Doxxing: What it is and how to protect yourself
Doxxing can pose a threat to your personal safety, finances, reputation, and mental well-being. In this article, we'll tell you more about what doxxing entails and how to protect yourself. Then get Norton 360 Deluxe to safeguard your online privacy and help find and remove personal information from the web that could be weaponized against you.

When someone doxxes you by publishing your personal details online, you might experience a surge in harassment, hateful messages, or even threats. Often, this alarming attention is the first sign many people have that they’ve been doxxed. Even in milder cases, losing online privacy can be deeply unsettling, affecting mental health and exposing you to potential financial risks.
Read our guide to discover what exactly doxxing is, how doxxing works, how you can help protect yourself, and what you can do if your privacy is compromised.
What is doxxing?
Doxxing, short for dropping dox or documents, occurs when someone, often a cyberbully or cybercriminal, maliciously publishes personal identifying information about you on the internet without your consent. They might post your ID, address, place of work, personal photos, or even your Social Security number (SSN).
Generally, cyberbullies commit doxxing attacks to:
- Get revenge
- Troll for attention or entertainment
- Extort money
- Harass people
- Punish those whose opinions they disagree with
The ACLU of New York has noted an uptick in doxxing of people who are outspoken about issues like women’s rights, trans rights, and other causes. Journalists covering controversial topics are another frequent target.
According to data by SafeHome.org, the most common factors that fuel doxxing attacks are poorly received public posts, perceived slights, a difference of opinions, or gaming disputes. Following a disagreement, the attacker usually makes it their goal to shame the target, incite violence, cause them to lose their job, or inflict other harm.
How to protect yourself against doxxing
There’s no sure-fire way to stop yourself from getting doxxed, but you can use a few tactics to make it less likely. Here are some tips to help you ward off attacks:
- Don’t overshare online: Be cautious about sharing your birthday, hometown, high school, or employer online. Never publish your Social Security number, home address, driver’s license number, bank account number, or credit card number.
- Ask data brokers to remove your information: Websites like PeekYou, Acxiom, and Clearview AI compile public information on people and sell it. The Norton 360 Deluxe Privacy Monitor feature can help you opt out of their “services.”
- Don’t antagonize others: Be careful about what you say online. Someone you annoy may be more likely to seek out your personal information to doxx you. Poor netiquette or antagonistic behavior may increase this risk.
- Delete old social media profiles: Don’t allow doxxers to search through old posts that may have aged poorly or give them insight into your life — delete content that is no longer important to you and close old accounts.
- Update privacy settings: Configure the privacy settings on your social media profiles to keep your accounts secure and less prone to doxxing.
- Use a virtual private network (VPN): A VPN masks your device's IP address and helps protect the data you send and receive, keeping you safer from doxxers.
- Get creative with your usernames: A doxxer can track your username across the internet to find your posts on various platforms. Unless it’s a part of your brand, consider using different usernames for each account.
- Don’t click unknown links: Doxxers might use phishing to trick you into sharing private information or downloading malware. To avoid phishing, be wary of “businesses” urgently asking you to click a link or navigate to another page.
- Create strong passwords: Use strong, unique passwords on every site — especially on accounts you use to manage your finances and work communications.
- Use different email addresses: Use different emails for different purposes to mitigate damage in the event of a doxxing attack. For instance, you might want to create separate email accounts for commercial mail, social media, work, and school.
Is doxxing illegal?
There are no federal laws against doxxing, but some states have passed anti-doxxing legislation. Other laws make it illegal to stalk, harass, or use mail or delivery services to publish identifying information about another person.
States with laws against posting someone else’s personal information on the internet non-consensually and with malicious intent include:
Yet more states, like Minnesota, make it a crime to dox people with a specific occupation, like law enforcement officers.
Records people might use to dox you
People can use public records to find information about you and publish it online. In addition, data brokers compile personal information and sell it to companies or individuals. Doxxers can also use your social media posts to figure out where you live, work, and study.
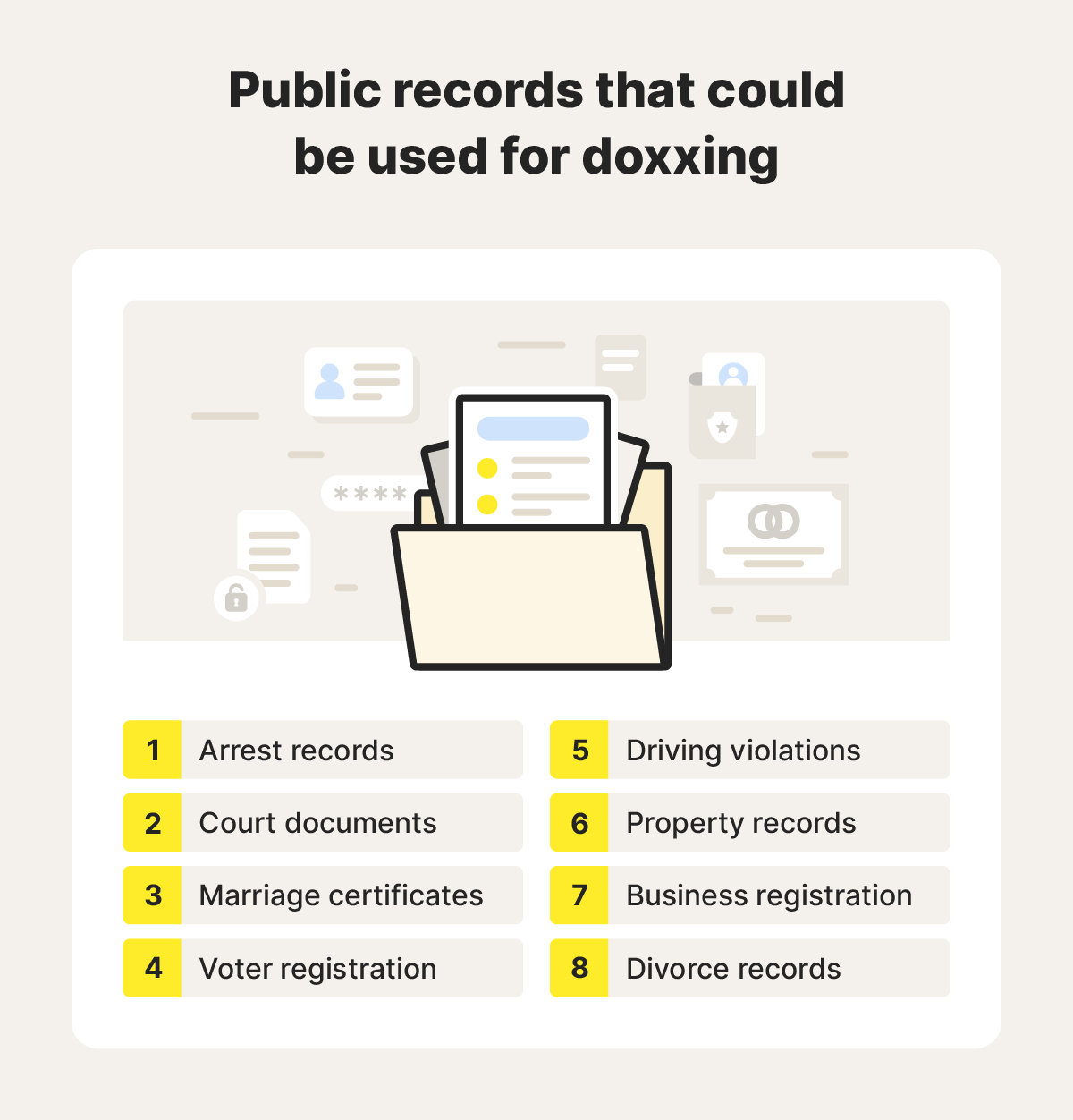
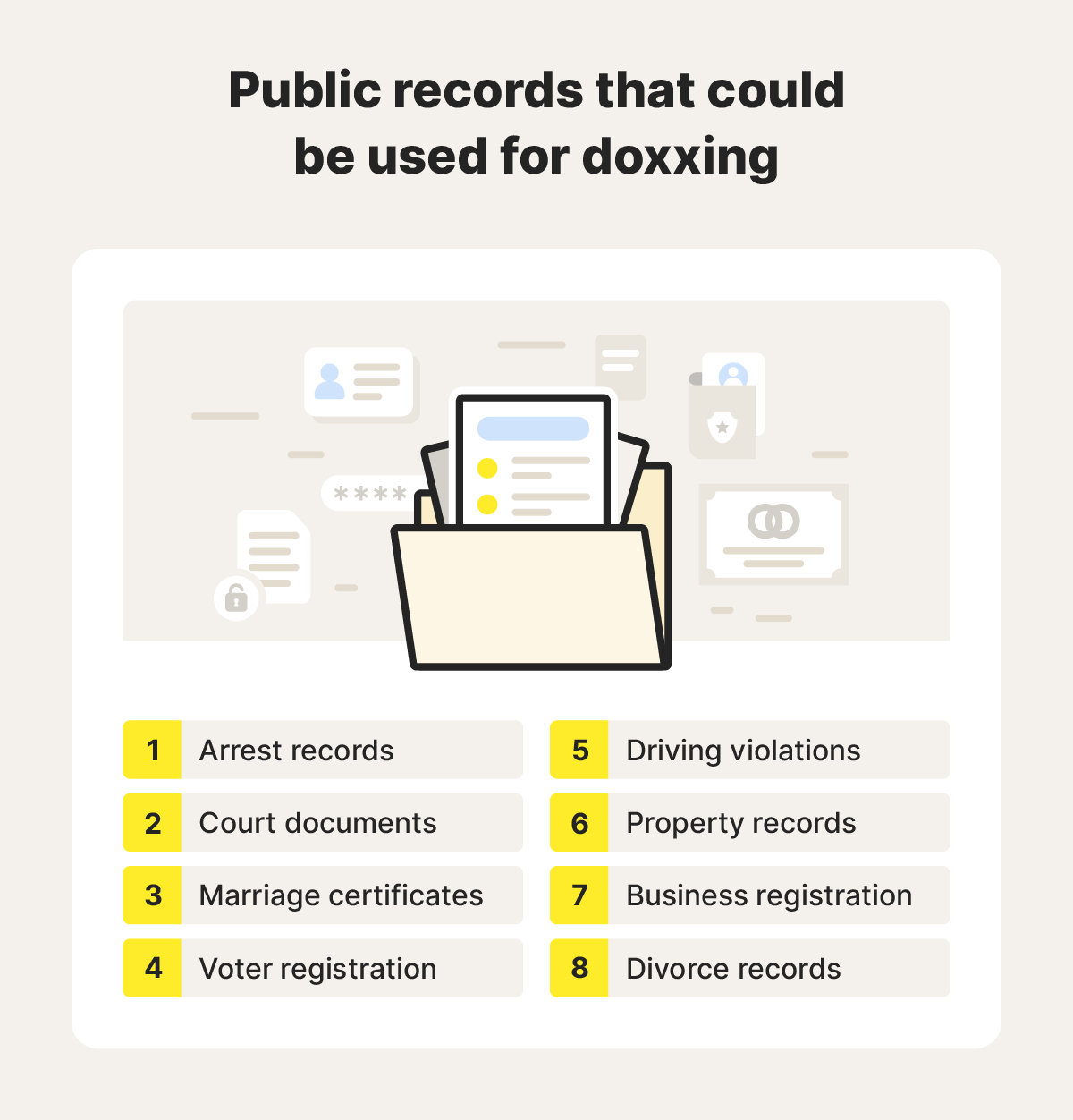
Anyone can publish information that is publicly available online or in public records. This includes your:
- Full name
- Phone number
- Arrest records
- Court documents
- Marriage certificates
- Divorce records
- Voter registration
- Driving violations
- Property records
- Business registration
- Home or work address
Unfortunately, even if you’d rather keep these things a secret, in many states, doxxers are legally entitled to publish anything that is accessible to the general public.
Following a data leak, doxxers may also be able to access information that’s not available in public records, like your Social Security number. Doxxers can buy this data on the dark web and publish it on public forums.
Norton 360 Deluxe includes powerful anti-hacking protection to help keep your data secure. It also monitors the dark web and notifies you if your data is found, and it has a built-in Privacy Monitor feature that can help remove your information from data broker websites.
What are some common doxxing techniques, and how do they work?
A doxxer’s job can be as simple as scrolling through your socials. More experienced doxxers can use advanced techniques, such as cyberstalking, packet sniffing, IP logging, reverse cell phone lookups, and phishing to uncover private information about their targets.
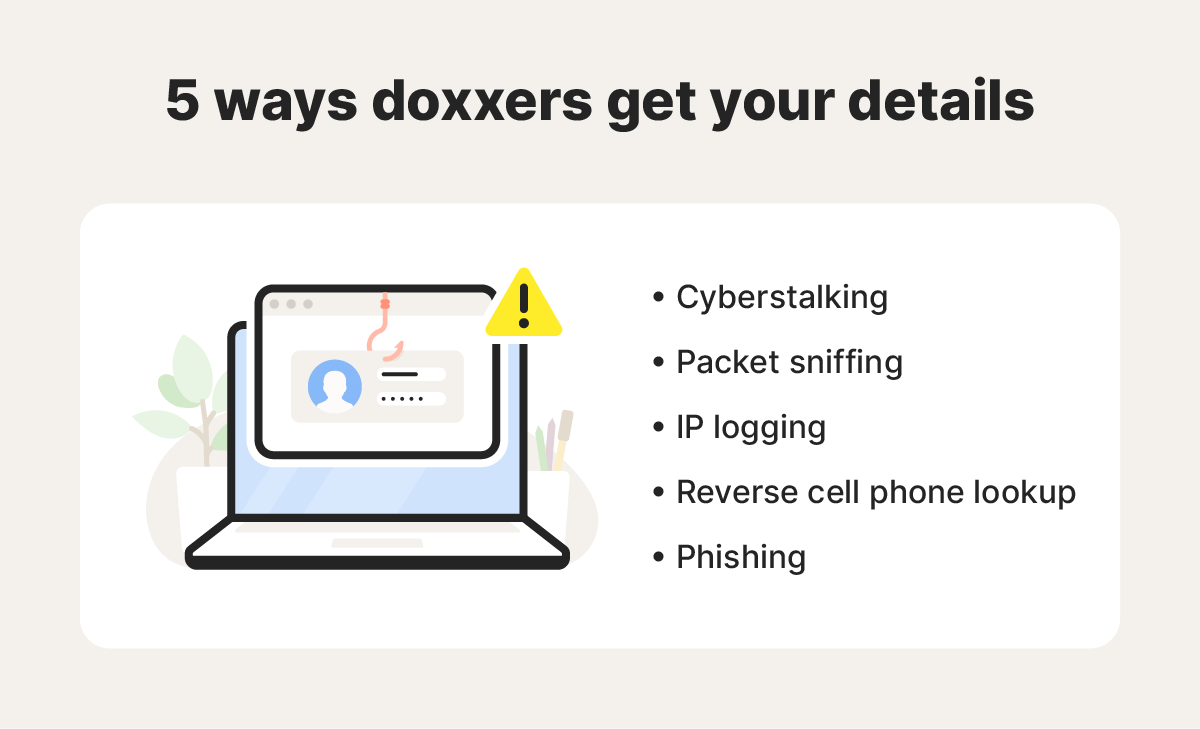
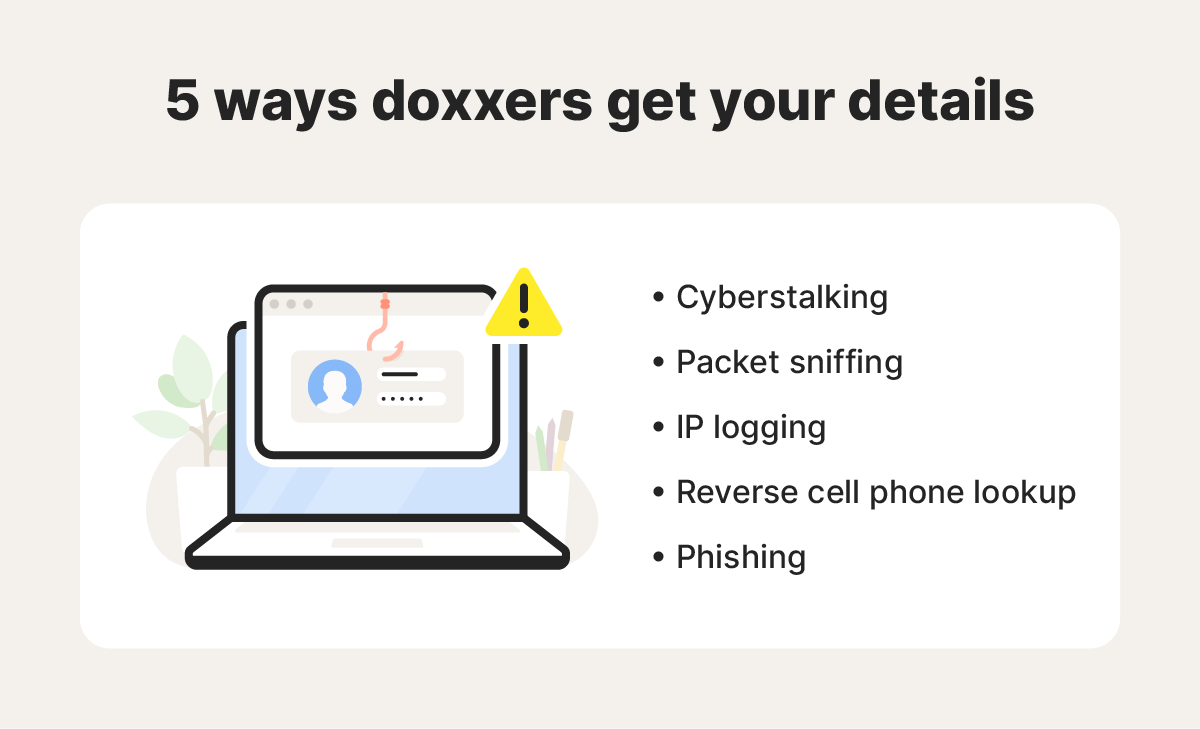
Here’s a breakdown of what these doxxing techniques are and how they work:
- Cyberstalking: Cyberstalkers may peruse your social media posts to find personal details like your birth date, hometown, relationship status, phone number, educational updates, work history, or more.
- Packet sniffing: Hackers can use a packet sniffer to crack the security of a network and intercept the data and private information flowing through it, like account passwords and credit card numbers.
- IP logging: A hacker can use code or an online application to uncover your IP address, find your physical address, or deduce information about your online behavior.
- Reverse cell phone lookup: Reverse phone lookup services can help doxxers find your name and other personal information by entering a phone number into a database.
- Phishing: By leveraging a fictitious business, persona, or scenario, phishers can trick targets into clicking malicious links that allow them to access their target’s device and the personal information stored on it.
As you can see, doxxers have several tools and tactics to find private information.
Keep yourself safer from the dangers of doxxing
An estimated 11 million people say they’ve been doxxed, and 90% of web users are worried it will happen to them. You don’t have to be one of them.
Norton 360 Deluxe combines advanced tools to help safeguard your personal information and secure your online presence. With an ironclad VPN to hide your location, Dark Web Monitoring, and the built-in Privacy Monitor feature to help remove sensitive information from people-search websites, Norton can help you flip the script on would-be doxxers.
FAQs
How did doxxing start?
The concept of doxxing arose in the early 1990s in an offline context, following a doxxing attack on a U.K. organization focused on improving race relations. Initially dubbed “dropping docs,” this concept soon found its way online and evolved into “dropping dox,” or just “doxxing,” which is now a common strategy for cyberbullying and harassment.
What is the difference between doxxing and swatting?
Doxxing is the act of maliciously exposing someone's personal information online without their consent; swatting involves making a false police report to trigger a SWAT response at someone’s home.
What is consensual doxxing?
In consensual doxxing, the person being doxxed agrees to let someone find and disclose their information for a specific purpose or scenario — often for training. Consensual doxxing has also become a trend on TikTok, with users challenging pro sleuths and doxxers to uncover private details like their address or age using only the information they have posted online for entertainment.
How can I tell if I’ve been doxxed?
The most common way to discover if you’ve been doxxed is if you start to notice the consequences. However, you can also find out if someone is leaking your private details by:
- Searching your name online
- Checking social media
- Taking notice of calls and messages from people you don’t know
- Investigating possible data breaches
- Using a service like Norton 360 Deluxe, which monitors the dark web and notifies you when it finds your data
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.







Want more?
Follow us for all the latest news, tips, and updates.