What is a firewall? What it does and why you need it
When hackers, bots, and other malicious traffic access a private network, they can do significant damage. That’s where firewalls come in. Learn more about firewalls and how they help protect networks against unauthorized intrusions. Then get Norton 360 Deluxe with its built-in Smart Firewall to help protect and secure your network.

What is a firewall?
A firewall is a digital security system that monitors and filters traffic over a network based on a predetermined set of security rules. Firewalls filter unknown traffic and help block unauthorized access to a network.
Firewalls, which can come in the form of physical hardware or software applications for your computer, also help protect against malware that can wreak havoc on your device and identity. The key to firewall protection is determining the breadth and depth of protection you need so you can find the best solution for your online life.
How does a firewall work?
A firewall monitors traffic by inspecting the data packets that flow between your internal and external network, or between your device and the internet. Depending on the firewall’s predetermined set of rules, traffic is either allowed, blocked, or quarantined.
Firewalls help protect against hackers, wardriving, and different types of malware like ransomware that may try to access your network and steal sensitive information. They act as gatekeepers between your computer and another network (typically the internet).
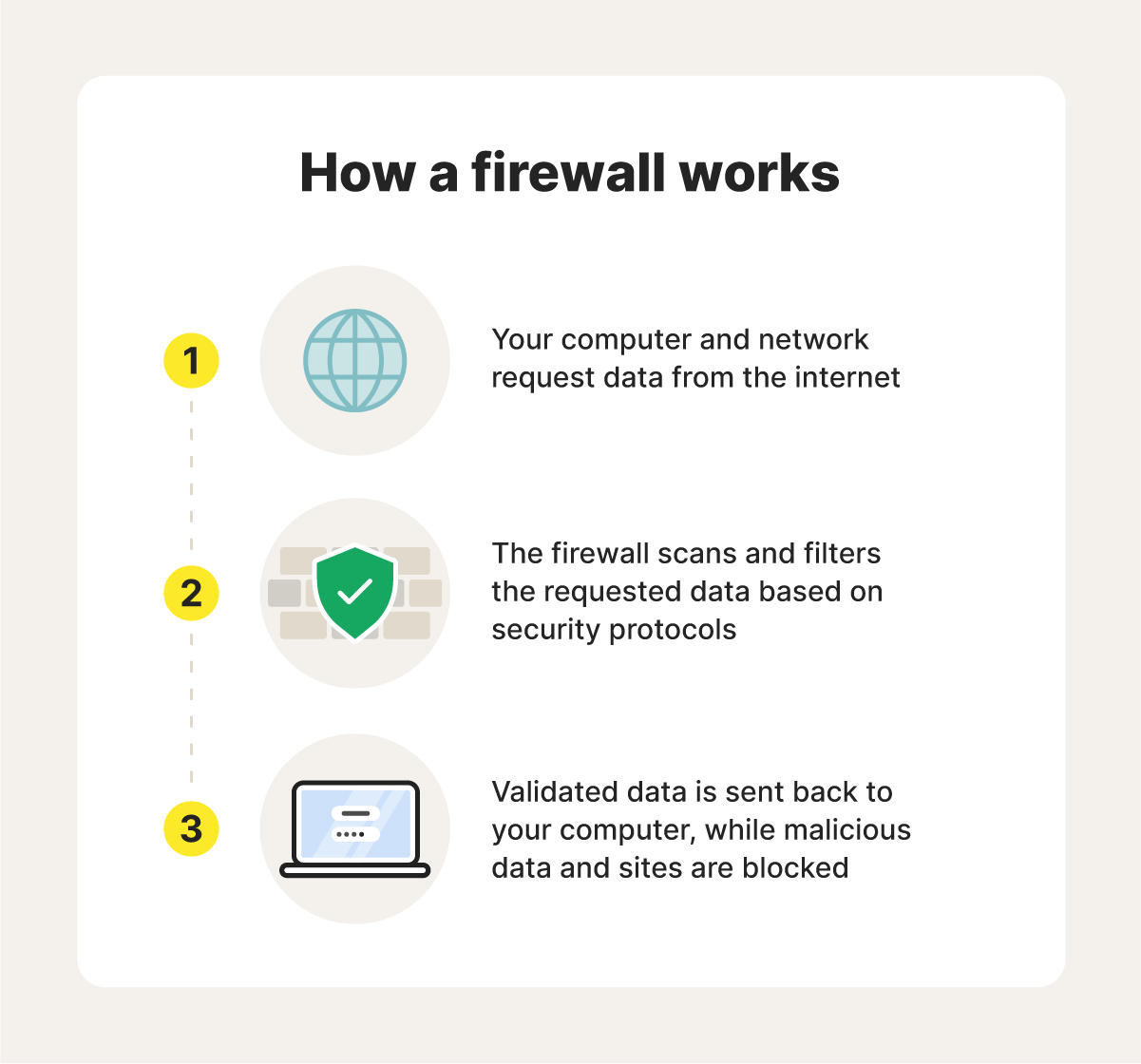
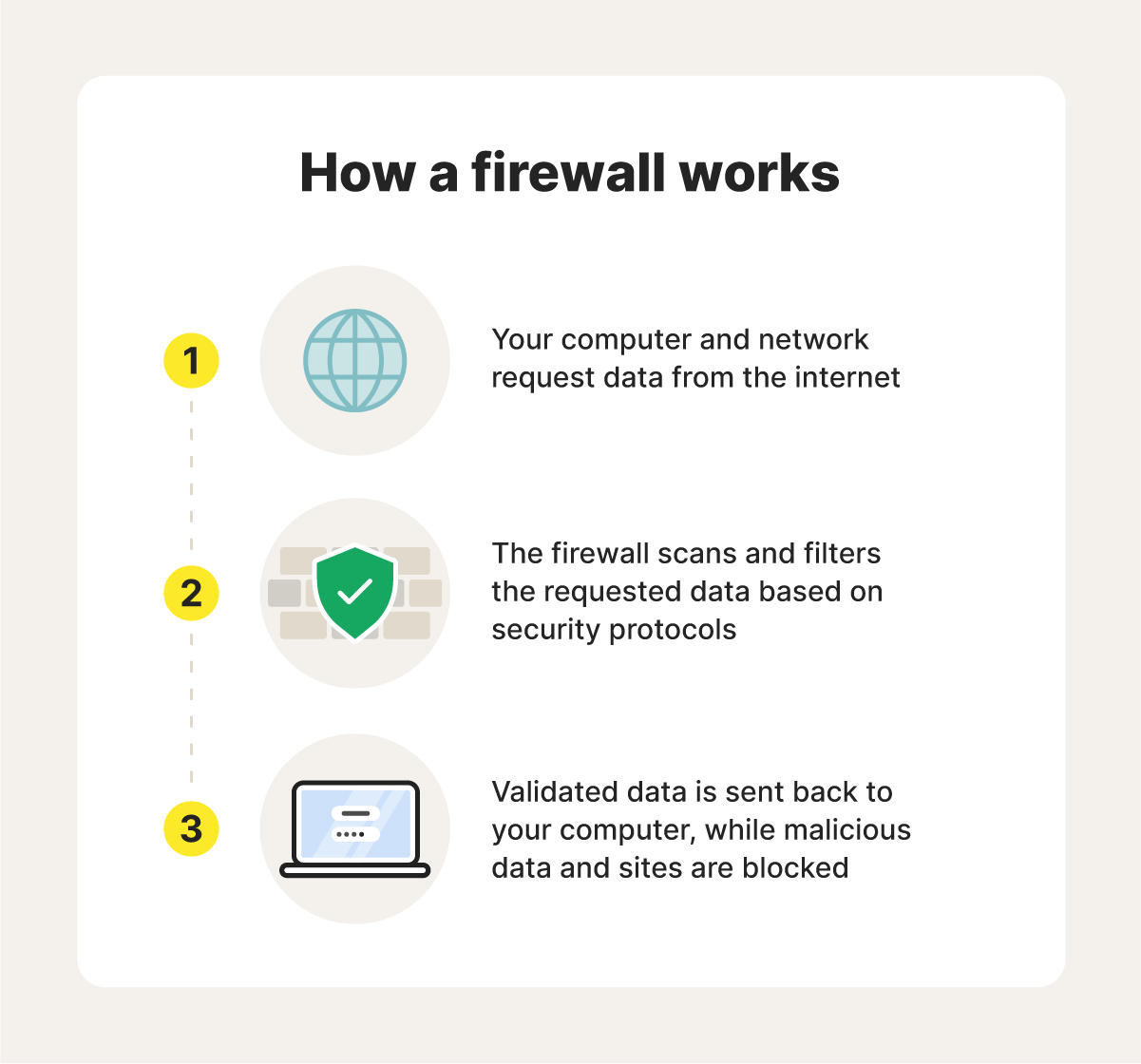
A firewall is like a traffic controller. It helps protect your network and information by managing your network traffic. This includes blocking unsolicited incoming network traffic and validating access by assessing network traffic for malicious activity.
Many devices come with built-in firewall protection. Double-check to make sure you’re getting the most out of your computer’s pre-installed firewall. A firewall isn’t a replacement for antivirus software but should be run in tandem. You should also configure your security settings to run software updates automatically so you always have the most up-to-date protection.
What about VPNs and NAT?
You might have heard about privacy measures, such as virtual private networks (VPNs) and network address translation (NAT).
- VPN: Disguises your device’s IP address and encrypts traffic over a network
- NAT: Assigns one public IP address for all devices on a network, hiding internal IP addresses from external networks
Use a VPN on your device when working at a coffee shop or on any public Wi-Fi to protect your in-transit data from sneaky hackers. Use a NAT on your home Wi-Fi to protect your family and guests who use your internet connection.
While these tools improve your privacy, you still need a firewall and security software for enhanced online protection.
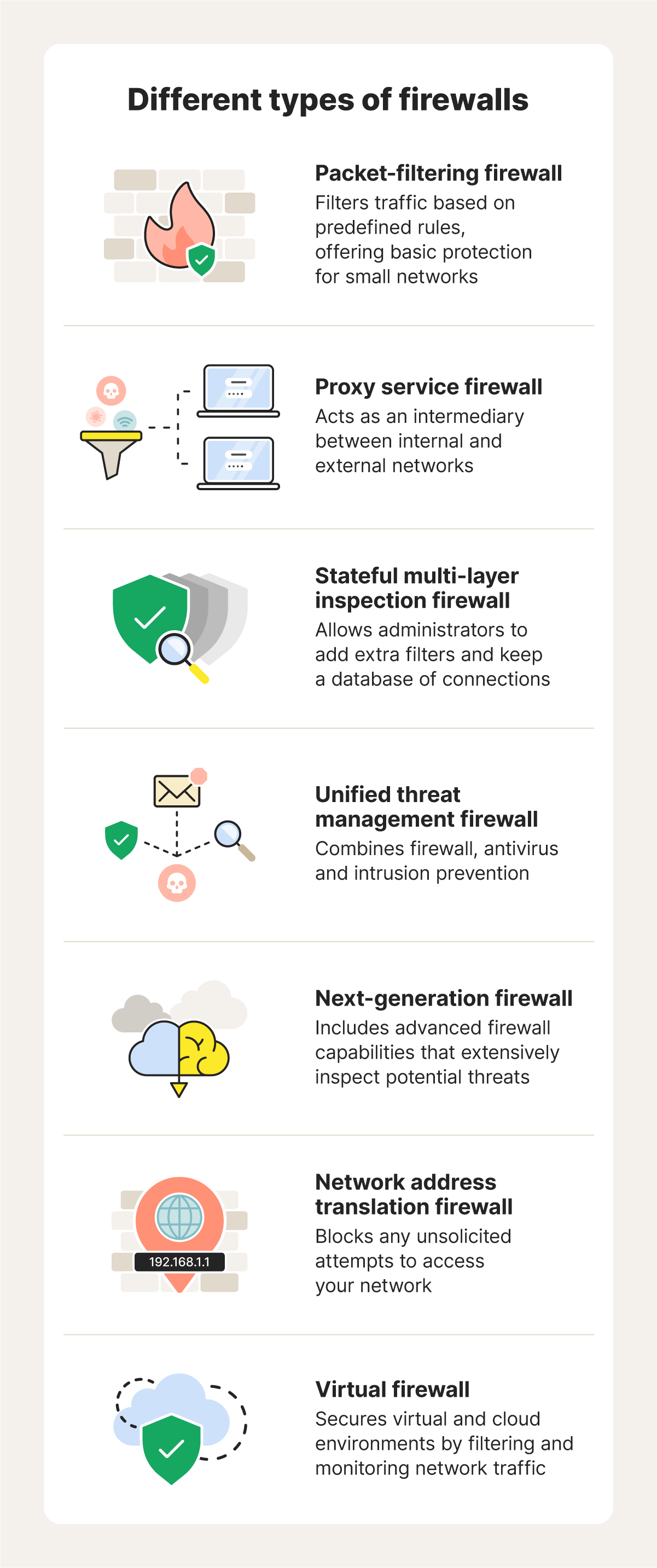
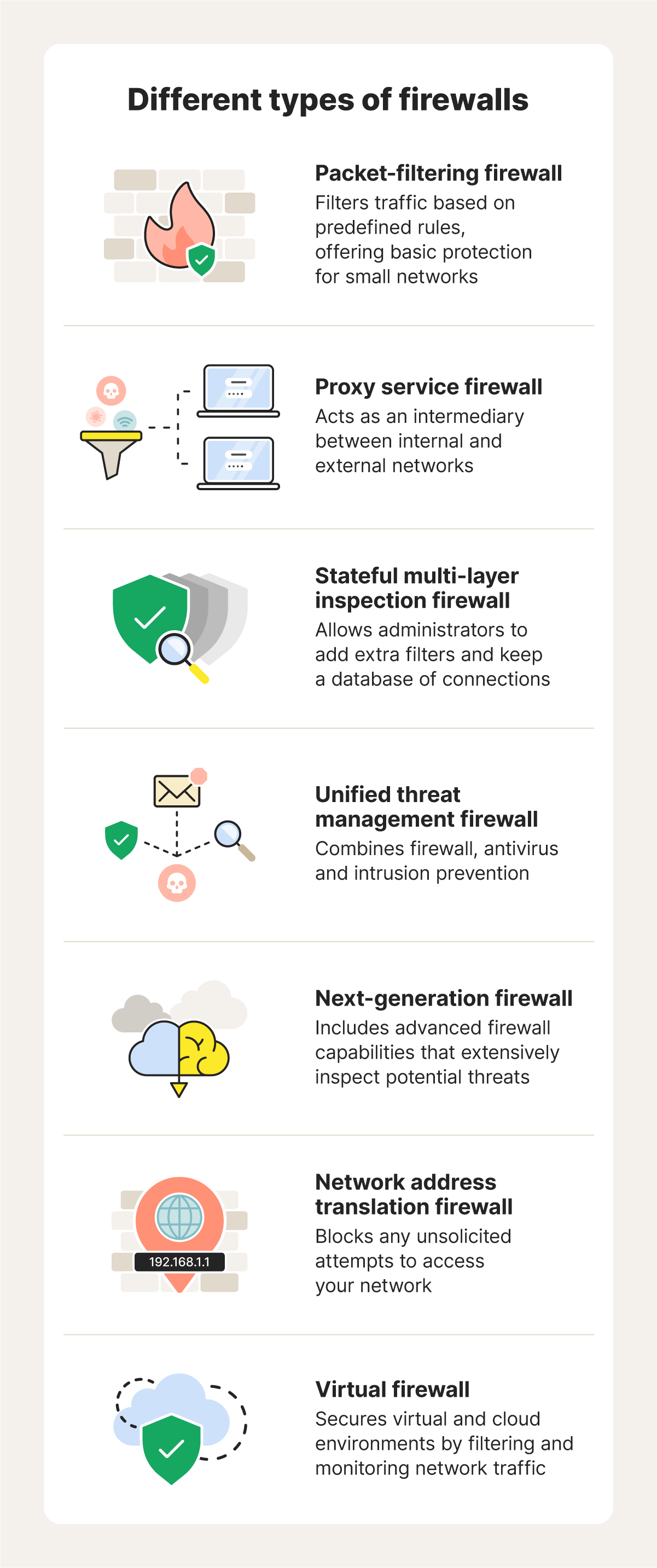
Different types of firewalls
The two primary types of firewalls are software and hardware-based. A hardware firewall protects an entire network, while a software firewall protects an individual device.
- A hardware firewall is a physical device, often integrated into a router, that sits between your network and the internet.
- A software firewall is an application installed on individual devices that controls traffic based on port numbers and application-level rules.
Here are the various firewalls you can install, depending on the size of your network and the level of security you need.
Packet-filtering firewalls
A packet-filtering firewall filters incoming and outgoing data packets based on a predefined set of rules. It can block or allow network traffic based on criteria such as the IP protocol, IP address, and port number.
Packet-filtering firewalls offer the most basic form of protection and are suitable for smaller networks, such as your home. They are simple and efficient to use, making them an excellent choice for personal devices.
Proxy service firewalls
A proxy firewall acts as a gatekeeper between an internal network and external services, processing user requests securely. Using Deep Packet Inspection (DPI), a proxy service firewall analyzes traffic for threats, blocks unauthorized access, and shields internal IP addresses.
By preventing direct connections between users and the internet, proxy service firewalls enhance security and ensure compliance with network policies, safeguarding organizational data and resources.
Stateful multi-layer inspection (SMLI) firewalls
A stateful multi-layer inspection firewall combines standard firewall capabilities with connection tracking. SMLI firewalls filter traffic using data they gather and administrator-defined rules and context. This process involves using data from prior connections and packets from the same connection.
SMLI firewalls inspect the entire packet, including the data, which contributes to their high level of security.
Unified threat management (UTM) firewalls
A unified threat management firewall is more than a single program — it combines the functions of the SMLI firewall with other services like spam filtering and antivirus software.
UTM firewalls may include additional services like cloud management. For enterprises, UTM firewalls can be a cost-effective way to manage security within a more simplified central management system.
Next-generation firewalls (NGFW)
Next-generation firewalls are more sophisticated than packet-filtering and stateful inspection firewalls. They inspect entire packets, including headers, contents, and sources, for deeper threat detection.
While highly effective, the configuration complexity of NGFW firewalls can be a drawback, requiring expertise to optimize.
Network address translation (NAT) firewalls
A NAT firewall conceals internal IP addresses by assigning devices on a private network a single public IP address, protecting them from external access.
NAT firewalls filter incoming traffic, only permitting responses to outbound requests. NAT is generally simple to set up as it’s often built into routers, making it a popular choice for home users and small businesses.
Virtual firewalls
A virtual firewall is an application used by private and public cloud-based systems. It can assess and manage internet traffic over both physical and virtual networks.
Cloud-based firewall solutions can deliver extra flexibility for businesses running cloud environments, virtualized data centers, or hybrid networks.
Why are firewalls important?
Firewalls are critical security tools because they act as a first line of network defense against threats such as malware, hacking, and unauthorized access. By monitoring and filtering network traffic, firewalls help secure online communications and protect against data breaches.
Here are the three main risks of not having a firewall:
Unauthorized network access
Without a firewall, all connection attempts to your network are accepted, including those from potentially malicious actors. This absence of protection exposes your network to potentially unauthorized access, which heightens the risk of data breaches and system compromise.
Malware and data intrusion
Without a firewall, your devices and network are more exposed to malware and unauthorized intrusions. Cybercriminals could gain control of your computer or network, potentially hacking your computer's webcam, accessing sensitive data, or downloading your system files for malicious purposes.
Network stability
Without a firewall, attackers could destabilize or shut down your network. This is especially inconvenient in an office environment or when working from home, as it can cause a loss of productivity and put sensitive business files at risk. Recovering from such a disruption can take significant time and money.
How to use a firewall
Using a firewall doesn't need to be complex. Simply install Norton 360 Deluxe and you’ll get the firewall that’s built right in.
- Sign up: Create an account and download Norton 360 Deluxe.
- Install: Install the application on up to five devices.
- Run: Launch the app and adjust your preferences.
Firewalls vs. antivirus solutions
While firewalls and antivirus solutions are critical elements for keeping your online life safer and more secure, they are not the same.
A firewall prevents unauthorized access to your computer by examining data packets and selectively blocking potentially malicious network traffic. Antivirus software keeps malware off your device by using heuristic detection methods and scanning files and websites for malicious signatures. Antivirus software can also help remove malware if it infects your device.
Protect your devices with Norton 360 Deluxe
Norton 360 Deluxe provides powerful protection against malware, hacking, and other online threats. Plus, it features a built-in firewall and intrusion detection system to help monitor your network traffic, defend against unwanted access, and block hackers and other cybercriminals.
FAQs
What does a firewall protect against?
A firewall protects you from unsolicited and unwanted incoming network traffic. It evaluates incoming traffic for malicious threats, such as hackers and malware, to prevent them from infiltrating your computer or network.
Do you need a firewall?
If you use the internet, it’s smart to have a firewall in place. It provides a first line of defense to help protect your computer and the data stored on it from malicious traffic and potential threats.
Can a firewall be hacked?
A cybercriminal can potentially hack any device or system connected to the internet. Firewalls are more susceptible to being hacked if they’re poorly configured, running outdated software, or zero-day vulnerabilities arise.
Do firewalls prevent viruses?
Firewalls don’t protect against viruses on their own. They manage access to your network, whereas antivirus software serves as cyber protection from malicious viruses. However, some software firewall suites, like Norton 360 Deluxe, include virus protection.
Do you need a firewall at home?
Yes, your home needs a firewall. Without a firewall, you leave yourself open to accepting every connection to your home network without a way to detect and reject incoming threats. Intruders could engage in malicious activities like gaining control over your computer or network, deleting your data, or using your personal information to commit identity theft and other online frauds.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.









Want more?
Follow us for all the latest news, tips, and updates.