How to avoid ransomware: 9-step guide
What are drive-by downloads? Use this complete guide on drive-by attacks to help protect your data from drive-by hacking and other dangerous online threats.

- Step 1: Never expose personal information
- Step 2: Prioritize email security
- Step 3: Keep software and applications updated
- Step 4: Use a VPN on public Wi-Fi
- Step 5: Perform backups regularly
- Step 6: Do not pay ransom demands
- Step 7: Safeguard mobile devices
- Step 8: Consider firewall protection
- Step 9: Download antivirus software
- Ransomware security FAQs
Ransomware is a file-encrypting malware designed to hack and exploit sensitive data. Using money as their motivator, hackers used this cyberattack to target more than 4,000 vulnerable users over a span of two years, costing victims more than $16 million in 2021 alone.
This recent surge in ransomware attacks inspired the creation of this ransomware security guide. Use the nine steps below to learn how to avoid ransomware online, helping you keep your devices safe and pockets full.
The only thing that might be worse than becoming a victim of a cyberattack is learning that you could've done something to help prevent it.
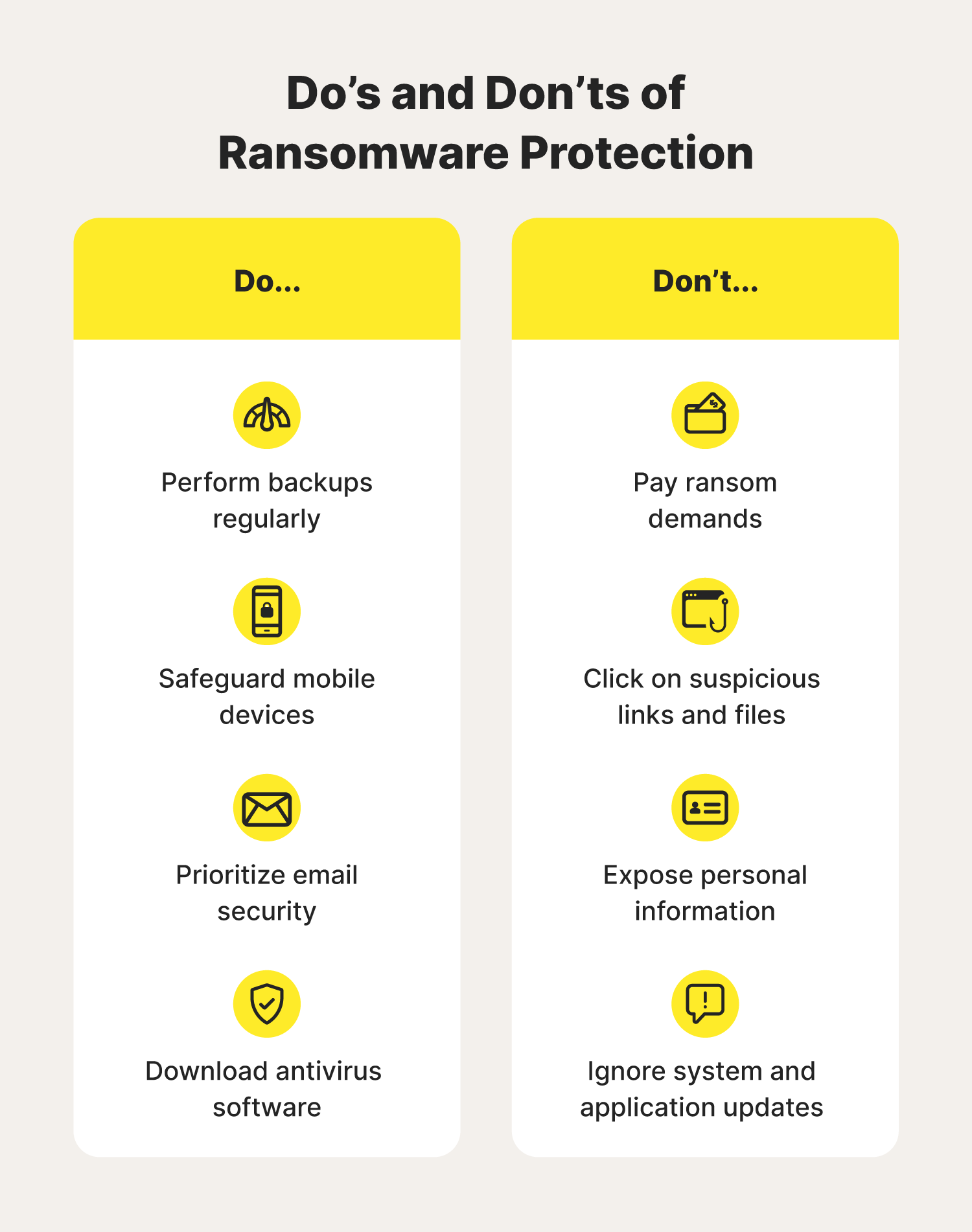
Step 1: Never expose personal information
Protecting yourself from ransomware starts with remembering to always protect your personal information online. Never reveal addresses, Social Security numbers, login credentials, and/or banking details. This applies to when you’re answering an email, unsolicited phone call, or text message.
Phishing scammers may try to trick you into installing ransomware or another type of malware by impersonating an individual or company you’re familiar with to gain your trust.
Step 2: Prioritize email security
Cybercriminals love using phishing emails to deliver ransomware attacks on unsuspecting users. In fact, hackers use phishing emails in over 90% of their cyberattacks.
Help stop ransomware attacks in their tracks by:
- Avoiding suspicious links and downloadable files
- Turning on spam filters
- Creating reliable login credentials
- Enabling two-factor authentication
And when it comes to your inbox, always feel free to delete messages from unknown senders.
Step 3: Keep software and applications updated
Help protect against ransomware by making sure that your operating system and the applications installed onto your device are up to date with the latest security features. Some devices make it easy by notifying you when there is an update available for you to install.
Exploit kits hosted on compromised websites are commonly used to spread different types of malware. Regular updates to vulnerable software is necessary to help block different types of ransomware.
Step 4: Use a VPN on public Wi-Fi
If you’re traveling or doing remote work, using a VPN helps with maintaining a secure and private connection, especially if you’re going to be using public Wi-Fi. These internet connections often lack the security features needed to help prevent ransomware attacks.
VPNs work by masking your IP address and online identity. This helps prevent hackers from using small bits of your data to learn how to best deliver their ransomware attacks.
Step 5: Perform backups regularly
Performing regular data backups is another way to help lessen the risk of ransomware. Some applications and external hard drives have automatic backup settings you can enable. But if not, you can always make it a habit once or twice a week.
That way, if you do become a target of a ransomware attack, you’ll be able to easily restore stolen files without paying a ransom.
Step 6: Do not pay ransom demands
No matter how concerned you get, do not pay the ransom. It only encourages and funds these attackers. Even if you decide to pay the ransom, there is no guarantee that you will be able to regain access to your files.
For perspective: Ransomware victims in 2021 only had 65% of stolen files returned to them after paying their demanded ransom. Additionally, 80% of victims experienced another ransomware attack after resolving their first one.
Step 7: Safeguard mobile devices
We use our smartphones for almost everything and anything nowadays. It’s for this reason hackers have taken a liking to mobile malware in the past year, increasing attacks by 500%.
Help keep yourself and mobile devices protected from ransomware by:
- Watching out for smishing texts
- Never sharing personal information via text and/or phone
- Keeping software and apps updated
- Avoiding third-party apps
- Downloading mobile security software
In addition, if you're using a Windows-based computer, ensure to have virus protection for Windows 10 and Windows 11 devices for better safety. If you take these precautions, there’ll be a good chance hackers will find themselves stumped as to why their hacking methods aren't working like they should.
Step 8: Consider firewall protection
Installing a firewall on your computer and mobile devices is an excellent way to help protect yourself from ransomware. You can think of a firewall as a gatekeeper, filtering the data coming onto your devices from the internet.
As your first line of defense when it comes to online intruders and blocking ransomware, firewalls make hackers have to work twice as hard to breach private networks they don’t belong on.
Step 9: Download antivirus software
In the same vein, downloading trusted antivirus software is also a great option for those learning how to combat ransomware. This software is capable of handling cyberthreats if they’re able to make it past your firewall. The round-the-clock protection antivirus software provides can:
- Scan potential cyberthreats
- Detect malware if present
- Block malicious ads and pop-ups
- Destroy and remove infectious software
The extra set of “eyes” can help you feel more secure as you browse online.
Ransomware may be on the rise, but knowing how to protect yourself online with these ransomware best practices can help keep you safe from today’s money-hungry cybercriminals.
Ransomware security FAQs
Still have questions about avoiding ransomware? We have answers.
How many ransomware attacks were there in 2021?
The Internet Crime Complaint Center received more than 3,700 ransomware complaints in 2021.
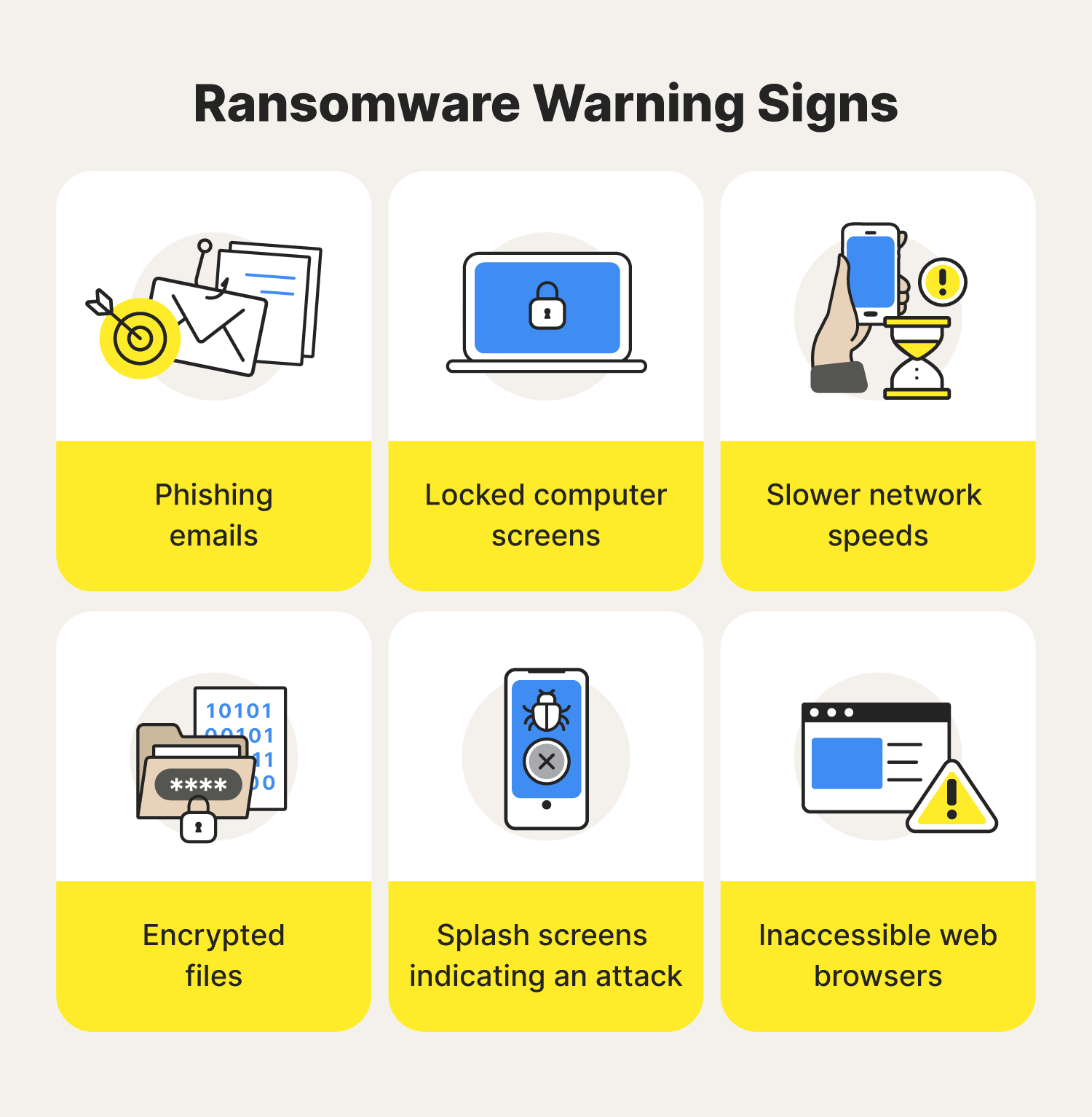
How is ransomware detected?
Ransomware attacks are typically detected after noticing the following signs:
- Phishing emails
- Slower network speeds
- Encrypted files
- Inaccessible web browsers
- Locked computer systems
- Splash screen messages indicating an attack
Can resetting your PC remove ransomware?
Yes. If ransomware only targets one type of file on your computer, a reset would remove those infected files from your device.
What is the most common way in which a user gets infected with ransomware?

Norton™ 360 for Mobile
Powerful protection for your mobile device and online privacy – plus Dark Web Monitoring Powered by LifeLock™.
It’s more important than ever to make sure your mobile devices are secure and your personal information stays private. Norton 360 for Mobile helps deliver powerful, proactive protection for your device and personal information against stealthy cyberthreats and online scams.
In 2020, 54% of ransomware attacks were delivered using phishing emails.

Norton™ 360 for Mobile
Powerful protection for your mobile device and online privacy – plus Dark Web Monitoring Powered by LifeLock™.
It’s more important than ever to make sure your mobile devices are secure and your personal information stays private. Norton 360 for Mobile helps deliver powerful, proactive protection for your device and personal information against stealthy cyberthreats and online scams.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.





Want more?
Follow us for all the latest news, tips, and updates.