Cryptocurrency security guide + 9 crypto protection tips
Follow these cryptocurrency security measures to help protect your crypto investments.

Cryptocurrencies — and the public’s interest in them — are surging across the globe, garnering more than 300 million users across nearly 150 countries. How did this happen so fast? Well, it could be they’re more convenient than your typical bank, great for avoiding transaction fees, and accessible for anyone looking to invest.
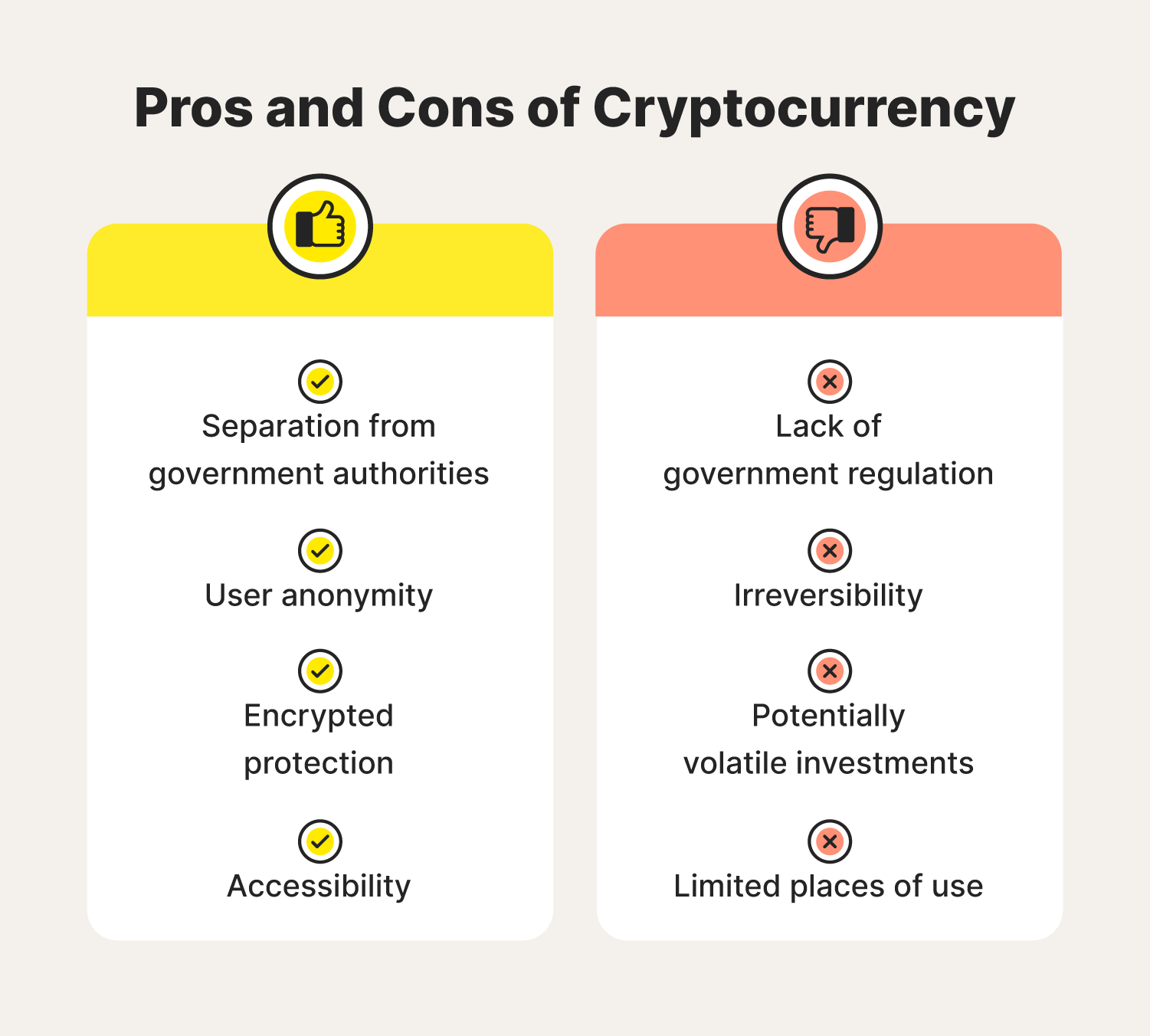
However, nothing is perfect. There are still cryptocurrency security threats that could make dealing with money on this new digital platform risky. Use this cryptocurrency security guide as a tool to improve your crypto safety. We’ve mined for answers to how safe cryptocurrency is, common cryptocurrency scams, advantages and disadvantages of cryptocurrency, along with security measures for protecting cryptocurrency wallets.
Let’s dive in.
What is cryptocurrency?
Cryptocurrency is a digital currency that uses advanced encryption to make it nearly impossible to counterfeit. Unlike the money we’re used to dealing with, cryptocurrencies exist on a blockchain. Think of this as a kind of virtual ledger that is separate and out of reach of official governments and banks.
Beginning with Bitcoin (BTC) in 2009, cryptocurrency received its name because of its use of encryption to authenticate transactions. Since then, the world witnessed the rise of Ether (ETH), Binance Coin (BNB), Tether (USDT), and many more cryptocurrencies that sparked further interest in these new digital assets.
How safe is cryptocurrency?
Trading, investing, and making purchases with cryptocurrency can be a pretty secure process. The blockchain technology used to protect data during these transactions makes it difficult for crypto scammers to hack.
However, it’s important you not get tricked into a false sense of security. Hackers have been working hard to develop cryptocurrency scams to trick users into compromising wallet keyphrases or other information that could allow them access to private accounts.
9 cryptocurrency security measures
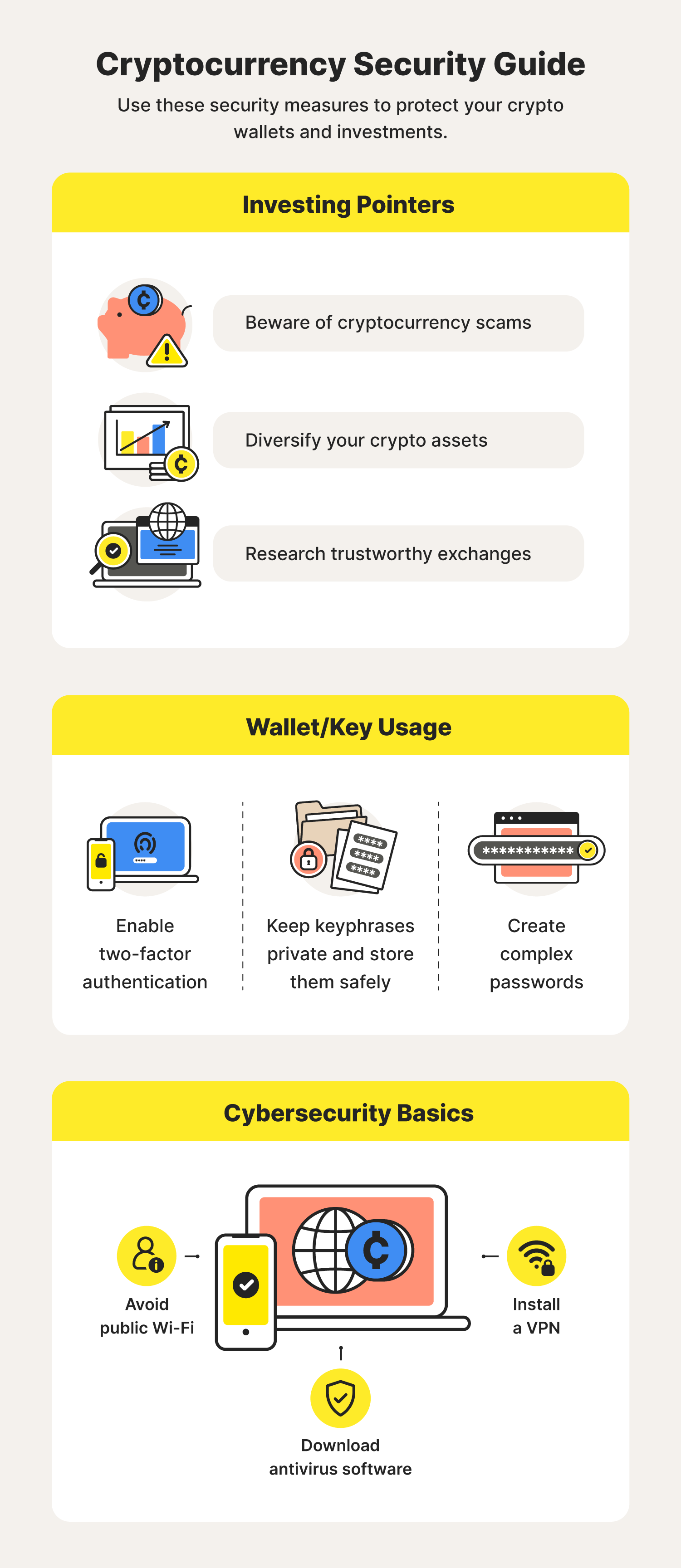
Think about incorporating these cryptocurrency security measures to help ensure your crypto wallets stay protected from different types of hackers.
1. Research trustworthy cryptocurrency exchanges
As with any type of investment, it’s imperative that you do your research before committing yourself financially. As mentioned, there are a number of cryptocurrency scams, like investment opportunity scams, attempting to defraud people out of their money, tricking people into compromising private keyphrases, and other kinds of sensitive data.
2. Create complex passwords
Secure passwords are always your first defense against cybercriminals that are up to no good. As you create login credentials for your crypto wallet, choose a password with a variety of letters, numbers, and symbols. This can help protect your crypto wallet from cyberattacks like password spraying and credential stuffing.
3. Diversify your crypto assets
One cryptocurrency security measure people often take to protect their account and investments is splitting up their crypto assets. It’s completely fine to have more than one crypto wallet holding your balances. Creating this separation helps you avoid losing all of your money if a hacker is able to compromise one of your accounts.
4. Keep your keyphrase private and store them safely
The best way to avoid having your crypto wallet hacked is remembering to always keep your keyphrase private and to store it safely. This unique phrase is the only thing that can grant you access to your account and allows you to trade and purchase cryptocurrency online. Never share this with anyone — as a compromised keyphrase could lead to theft or fraudulent transactions associated with your profile.
Because these are more complex phrases, you should consider using a password manager so you don’t have to worry about forgetting it. Lastly, be sure to choose a crypto wallet that has the protective features needed to keep your assets and information Cyber Safe.
5. Avoid public Wi-Fi
Public Wi-Fi doesn’t have the protection you need to defend against lurking hackers. That’s why you should avoid completing cryptocurrency transactions until you are connected to a private internet connection you can trust. Cyberthieves like to use spyware and other types of malware to compromise keyphrases and other kinds of data.
6. Install a VPN
If you find that you need to complete a crypto exchange or purchase on public Wi-Fi, a VPN is a great tool to have on your device. These work by masking your IP address and network activity so hackers can’t follow your every move, which makes identifying potential targets and installing viruses way more of a challenge.
7. Enable two-factor authentication
Most crypto wallets feature two-factor authentication, a process used to verify user identities during the login process. Biometric data from facial recognition and fingerprint scanning software makes it next to impossible for crypto scammers to impersonate you even after finding out your keyphrase.
8. Beware of cryptocurrency scams
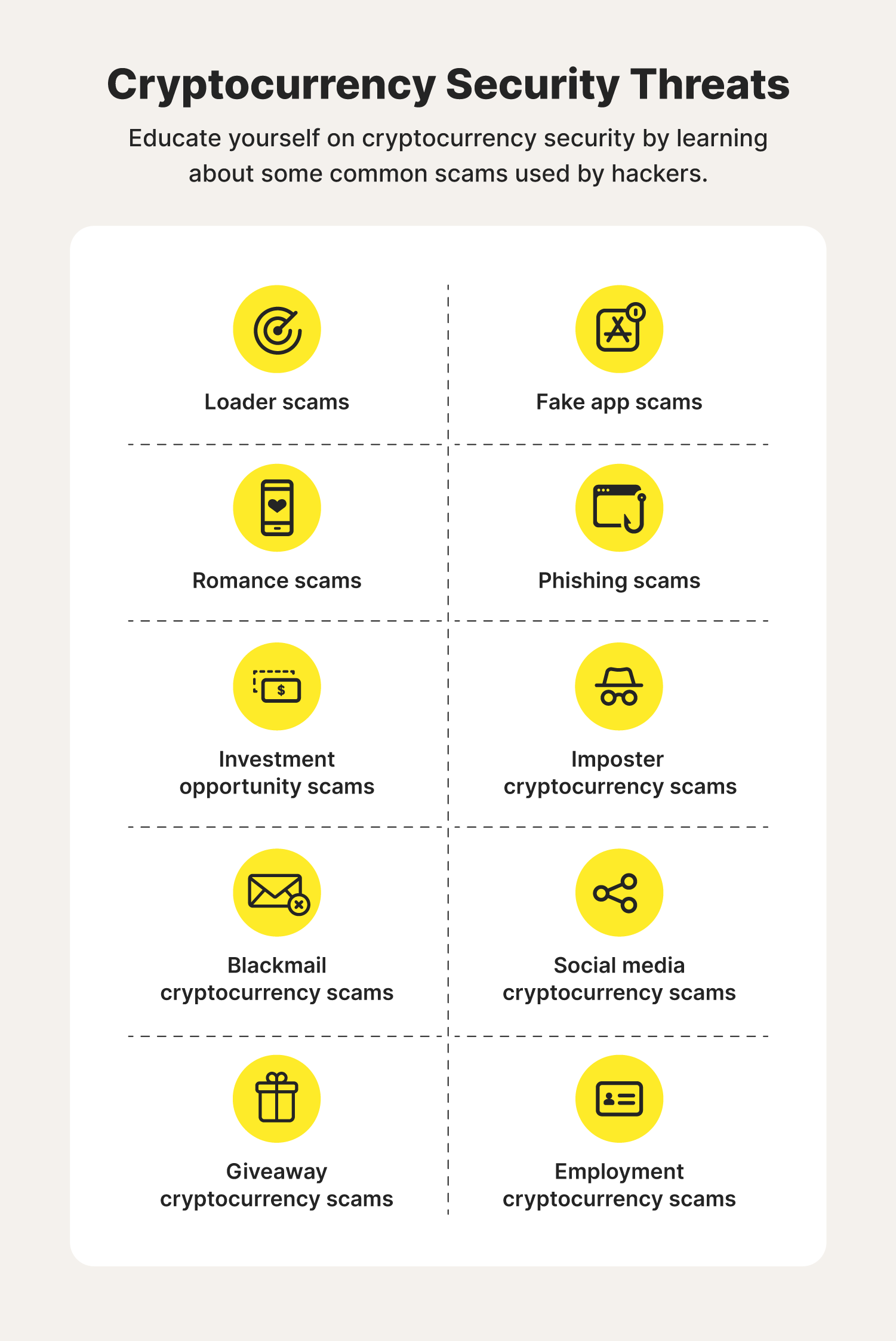
Cybercriminals have to turn to deception to work their way around cryptocurrency’s level of encryption. Here are some common cryptocurrency scams used to trick everyday people.
- Investment opportunity scams: Unsolicited messages luring you to a fraudulent website to get you to invest cryptocurrency in a fake business opportunity.
- Imposter cryptocurrency scams: Cybercriminals pose as a trusted company or government agency to get you to complete a purchase or pay a fee using cryptocurrency.
- Blackmail cryptocurrency scams: A fraudulent message informing you of stolen files that a cybercriminal will only return after you pay a ransom via cryptocurrency.
- Social media cryptocurrency scams: A false social media post or ad for a product or service requesting payment via cryptocurrency.
- Giveaway cryptocurrency scams: Scams designed to trick people into transferring cryptocurrency in hopes of receiving twice as much back.
- Fake app scams: Apps designed to look like legitimate cryptocurrency trading platforms using spyware to steal credentials as people log in.
- Loader scams: Direct requests for access to your cryptocurrency account to help with an investment, promising large returns once complete.
- Romance scams: Hackers posing as online love interests to trick trusting individuals to send them money using cryptocurrency or other payment methods.
- Phishing scams: Email messages often featuring urgent requests for money or account issue alerts from illegitimate businesses and/or cryptocurrency companies.
- Employment cryptocurrency scams: Scams that offer employment training sessions in exchange for payment via cryptocurrency.
There's no reason to feel scared — just remember to look for the obvious signs of a potential scam, like an urgent request for money or your personal login credentials via email.
9. Download antivirus software
Downloading antivirus software can take a little bit of the weight of avoiding cryptocurrency scams off your back. You’ll automatically receive alerts if you come across things like a potentially dangerous link or fake crypto website that could compromise of your crypto wallet.
Whether you’re interested in purchasing an NFT or simply want to expand your investment portfolio, cryptocurrency security should be top of mind as you continue exploring this new investment platform. Use the information and tips provided to keep your crypto wallet and assets Cyber Safe from emerging threats.
Cryptocurrency security FAQs
Round out your knowledge of cryptocurrency security by browsing through some commonly asked questions regarding digital currency.
How secure is cryptocurrency?
The process of exchanging cryptocurrency is relatively secure. However, hackers use cryptocurrency scams to break into crypto wallets and steal investments.
Is crypto safe to invest in?
There is risk in investing in cryptocurrencies, but there is also the potential for high earnings.
What are the most popular cryptocurrencies?
Bitcoin is the most popular cryptocurrency, followed by Ethereum, Binance Coin, Tether, and Litecoin.
Which is the safest cryptocurrency?
Ethereum was one of the first cryptocurrencies designed to block interference or fraud from outside parties.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.





Want more?
Follow us for all the latest news, tips, and updates.