What is scareware + how to remove it
Scareware is invasive software that tries to frighten people into performing specific actions. If you've ever encountered a "virus warning" message that urges you to download a program or file, this could be an instance of scareware. Learn more scareware warning signs to watch for and prevention tips, such as leaning on Norton 360 Deluxe to help protect your devices.

How does scareware work?
Scareware is software that tries to mislead people into performing a specific action. Cybercriminals might employ scareware to access someone else’s funds or sensitive information. They might also aim to trick people into downloading viruses or ransomware that can have long-lasting repercussions.
Scareware is a scam that can manifest as a pop-up ad for an alleged cybersecurity problem. These pop-ups try to scare users into handing over confidential data to “fix” fake cybersecurity problems. If you disable an ad blocker, you could be exposed to scareware more frequently.
Downloading scareware can result in credit card fraud or identity theft in the worst-case scenarios. But learning about some of its most common forms can reduce the likelihood of experiencing a scareware attack.
5 scareware examples
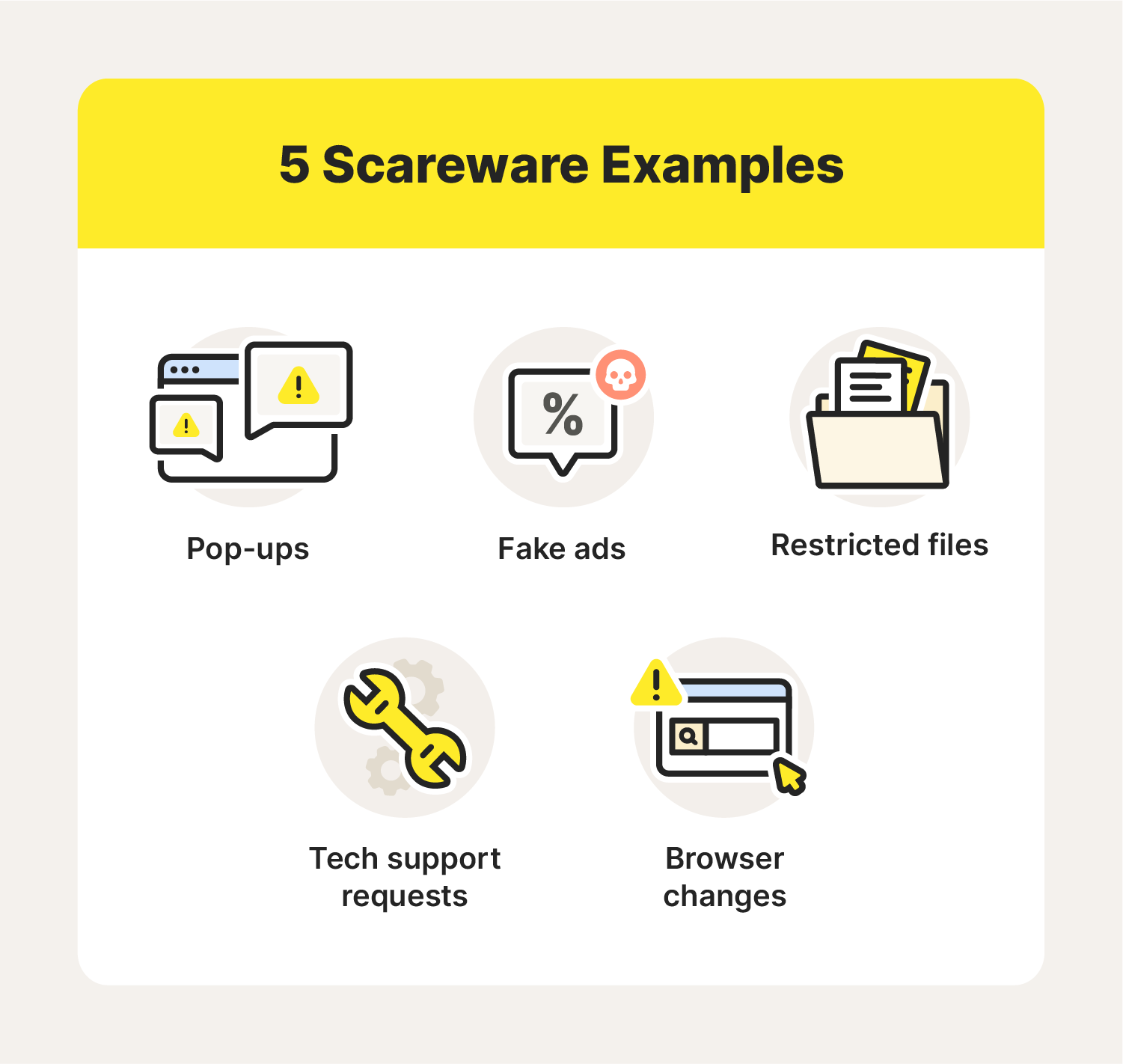
Scareware can take on multiple forms and range from subtle to more complex. While each scareware scam has its own nuances, all aim to frighten people into compromising their data. Here are five common examples you might encounter.
1. Pop-ups
Intrusive pop-up ads can disrupt your browsing session and slow your device to a crawl. The NightMare program is one of the earliest and most famous scareware attacks in internet history. In 1990, developer Patrick Evans created a program that would flash a haunting skeletal image every five minutes. Just like NightMare, many modern scareware pop-ups secretly run in the background and trigger at set intervals.
2. Tech support requests
Some scareware programs might try to scare people into believing their devices are damaged or malfunctioning. Consequently, prompts for fake tech support services might repeatedly display on screen as a pop-up window.
3. Browser changes
Scareware can alter your web browser and display “alerts” claiming your device has been infected. You may encounter this type of scareware if you connect to a hacked router that can alter your browser to redirect you to an unfamiliar website.
4. Fake ads
Fake ads are a form of social engineering, which is a tactic cybercriminals use to trick people into sharing sensitive information. Fake ads appear to promote legitimate products or services, but interacting with them can compromise your device. Some types of scareware can display fake virus alerts, so use caution if you see an ad for an unfamiliar product.
5. Restricted files
Discovering certain files on your device have suddenly been restricted may be a telltale sign that scareware is active. For example, you try to access a folder on your computer that contains sensitive documents, only to encounter a strange “error” pop-up accompanied by a link that will allegedly grant access to this folder. If you click on that link, you may accidentally download spyware, ransomware, or even more scareware onto your device.
Many scareware attacks are simply irritating, but some can be quite costly. Fortunately, you can learn how to recognize scareware before it becomes an issue.
How to spot scareware
No one wants scareware on any of their devices, so learning how to spot this invasive software is crucial. Look out for the following scareware signs while you’re web browsing:
- Dire messages: A pop-up might claim your computer is infected with hundreds of viruses, potentially using all caps and multiple exclamation points to convey a sense of urgency.
- Pressure to take quick action: Cybercriminals behind these attacks want you to purchase and install their malware quickly before you can think about it.
- Pop-ups that are hard to close: Clicking on the “X” button of a scareware pop-up might not immediately close the window, and it may open up more pop-ups.
- Unfamiliar software companies: A website with weak security might have fake ads sprinkled throughout. Watch out for ads that promote obscure companies; if it’s hard to find reliable information about them, it could be a sign of fraud.
- Performance changes: If your device is suddenly operating much slower than expected, or if it’s quickly overheating, scareware might be affecting its central processing unit (CPU).
Scareware can find its way onto your device in multiple ways. If you accidentally download scareware, it’s important to remove it from your device as soon as possible.
How to remove scareware
If you’ve experienced any of the previously mentioned scareware examples, it might be time to clean out your device. Here’s how to get rid of scareware on Windows and Mac devices.
How to remove scareware on a Windows computer
- Open Task Manager on your Windows device.
- Review all the apps running on your device and look for unfamiliar programs.
- Delete unverified programs that are taking up excessive amounts of CPU (50% or higher).
How to remove scareware on a Mac computer
- Restart your Mac and hold the “Shift” key as it boots up to enter Safe Mode.
- Complete all login prompts, then open “System Settings.”
- Click on “Storage,” then open “Applications” and delete any suspicious programs.
Exercise patience and be thorough when rooting out scareware from your devices. Once you’ve finally removed it, you’ll want to think about prevention next.
How to prevent scareware

It can take a long time to completely remove scareware from all your devices. Thankfully, you can take steps to prevent scareware attacks from occurring again.
- Don’t click on pop-ups: Scareware can install on your device if you click a pop-up featuring a link or a “download” button. Close your web browser as soon as you can—or force the browser to quit with Task Manager or Activity Monitor if the pop-up is especially persistent.
- Update your browsers: Developers release software updates to fix glitches and resolve vulnerabilities. Updating your web browsers can dramatically boost your defense against scareware attacks.
- Use pop-up blockers: Web browsers like Safari and Google Chrome let users disable pop-ups for any site they visit. You can enable or disable pop-up blockers in the “Settings” or “Preferences” tabs.
- Vet new software: The expansive catalog of free software you can find online is a double-edged sword. Research any programs you plan to use before installing them on your device—especially if payment is involved.
- Utilize cybersecurity tools: Firewalls and antivirus programs are excellent tools for eradicating malicious software. Choose antivirus software that are reliable and tailored to your needs.
Scareware attacks capitalize on vulnerabilities to be fully effective. Security products can help cover gaps in your device’s defenses and offer peace of mind while browsing the web.
No need to be scared by scareware with Norton 360 Deluxe
Protecting devices from scareware and other malicious programs takes a multifaceted approach. Products like Norton 360 Deluxe can simplify that process by offering a suite of security features, like antivirus software and protection against malware, ransomware, and hackers.
FAQs about scareware
Scareware has similarities to other types of invasive software, so it’s easy to see why people might confuse them. Here, we’ll answer a few commonly asked questions about scareware to shed more light on what it can and can’t do.
What's the difference between scareware and ransomware?
Scareware bombards users with disruptive pop-ups, but it isn’t as debilitating as other programs. Ransomware, however, can lock up a device and deny access until the user pays a specific amount of money.
What is the difference between scareware and malware?
Scareware is one of the many forms of malware you may encounter online. The term “malware” broadly refers to any form of malicious software that can infect a device.
How is spyware different from scareware?
Spyware monitors a user’s activity without their knowledge or permission and then shares that data with an unknown party. Scareware, on the other hand, aims to trick users into performing a specific task through shock tactics.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.







Want more?
Follow us for all the latest news, tips, and updates.