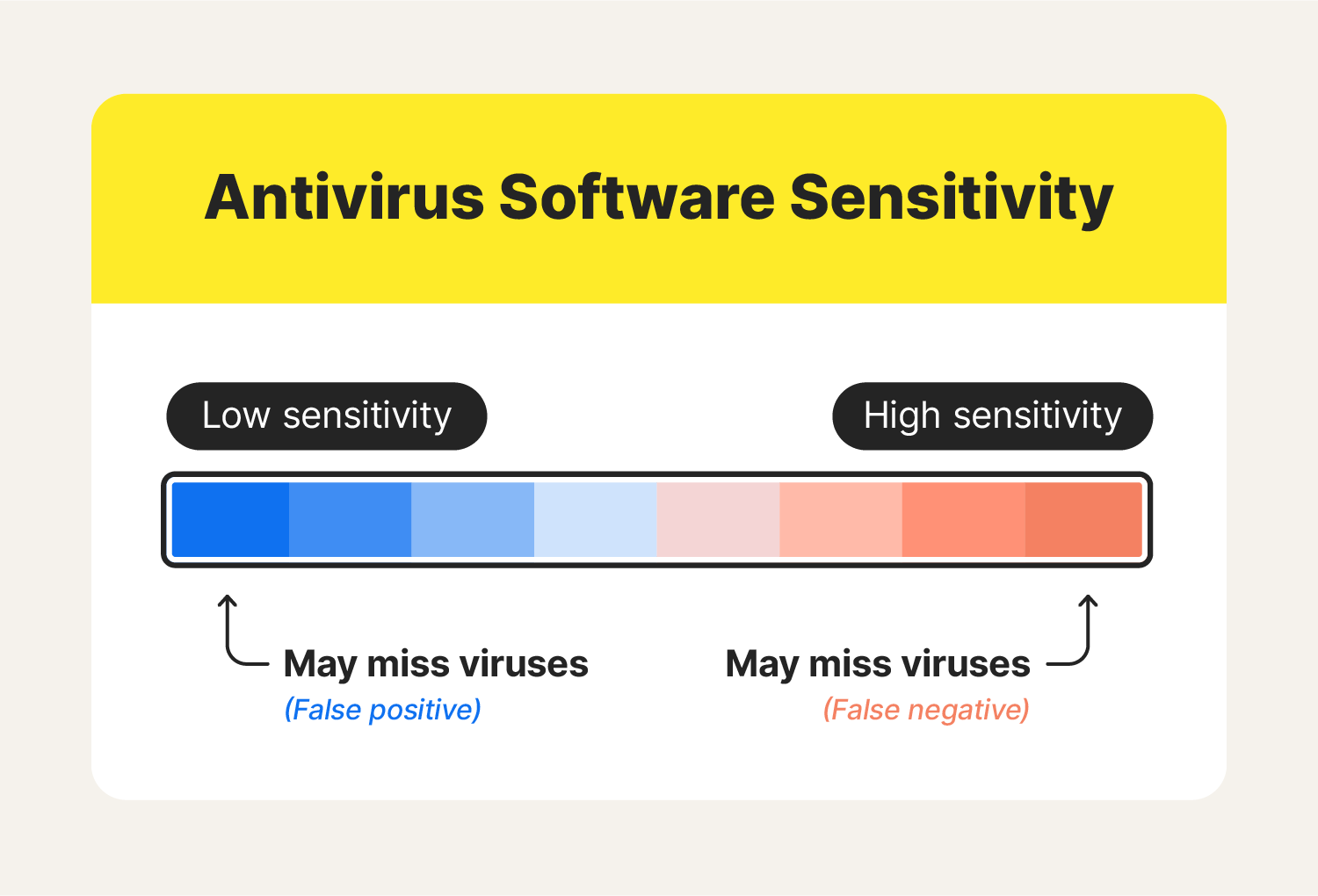
Before you run a heuristic scan to identify potential threats on your device, you may consider adjusting your antivirus software’s sensitivity levels. Higher sensitivity levels, while more likely to detect potential threats, may flag secure files as dangerous, also known as generating false positives.
Low sensitivity levels, on the other hand, will cause the software to only flag what it deems as particularly suspicious, but may miss out on some items that are slightly suspicious. It’s up to you to decide how much risk you’re willing to take on when running your antivirus program.
You can customize your software’s sensitivity level by:
- Opening your program’s settings.
- Locating scan properties and enabling Heuristic scans.
- Selecting your preferred sensitivity level.
How to identify + remove a heuristic virus
As you likely know by now, your antivirus software can be your best friend when it comes to locating and removing viruses. If you’ve been noticing some virus warning signs on your device, it might be time to scan your device for potential malware.
Some common heuristic detections include:
- Win32 Heur: A Trojan virus.
- Pup.Adware.Heuristics: A piece of adware usually identified as “Potentially Unwanted Program.”
- HEUR/QVM06.1.0000.Malware.Gen: A Trojan virus.
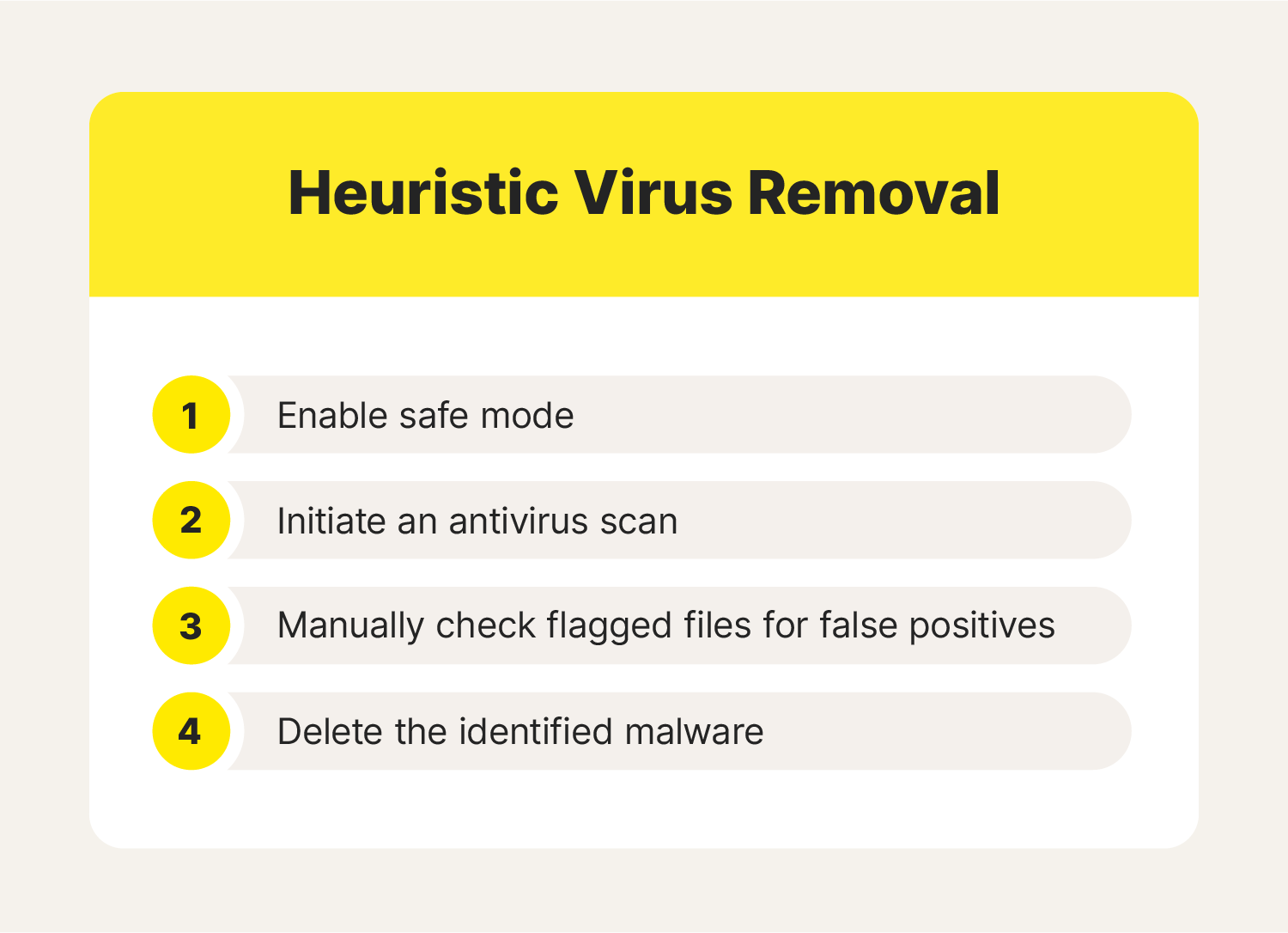
To remove Heur.Invader as well as any other malware that may be plaguing your device:
- Launch your device in safe mode.
- Run an antivirus scan using your antivirus software.
- Once your software flags certain files, don’t delete those files just yet. Manually inspect each one to ensure you don’t delete false positives.
- Remove malware from your device.
How to enable safe mode
Before beginning your antivirus scan, you’ll want to enable safe mode on your device. Safe mode allows only the most essential programs on your computer to run, keeping everything else (including most malware) disabled. This makes it much easier to remove malware that could otherwise be camouflaging or disrupting the antivirus scan.
To enable safe mode on a PC:
- Restart your PC.
- When the sign in screen appears, hold the Shift key and select Power then click Restart.
- Once your PC restarts, it will recognize you are wanting to access a new startup mode and will prompt you to “Choose an option.” Select Troubleshoot → Advanced Options → Startup Settings.
- Once the next window loads, click the Restart button and wait.
- When the startup options menu appears, select number 4 or F4 to load your PC in safe mode.
Enabling safe mode on a Mac is a bit more straightforward.
To enable safe mode on a Mac:
- Restart your Mac, then immediately hold the Shift key. Continue holding as the Apple logo appears and the bar below it loads.
- Once you see the login window, release the Shift key. Once you log in, your Mac should be in safe mode. If you are prompted to log in twice or run into any other issues, Apple provides safe mode instructions to diagnose the issue.
Once safe mode is enabled, you can move forward by running your antivirus software as usual then investigating and potentially removing the suspicious files it identifies.
5 tips to prevent heuristic viruses
Mistakes happen, and it’s nearly impossible to be perfectly safe when using the internet, but there are some best practices that will improve the chances of your devices remaining virus-free.
1. Think before you click
Everywhere you look on the internet, you’ll see prompts to click. Get into the practice of looking at a link URL before you click on it. If the site name or the URL seems unnatural, your best bet is to avoid clicking on it. Ultimately, take your time when surfing the web and trust your gut if you have any hesitancy to click a link.
2. Use unique passwords and change them often
Strong passwords that include a combination of characters, numbers, and uppercase and lowercase letters are far more challenging to hack than simple passwords such as your name followed by “123.” For the strongest protection, opt into two-factor authentication, using both a password and a text or email notification to sign into your accounts.
3. Update software regularly
Nobody likes taking the time to wait for their device to update. We log onto our computers with the intention of getting something done, and updates can feel like a waste of time. However, software updates are critical in keeping devices safe from cyberthreats.
New hacking strategies are always being invented, and applications must update with them to stay ahead of novel cyberattack strategies. Taking a few minutes to update your device and its applications will keep you safe in the long run.
If you don’t have time to download it now, set a reminder to do so when you have time to spare or even schedule the update to install overnight.
4. Periodically run antivirus scans
Viruses often go undetected. Running frequent antivirus scans is the only sure way to identify malware and nip it in the bud. Many antivirus programs offer a feature that regularly scans your device for viruses, using heuristic analysis. If possible, enabling this feature is highly encouraged.
5. Keep an updated backup hard drive
While backing up your computer’s contents won’t protect you from viruses, a backup hard drive (whether physical or in the cloud) is a great safety net in the event of a cyberattack. Try to get into the habit of backing up your computer on a monthly if not weekly basis to minimize the stress of an attack as much as possible.
Cybersecurity is a serious modern-day issue that is not to be taken lightly. Stay ahead of hackers by taking as many precautions as possible to protect yourself online, keeping your risk of acquiring heuristic viruses as low as possible.

The freedom to connect more securely to Wi-Fi anywhere
With Norton™ VPN, check email, interact on social media and pay bills using public Wi-Fi without worrying about cybercriminals stealing your private information
Try Norton VPN for peace of mind when you connect online
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.





Want more?
Follow us for all the latest news, tips, and updates.