What are cookies? How they work and when to accept them
Computer cookies are files that allow websites and web servers to remember your device and browsing activity. Learn more about cookies, including when to block and when to accept them. Then get Norton AntiTrack to help block third-party cookies, prevent tracking, and stay more private online.

Your personal data is private—or, at least, it should be. Understanding computer cookies is essential to properly managing your data. Keep reading for an in-depth overview of cookies and how they affect your data.
What are cookies?
Computer cookies are small files used by web servers to save browsing information, allowing websites to remember your device, browser preferences, and associated online activity. Cookies are often very helpful, because they spare you from having to log into your accounts every time you return to the same website.
But cookies can also be invasive, as they help companies and advertisers build a profile of your browsing habits, interests, and purchases, which they can use to target you with ads. Depending on permissions, that information can also be shared with third parties.
What are cookies used for?
Computer cookies are intended to help a website keep track of your visits and activity. This lets them remember you and your preferences so they can personalize your experience. For example, cookies can help you sign into Facebook faster, and they are what let you save items in your shopping cart for later when shopping online.
Cookies are also used to personalize ads, too. This has pros and cons—while some find it intrusive to see ads targeted to their interests, citing privacy issues, others find it more helpful than seeing irrelevant ads at every turn.
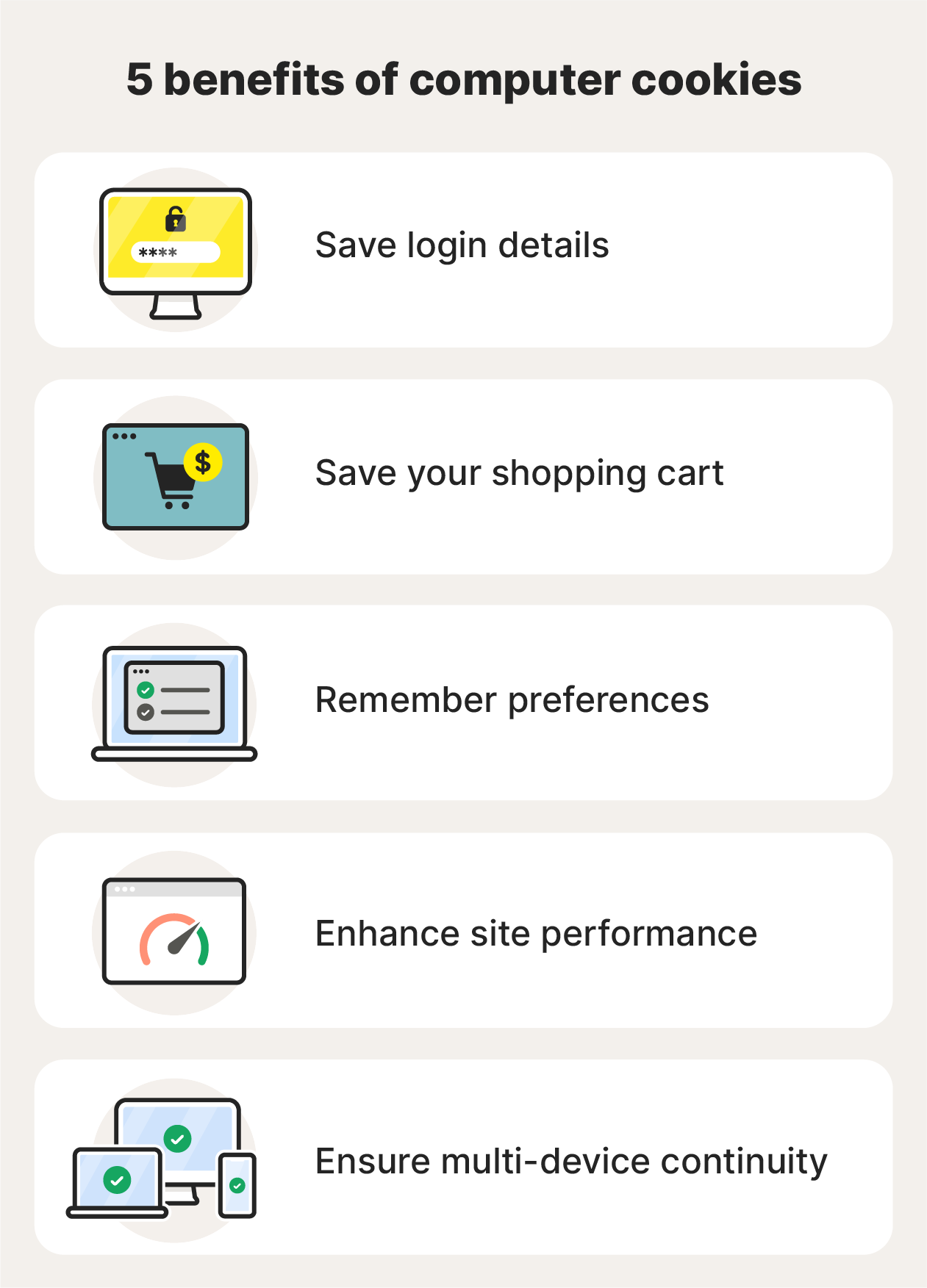
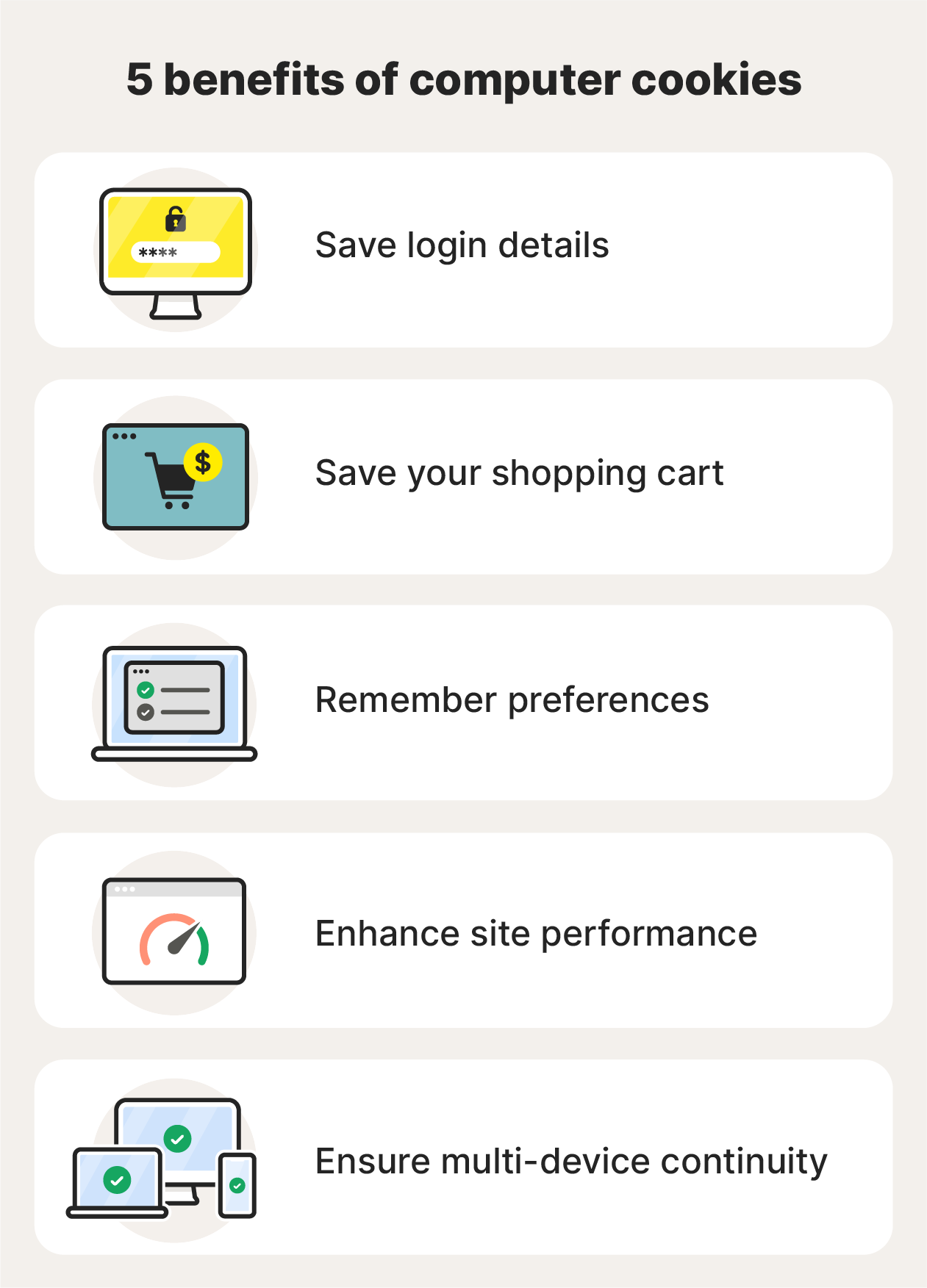
Here are some pros and cons of website cookies:
Pros of cookies
Having your movements tracked doesn’t have to be a bad thing. Some of the helpful features of cookies include:
- Saving login details: For frequently visited sites, it can be useful for the website to remember your login credentials so you don’t need to sign in every time you visit.
- Saving your shopping cart: Cookies help sites save the items you‘ve placed in your shopping cart. That way, you can continue to browse the site or even go to a different site without losing the items you’ve saved.
- Remembering preferences: If you change a website’s settings, such as language or currency preferences, the site uses cookies to remember these preferences for your next visit.
- Enhanced site performance: Websites can use cookies to store data, allowing the site to load faster. Websites also use analytics to improve their sites and make them more user-friendly.
- Multi-device continuity: Cookies can help you maintain sessions across devices. For example, you could start streaming a movie on your phone and continue watching it on your laptop.
Cons of cookies
Of course, cookies also have a dark side. Here are a few of the more negative aspects of cookies:
- Data privacy: Third parties can use cookies to track your digital footprint and build a detailed personal profile of you. Websites sharing your data without your explicit knowledge or consent raises privacy concerns.
- Session stealing: Hackers can exploit cookies to hijack active sessions—for example, while you’re checking your bank account online. This is a bigger risk if you are on a public Wi-Fi network or browsing an unsecured website.
- Cybersecurity concerns: Cookies themselves are generally safe, but they can be exploited by attackers to access your sensitive data.
- Sluggish performance: When your browser is cluttered with too many cookies, it can impact performance and cause websites to load more slowly.
How do cookies work?
A cookie is a snippet of data that a website stores on your device. The next time you visit that website, your browser sends the cookie back to the site with the information it has stored about you. That information can be things like login credentials, site preferences, and details about your activity from previous visits.
You can make websites “forget” this information by deleting cookies from your computer or device.
Should you accept all cookies?
You don’t have to accept cookies, but some websites won’t let you visit unless you do. So to keep browsing freely, you’ll probably have to accept some cookies. But not all cookies are created equal.
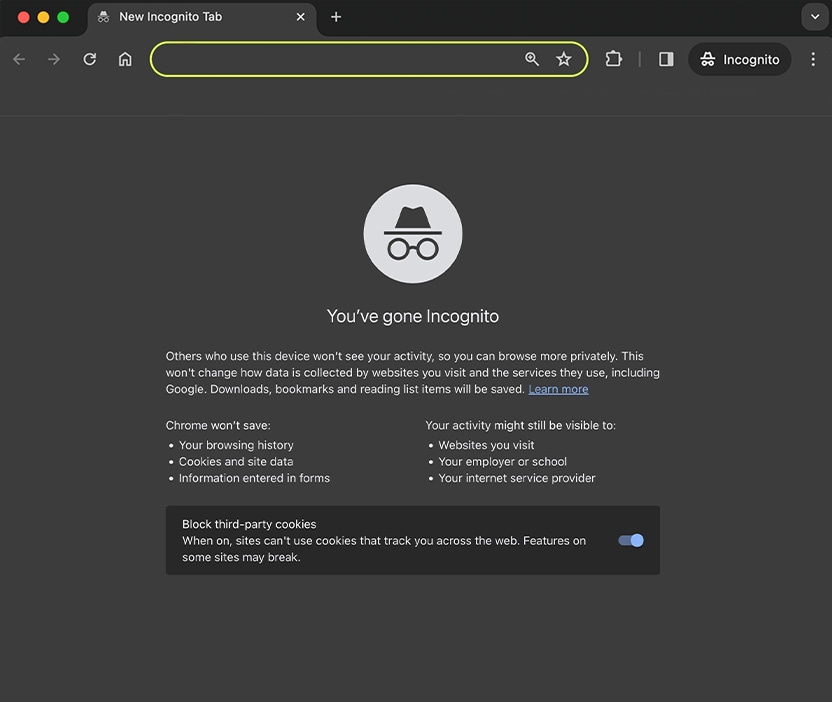
First-party cookies are used to enhance your experience while on a website and remember pertinent information that will help you navigate the site with ease. It usually makes sense to accept first-party cookies. But third-party cookies can be a different story. These cookies are often used by advertisers to track your online activity and show you targeted ads.
You should also beware of accepting cookies on unsecured sites, as it can put your security at risk.
10 types of cookies and how they work
Not all cookies are the same. Here’s a brief overview of some of the most common cookie types and their uses.
1. Session cookies
Session cookies are temporary and are deleted immediately after closing your browser. They’re generally safe and secure because they don’t store personal information over the long term. These are the cookies that allow you to keep items in a shopping cart even after clicking on a different page—they’re essential to making a site function properly.
2. Persistent cookies
Persistent cookies can save data for an extended period of time. These are the cookies that allow websites to store login information and settings preferences. Persistent cookies can also track your activity on a site over multiple visits so content can be personalized based on your interests.
3. First-party cookies
First-party cookies are created by the website you’re currently visiting to track your activity on that particular site. First-party cookies are often essential for the website to function properly. They are generally less risky as they only work on the site you’re on.
4. Third-party cookies
Third-party cookies are created by domains other than the website you’re currently visiting. They track data regarding your online activity across websites and are often used for targeted advertising. They are non-essential and can be intrusive, allowing advertisers to monitor your behavior even when you’re not on their site.
5. Essential cookies
Essential cookies are also necessary for websites to function properly. They include cookies that keep you logged in as you browse a website, remember the items you add to your cart, and maintain secure browsing sessions. Session cookies and some first-party cookies typically fall into this category.
6. Functionality cookies
Functionality cookies enhance a website’s user experience by remembering setting preferences such as language, region, and login data. They don’t track user information across websites and are usually low risk.
7. Targeting cookies
Targeting or advertising cookies track your online activity to show you personalized ads based on your browsing and purchase history. These are non-essential cookies that often collect your data without your full knowledge or consent, which can raise privacy concerns.
Anti-tracking tools help prevent your online fingerprint from being tracked and shared with third parties like advertisers and websites. Use Norton AntiTrack to keep your browsing more private and help avoid annoying targeted ads from following you all over the web.
8. Magic/HTTP cookies
Magic cookies are unique identifiers sent from a server to a user’s computer and used later to identify the user. They are used for authentication and for managing sessions. Magic cookies were more common in older computer systems and have largely been replaced by HTTP cookies that perform the same functions.
9. Supercookies
Supercookies are similar to regular browser cookies in that they track your online activity, but they are stored at a deeper system level, often by internet service providers. This makes them harder to remove as they aren’t in the standard cookie storage location. Since these aren’t stored on your device you can’t delete them. But you can help prevent tracking by using a dedicated privacy tool like Norton AntiTrack.
10. Zombie cookies
Zombie cookies are persistent cookies that just won’t die! They exist outside your regular cookie storage, hiding in multiple locations— and advertisers are able to “resurrect” them to continue tracking you online. The only way to put a zombie cookie in its grave is to root out every location where it’s hiding.


How to remove cookies from your computer
Your computer stores cookies that build up over time, slowing your browser and possibly posing a security risk. Clear your cache and remove cookies on all your browsers regularly to help protect your privacy online and keep your device running smoothly.
Here’s how you can remove cookies from your computer on Chrome:
- Open Chrome, then click the three dots in the top right corner.
- Click Delete Browsing Data.
- Check the box next to Cookies and other site data.
- Click Clear data.
Block cookies and stay private online
While some cookies are helpful and improve your browsing experiences, other cookies can leave you exposed to security and privacy risks. Download Norton AntiTrack to help block invasive cookies and stop data collection companies from gathering information about you and tracking your online activities.
FAQs about computer cookies
Computer cookies can be a good thing, but there is often more to them than meets the eye. Here are the answers to some FAQs about cookies.
How does Google use cookies?
Google uses functional cookies to enhance your user experience by remembering your logins and site preferences. Google also uses targeted cookies to collect data on your browsing patterns and personalize the ads that you see.
Can I get hacked by accepting cookies?
Most cookies are safe to accept, although you might prefer to decline third-party cookies to help prevent websites from tracking your online activity and collecting personal data. High-risk cookies that could leave you open to security threats such as hacking include cookies on unsecured websites or suspicious cookies flagged by antivirus software.
Can cookies steal passwords?
Cookies don’t steal passwords. Websites use cookies to remember your login information, making it easier for you to visit the website again in the future. While cookies themselves don’t “steal” passwords, hackers can hijack cookies by intercepting data and using that information to access your accounts. Using long and unique passwords for all your accounts, setting up a password manager, and regularly clearing your cookies will help you keep your accounts safer.
What information do cookies collect?
Cookies can store information such as the websites you visit, links you click, how often and for how long you visit certain websites, and the items you’ve purchased. Cookies can also remember personal data such as usernames and passwords, your geolocation and IP address, and even your address and phone number.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.



Want more?
Follow us for all the latest news, tips, and updates.