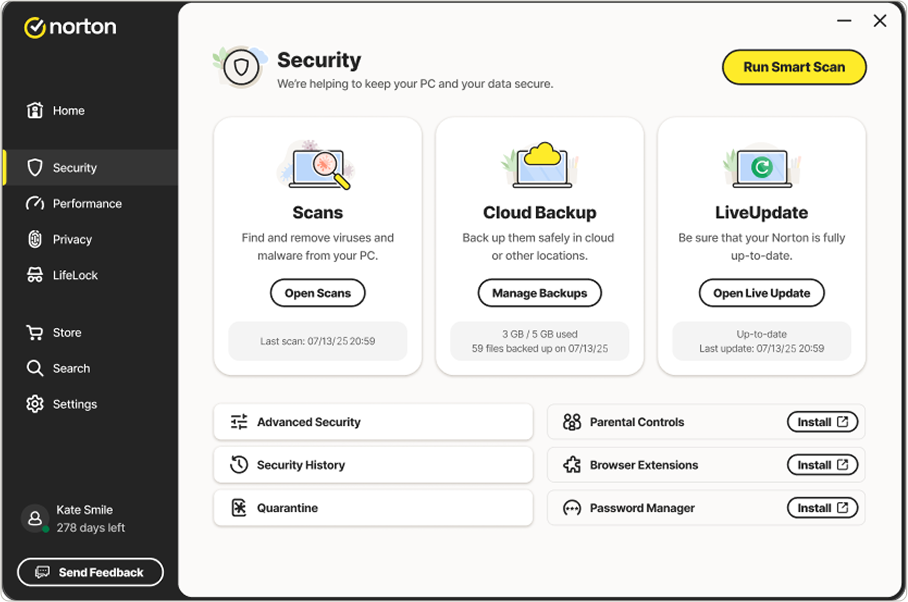
How to prevent cybercrime: 11 ways to protect against threats
Learn how to prevent cybercrime from ruining your finances and identity with these safety tips.
Updated July 21, 2025






































































































Want more?
Follow us for all the latest news, tips, and updates.