Download a VPN for Mac
Sharing sensitive information over unsecured networks is risky. A Mac VPN can help shield the data you send and receive with powerful encryption. Get Norton VPN to help keep your internet connection private, prevent hackers from stealing your personal data, and access the content you love. Try it free today.
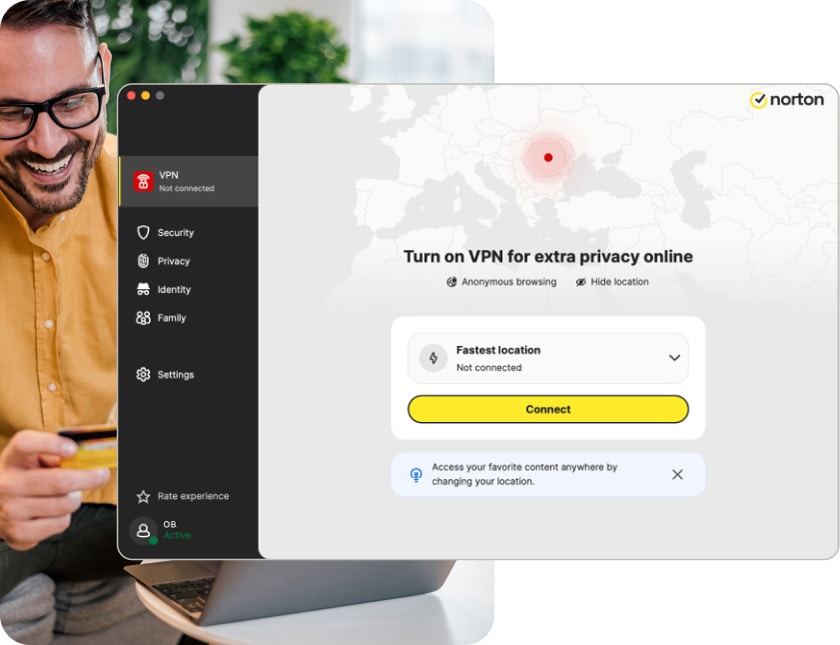
Your Mac® browsing activity may be just as exposed and vulnerable as on any other platform. Using a VPN encrypts your online connection to help keep your browsing private, even on public Wi-Fi. Secure your personal data and unlock your favorite content with Norton VPN. Download our best Mac VPN today and try it for free.
Why you should use a VPN on your iMac, MacBook, or Mac mini
-
Bank-grade encryption
We use best-in-class encryption technology with a kill switch fail-safe to maintain a secure tunnel between your Mac and the VPN server.
-
Unmatched freedom
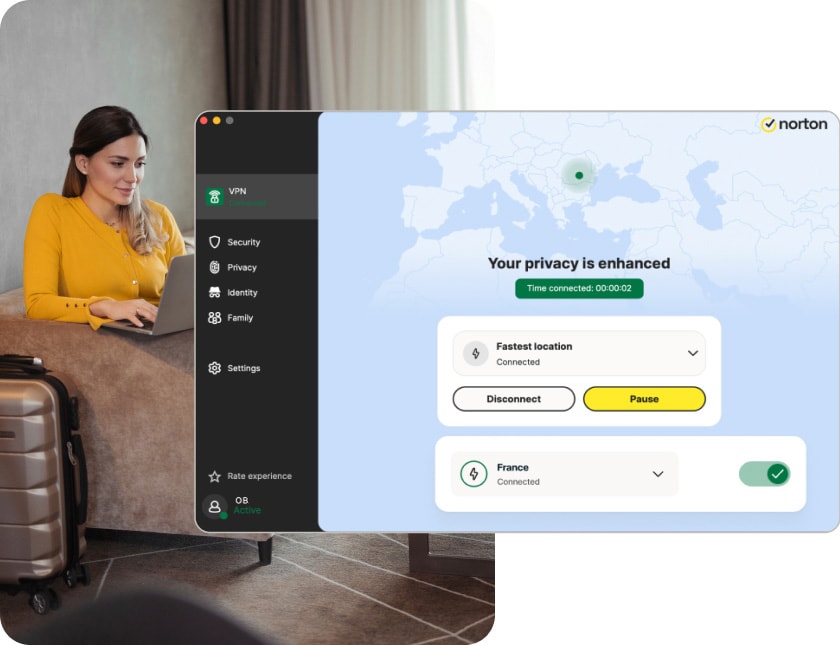
Change your location for unbeatable access to all your favorite sites and streaming services no matter where you are.
-
Secure public Wi-Fi
Protect your sensitive personal data on unsecured public Wi-Fi so you can browse and shop in peace.
-
No-log policy
What you do online is your business — that’s why Norton VPN doesn’t track or log your online activity.
-
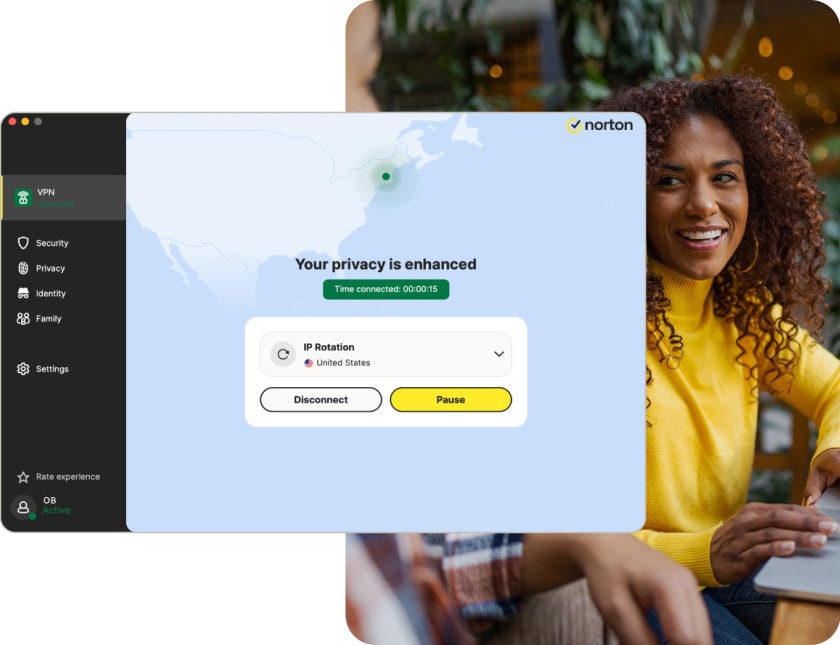
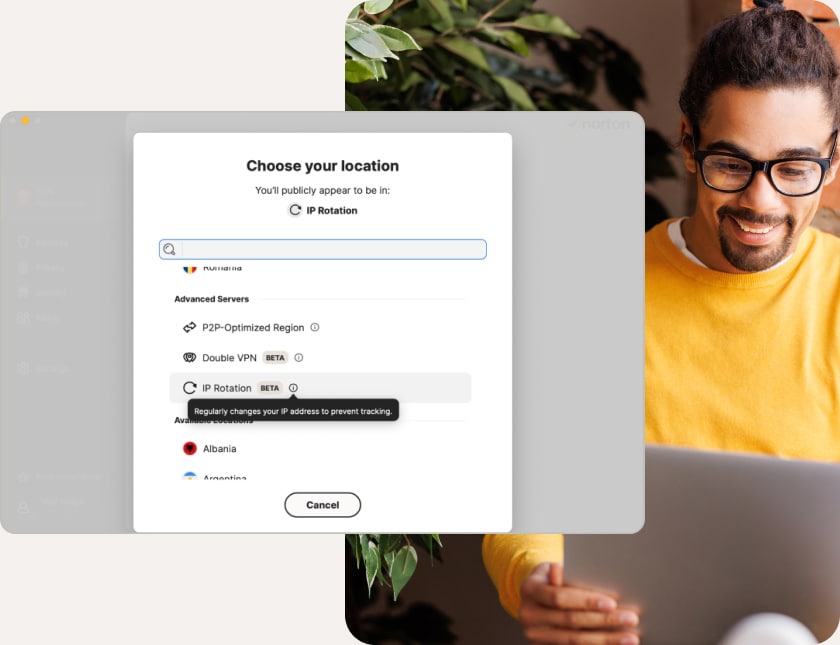
Block ad-tracking
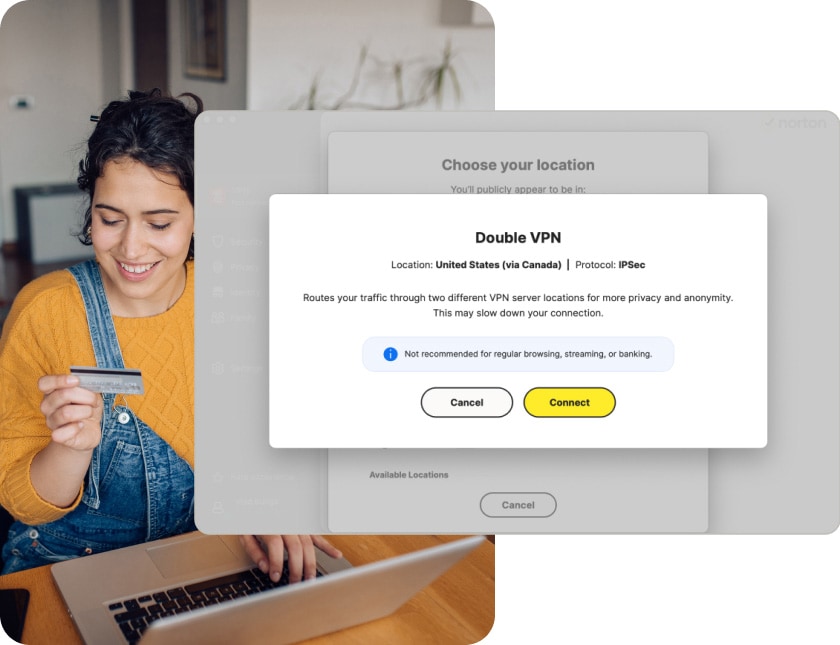
With powerful ad-blocking technology, IP rotation, and double VPN features, Norton VPN helps stop advertisers and others from following you online.
-
Region selection
Connect to any of our high-speed servers around the world for a reliable connection to over 100 VPN locations.
How to set up a VPN on Mac
Downloading a VPN for Mac and setting it up on a computer takes just a few simple steps. Here’s how to install the Norton VPN app on your Mac:
Improve your Mac privacy with a VPN
Norton VPN for Mac provides you with security online and a private network that helps mask your location, shield your internet activity, and protect your identity.
Enjoy an even more secure macOS
A VPN gives your Mac ironclad online security and privacy and helps protect against snooping, man-in-the-middle attacks, and other hacking threats.
Work and play online from anywhere
A VPN masks your IP address and routes your traffic through a secure server, so you can work and play from anywhere. Connect through a variety of server locations across six continents.
Hide your data
With bank-grade encryption, your internet data travels through a secure virtual tunnel, helping to protect sensitive information like passwords and banking details.
Get a powerful VPN for all your devices
With plans covering up to 10 Mac, iOS, Android, PC, and smart TV devices, you can secure your whole family’s online activity with just a single account.
-
iPhone/iPad
Stay anonymous with Apple-approved internet privacy from Norton VPN for iOS.
-
Android
Encrypt your internet data and stream on the go with Norton VPN for Android.
-
Windows
Protect your IP address, browsing activity, and sensitive data with Norton VPN for Windows.
Strengthen your privacy with Norton VPN for Mac
Norton VPN for Mac is the ultimate online privacy tool that lets you establish a lightning-fast connection from anywhere in the world. Download Norton VPN to help keep your activity private, protect your personal data, and access your favorite content. Try it free today.
FAQs
If you use unsecured public Wi-Fi, bank or shop online, or share sensitive data over the internet, you need a VPN to help secure your connection and protect the information you send and receive. Given the breakneck connection speeds of premium VPN services and the range of other privacy and security benefits VPNs provide, like protection against online trackers, it’s worth getting a VPN and setting it to auto-connect whenever you go online.
Mac VPNs are definitely safe to use, as long as you select VPN software from a reputable vendor. Dedicated Mac VPN apps like Norton VPN for Mac are designed from the ground up to provide seamless integration with macOS, marrying maximum privacy and security with flawless performance.
Macs don’t have a built-in VPN. But they do have a VPN interface utility within the Network section of System Preferences/Settings that enables you to manually configure a VPN if you have the right credentials and other details needed to connect directly to a VPN server. Or you can download a VPN app like Norton VPN to set up, turn on, and customize your connection in just a few clicks.
When connected to Norton VPN, the data you send and receive online is tunneled through an encrypted connection between your Mac and the VPN server. That gives you online privacy, anonymity, and security against cybercriminals — preventing them from seeing your IP address, gaining access to your Wi-Fi connection, or intercepting the data you share while you browse.
If you choose a multi-device subscription, you can use Norton VPN for Mac while you’re using the VPN client on other devices at the same time. You can include up to ten macOS, iOS, Windows, Android, and smart TV devices in a single subscription plan.
-
Other Tools
-
Helpful Links
System Requirements
Note: Mac, Apple, and the Apple logo are trademarks of Apple Inc., registered in the U.S. and other countries.
*Automatically renews annually after the trial period ends, unless cancelled. The price quoted in the cart today is valid for the introductory term after the trial, after which your subscription will be billed at renewal pricing. Renewal pricing is subject to change and may be charged up to 35 days before the active term ends. For support or to cancel automatic renewal, log into your account or contact support.
Norton VPN: A yearly subscription is just $xxxx for the first year after the free trial, then only $xxxx/year after.







