11 strategies on how to stop spam emails from clogging your inbox
Spam emails can clog your inbox and hide threats like phishing scams, malware infections, and even identity theft. Learn how to block spam emails and get Norton 360 Deluxe to help keep your device safer against malicious email attachments and links.

- 1. Mark them as spam
- 2. Delete spam emails
- 3. Block spam senders
- 4. Keep your email address private
- 5. Use a third-party spam filter
- 6. Unsubscribe from email lists
- 7. Check if your email is on the dark web
- 8. Use email aliases for sign-ups
- 9. Disable autoload for images
- 10. Opt out of data broker directories
- 11. Change your email address
- Why am I getting spam emails?
- Common spam email security threats
- How to spot spam emails
- Protect against spam email threats with Norton
- FAQs
Key takeaways
- Spam puts you at risk of phishing, malware, and identity theft.
- Reduce your exposure by reporting it, blocking repeat senders, and using email aliases for sign-ups.
- Cyber Safety software can help you get to the root of the problem by checking if your email is exposed on the dark web or data broker sites.
Spam emails can overwhelm your inbox, and possibly you. They often include misleading claims, scare tactics, and fake urgency to trick you into clicking harmful links. Spammy emails are a major problem, accounting for around 46% of global emails in 2023.
Learn how to stop getting spam emails and get rid of unwanted messages.
1. Mark them as spam
One way to stop spam emails is to mark them as spam. Most email services, like Gmail, Yahoo Mail, Microsoft Outlook, and Apple Mail, have algorithms that filter out spam and junk mail to tuck them away in a dedicated folder, but some still might slip through.
If you see any spam emails in your inbox, mark them as spam. This should stop you from receiving more spam from that sender.
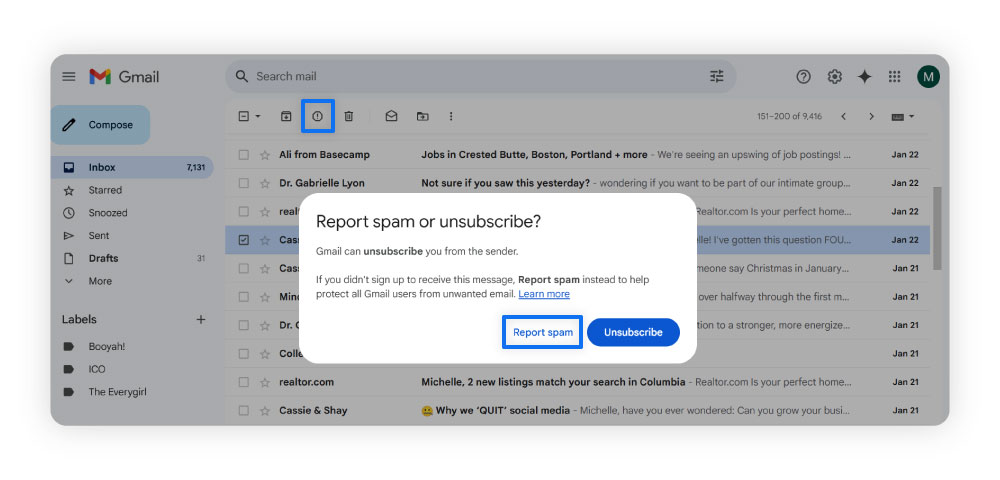
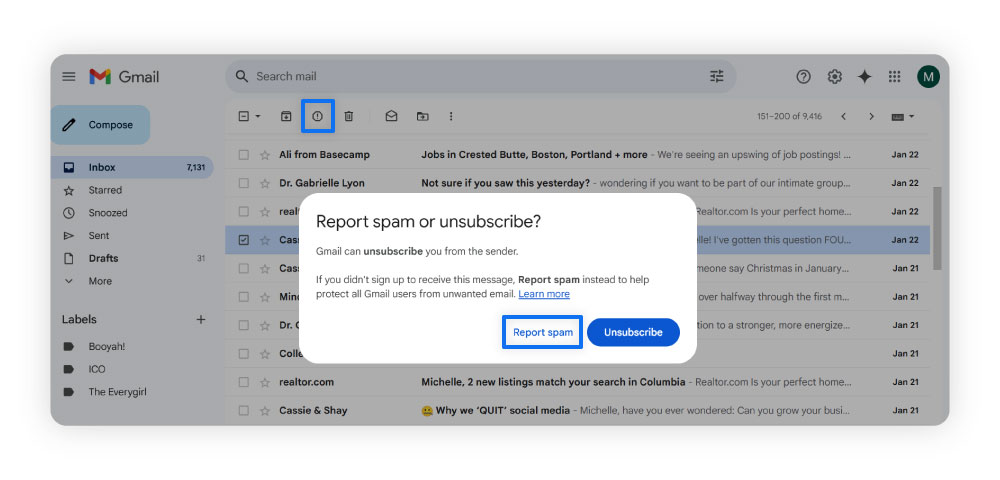
How to mark spam in Gmail
Use the following steps to mark emails as spam in Gmail.
- Select the checkbox next to the email or emails you want to report as spam.
- Click the Report spam icon (a caution sign with an exclamation point).
- Select Report spam.
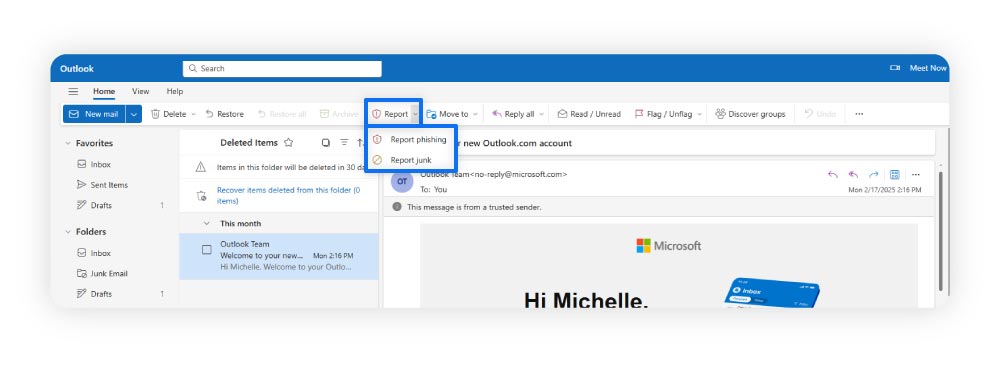
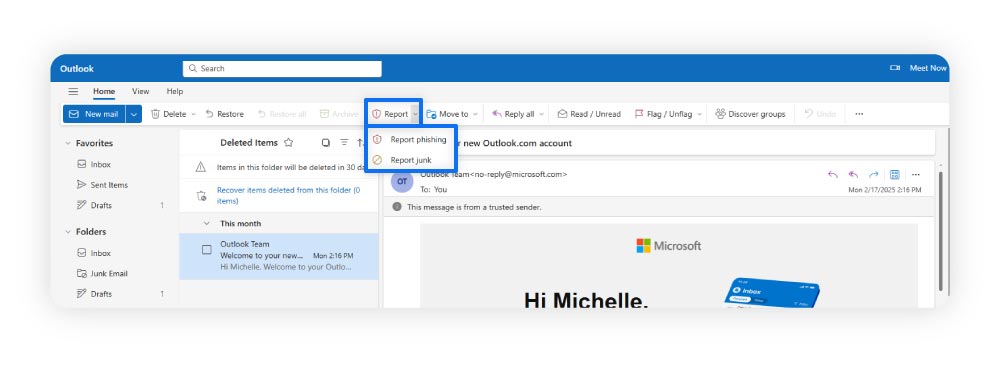
How to mark spam in Microsoft Outlook
Use the following steps to mark emails as spam in Outlook.
- Hover over the email or emails you want to report as spam and select the checkbox.
- Click the Report button.
- Then select Report junk (spam) or Report phishing (scam) from the dropdown menu.
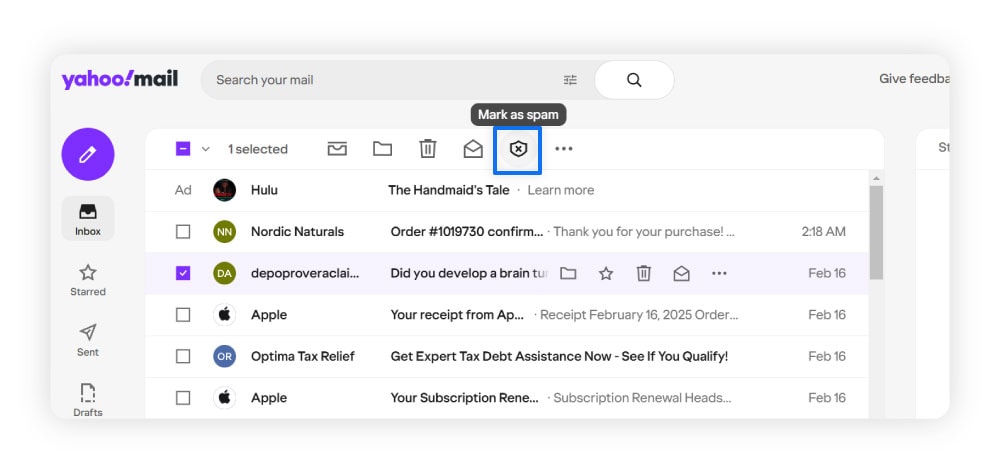
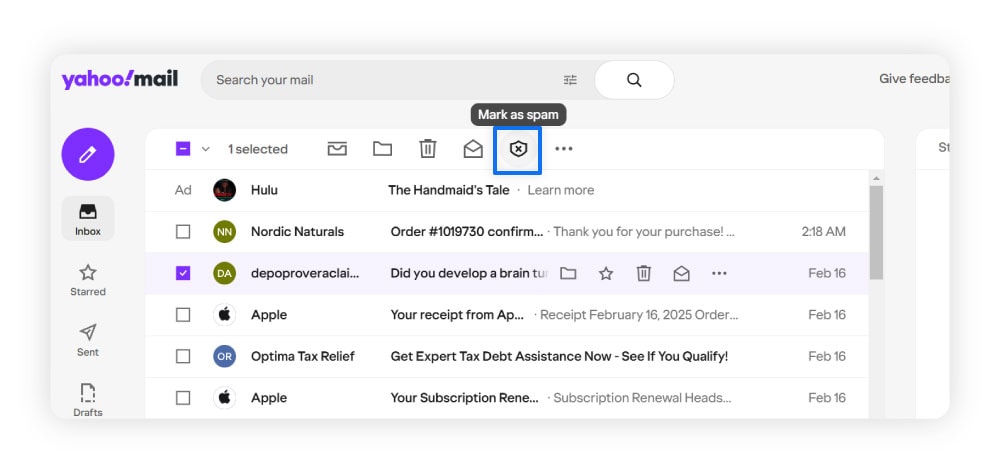
How to mark spam in Yahoo Mail
Use the following steps to mark emails as spam in Yahoo Mail.
- Select the email or emails you would like to report as spam.
- Select the Mark as spam icon (shield with an X).
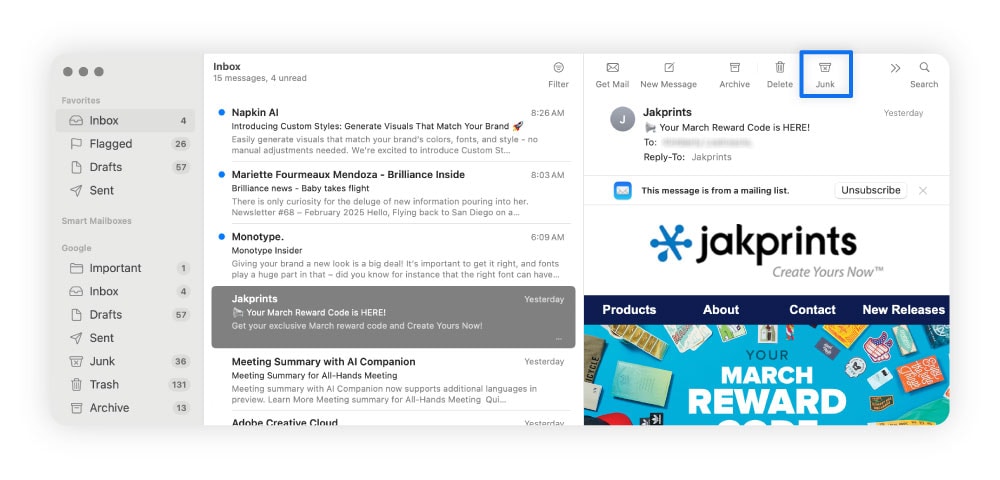
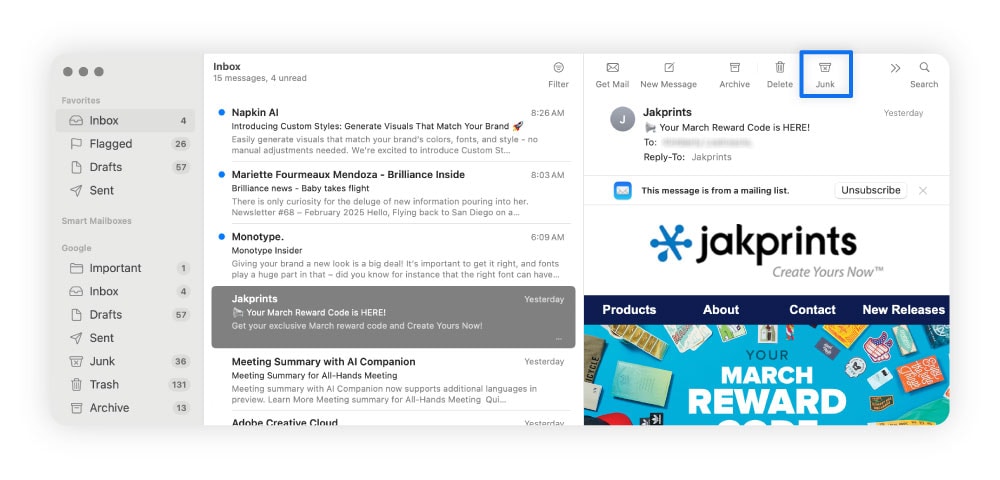
How to mark spam in Apple Mail
Use the following steps to mark emails as spam in Apple Mail.
- Select the email or emails you would like to report as spam.
- Select the Junk icon (“X”-marked trash can).
2. Delete spam emails
If an email looks like a spam message, delete it without clicking or downloading anything. These emails may contain software that tells the sender you’ve opened the email, confirming you have an active account, which could lead to even more spam or scam messages containing malware.
Here’s how to delete spam emails from Gmail, Outlook, Yahoo, and Apple Mail.
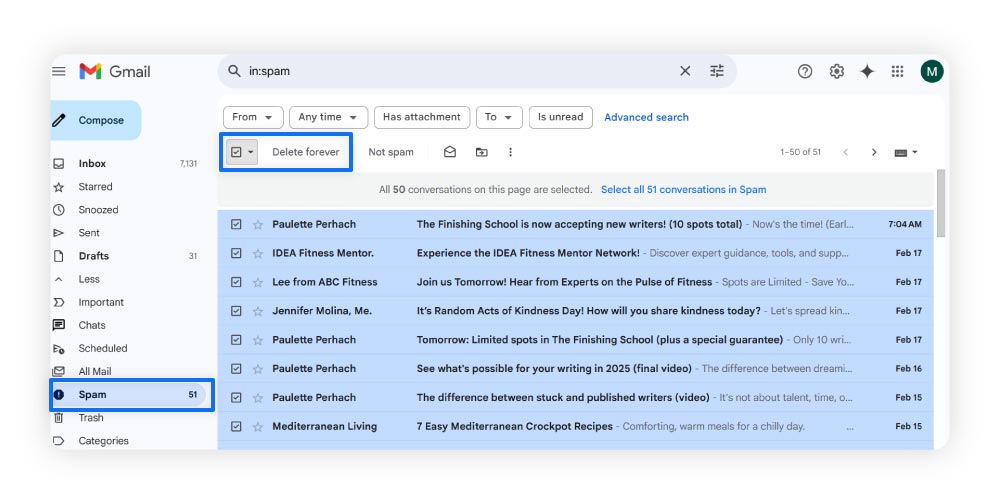
How to delete spam from Gmail
To delete spam emails in Gmail, you can delete individual emails or use the following steps to delete all the emails in your spam folder.
- Expand More in the main menu on the left side of your Gmail account and select Spam.
- Mark the checkbox above your spam emails to select them all, then select Delete forever.
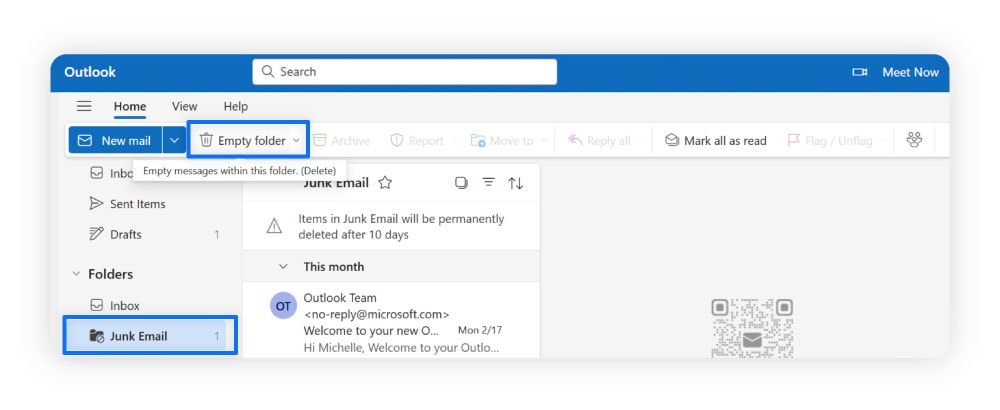
How to delete spam from Microsoft Outlook
To delete spam emails from Outlook, you can delete individual emails or use the following steps to delete emails in the Junk Email folder.
- Click on the Junk Email folder.
- Select Empty folder to delete all spam messages in the Junk Email folder.
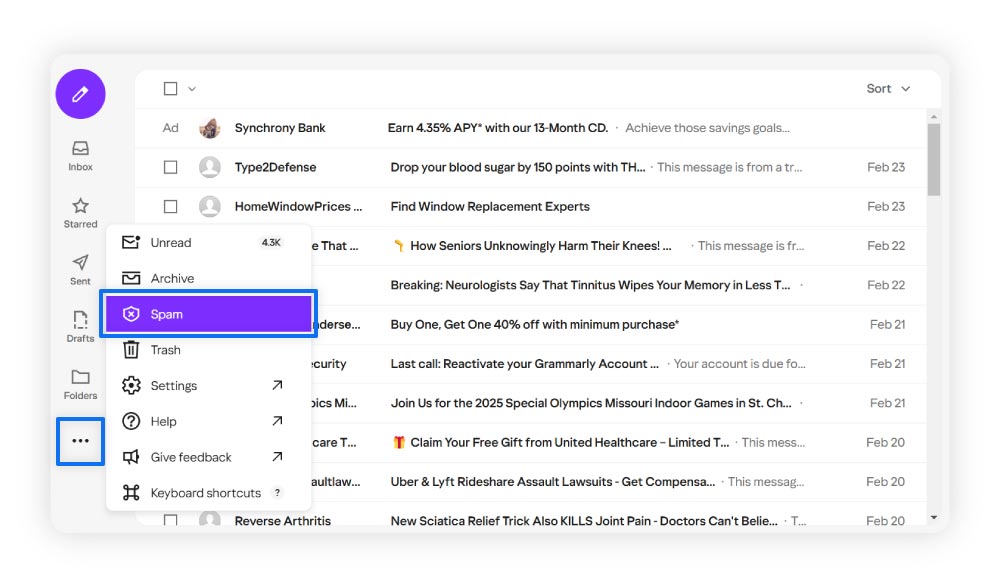
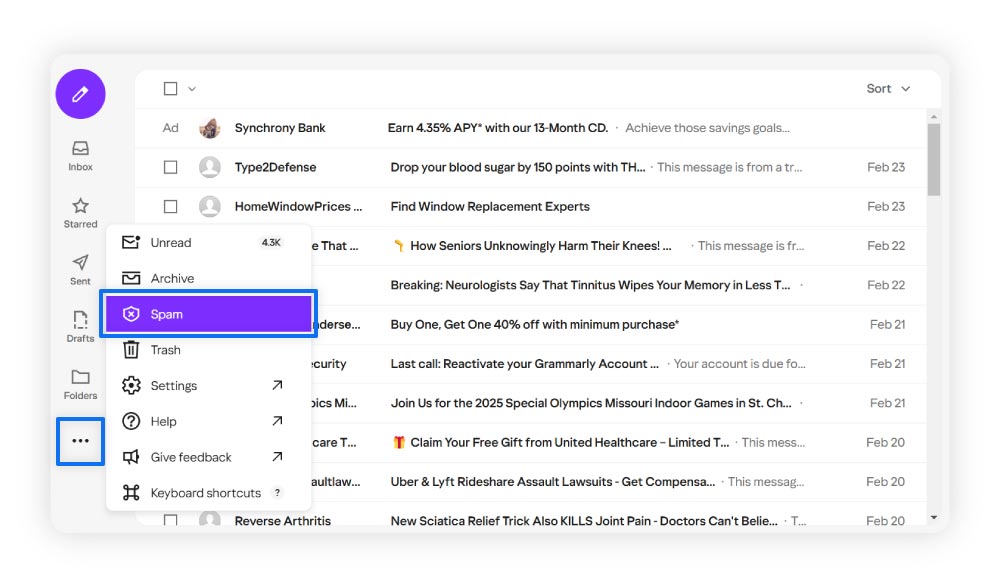
How to delete spam from Yahoo Mail
To delete spam emails from Yahoo Mail, you can delete individual emails or use the following steps to delete all emails in the Spam folder.
- Click the three dots at the bottom of the navigation menu on the left of your screen.
- Select Spam. Then, mark the checkbox at the top of your screen to select all spam messages.
- Click the trash can icon to delete all selected messages.
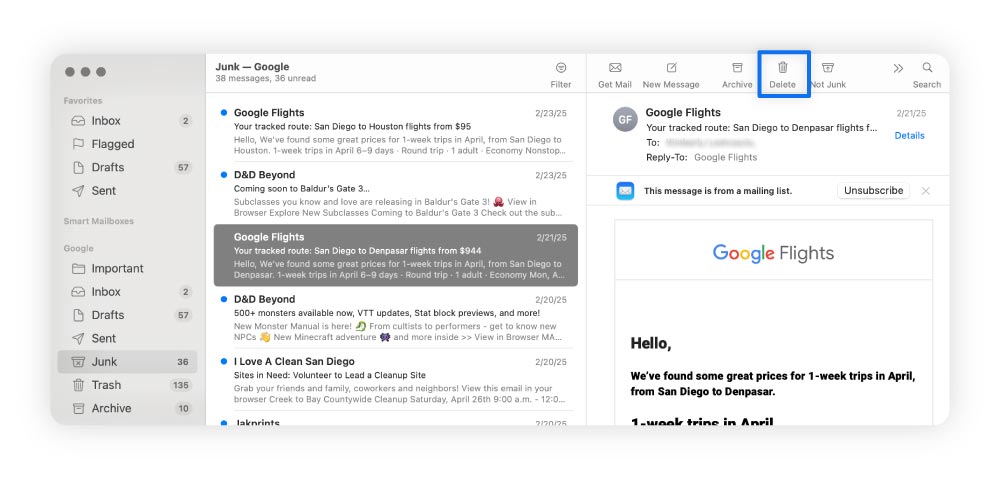
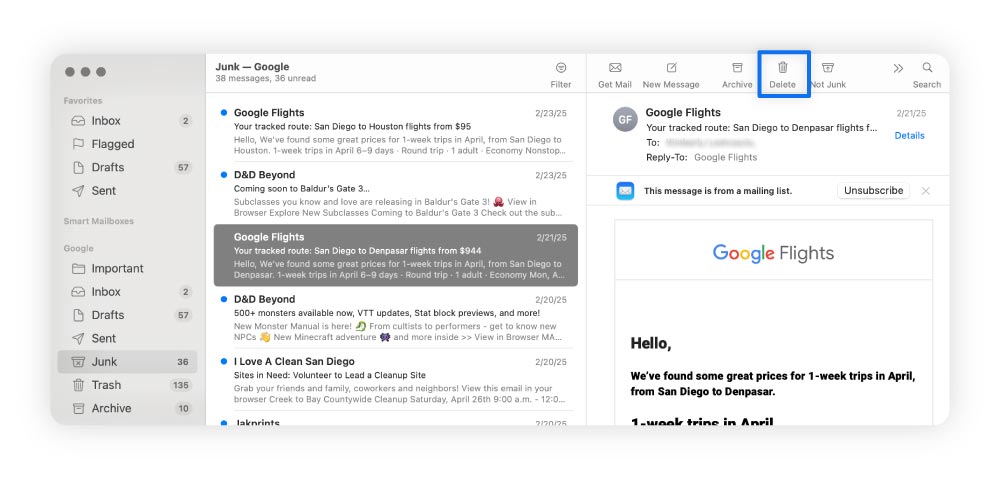
How to delete spam from Apple Mail
To delete spam emails from Apple Mail, you can delete individual emails or use the following steps to delete emails in the Junk Mail folder.
- Select the Junk option in the left side menu.
- Press Command + A to select all the emails.
- Click the trash can (Delete) icon.
3. Block spam senders
Blocking spam senders prevents unwanted messages from reaching your inbox by automatically filtering emails from specific addresses into the spam or trash folder. This helps protect you from phishing attacks by stopping potentially harmful emails from landing in your main inbox.
Here's how to block spam emails in Gmail, Outlook, Yahoo, and Apple Mail.
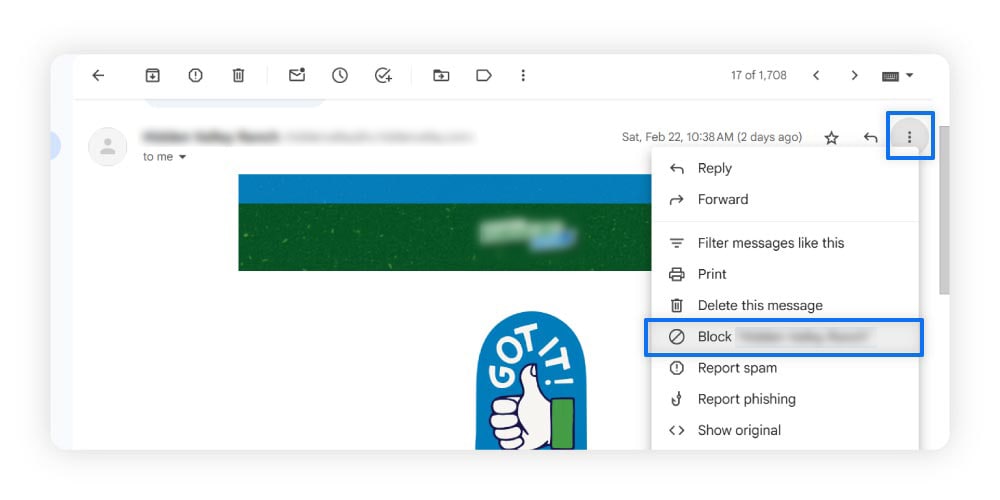
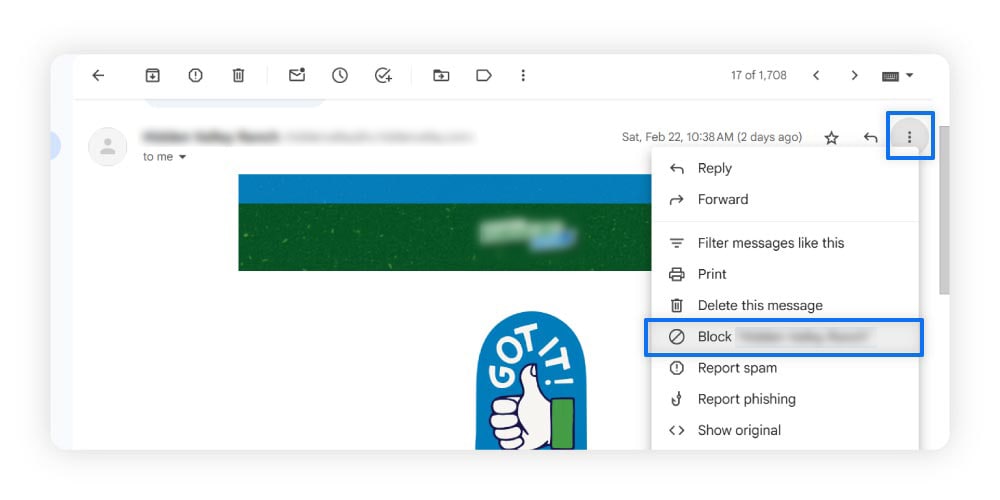
How to block spam in Gmail
Use the following steps to block spam emails in Gmail.
- Open the message from the sender you want to block.
- Select the three dots at the top right of the email.
- Click Block “[sender]”.
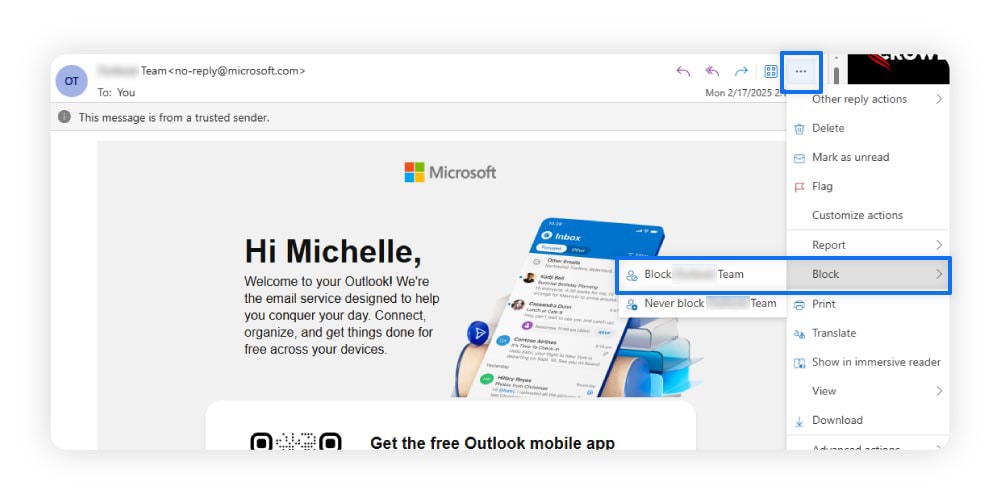
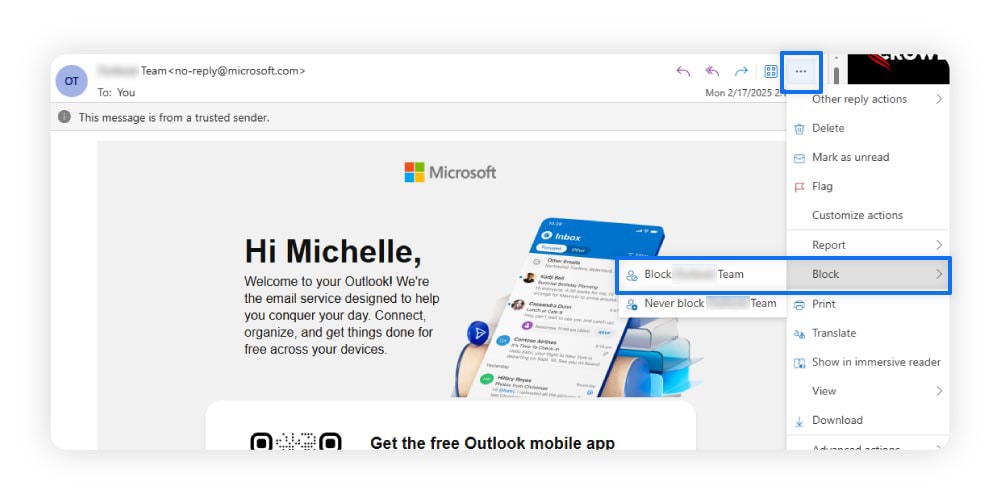
How to block spam in Microsoft Outlook
Use the following steps to block spam emails in Outlook.
- Open the message from the sender you want to block.
- Select the three dots at the top right of the email.
- Hover over Block, then select Block “[sender]”.
How to block spam in Yahoo Mail
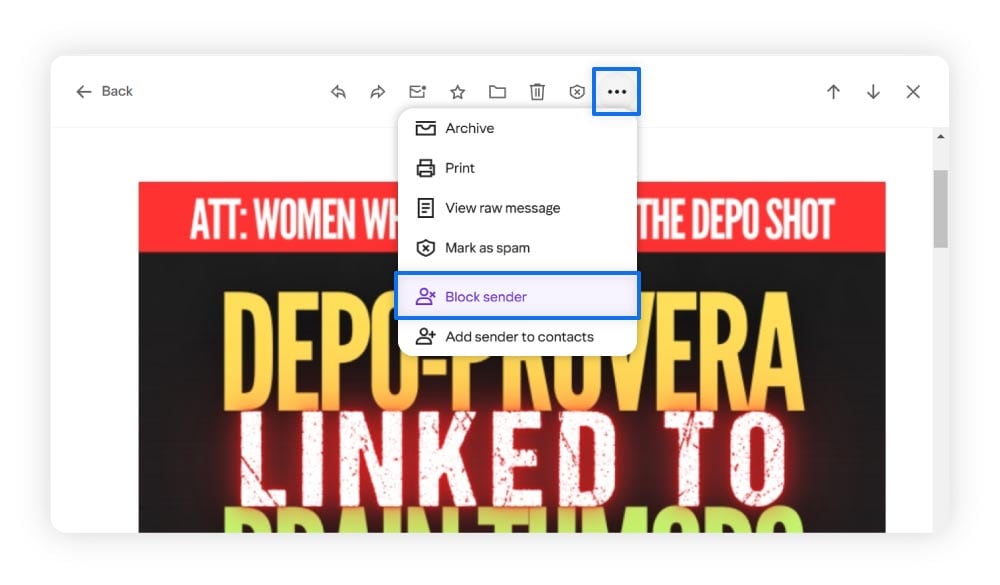
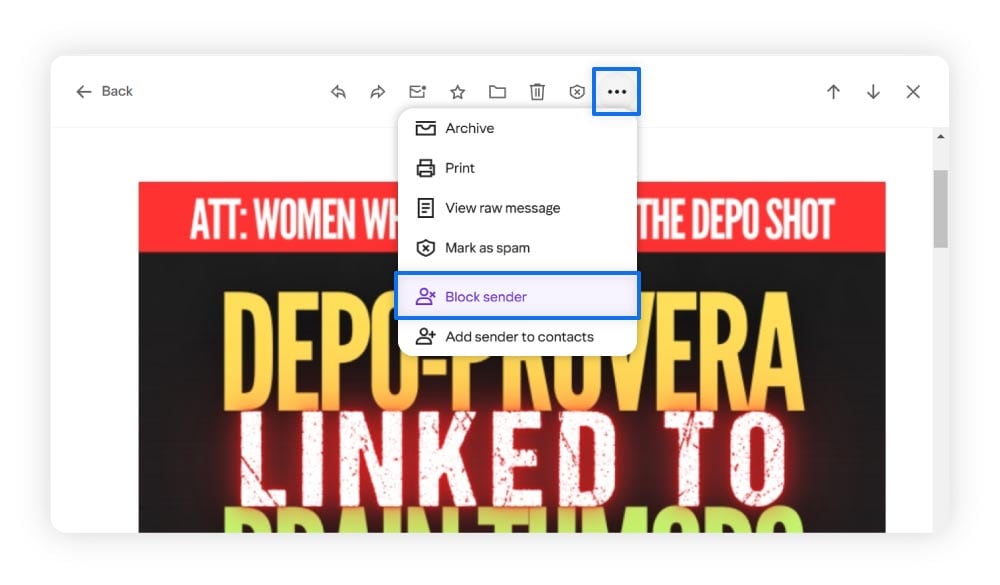
Use the following steps to block spam emails in Yahoo Mail.
- Open the message from the sender you want to block.
- Select the three dots above the selected email.
- Select Block sender.
How to block spam in Apple Mail
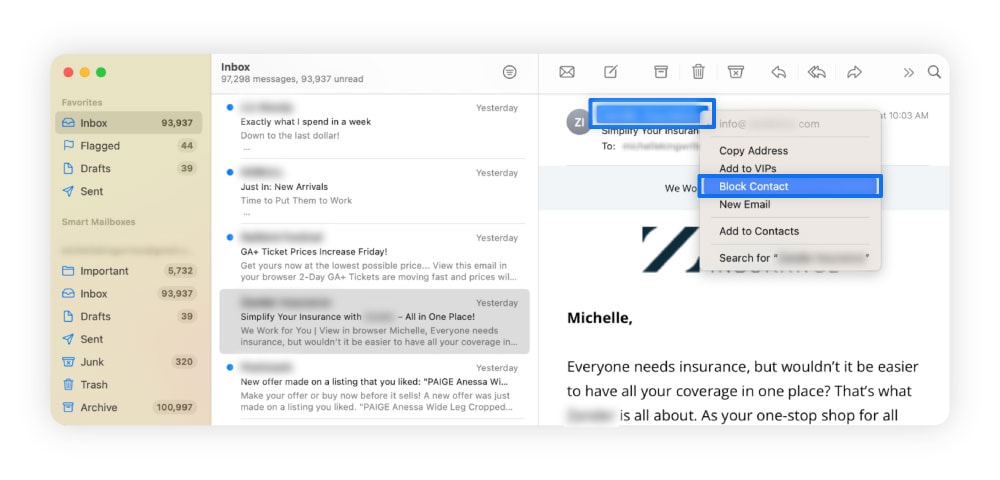
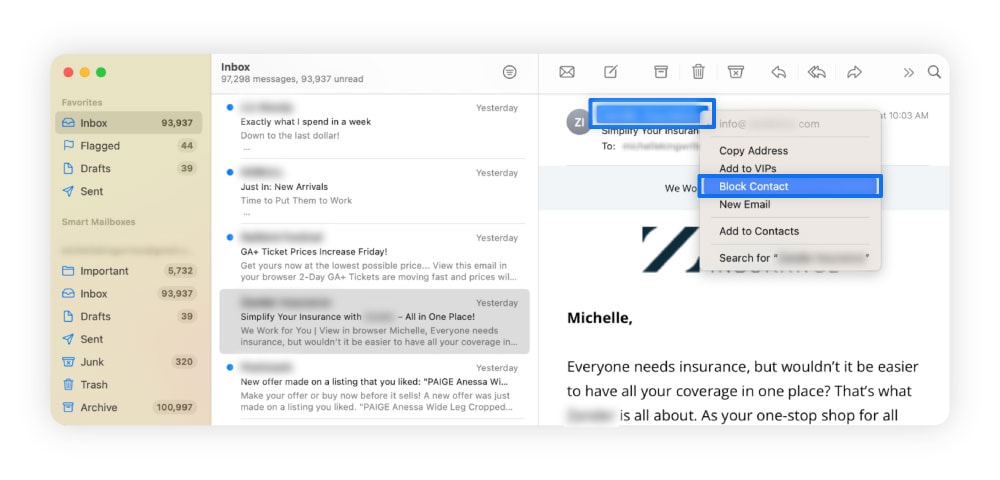
Use the following steps to block emails in Apple Mail.
- Select the email from the sender you want to block.
- Navigate to their name in the message header. Click the arrow and select Block Contact.
4. Keep your email address private
Giving out your email address can increase the number of spam emails you receive. To safeguard your email and reduce spam, avoid sharing it unnecessarily. Doing so reduces the likelihood of receiving malicious emails and limits the risk of exposing your personal information.
Also, consider adjusting your email privacy settings for added protection. Here’s how you can do this in Google, Outlook, Yahoo, and Apple Mail.
Google privacy settings
Use the following steps to view and manage your Gmail privacy settings.
- Go to your main Google account and log in if you need to.
- Select Data & privacy in the navigation menu on the left of your screen.
- Check your privacy settings, including the information you’re sharing with others and who can see it.
Microsoft Outlook privacy settings
Use the following steps to view and manage your Outlook privacy settings.
- Click your account icon in the upper-right corner of the screen.
- In the menu list, click My Microsoft Account.
- Navigate to the Privacy section to change the settings.
Yahoo Mail privacy settings
Use the following steps to view and manage your Yahoo Mail privacy settings.
- Open your Yahoo account.
- Click your profile icon in the top right corner. Select Manage account or Account Info.
- In the navigation menu, select Privacy Controls or Privacy Dashboard.
- View, manage, and update your privacy settings.
Apple Mail privacy settings
Use the following steps to view and manage your Apple Mail privacy settings.
- Click the apple icon in the upper-left corner of the screen.
- Click on System Settings, then Privacy & Security.
- Scroll to Mail Privacy Protection (if available) and adjust settings like blocking email trackers.
5. Use a third-party spam filter
Your email service provider may have its own filter, but pairing it with a third-party spam filter can provide an additional layer of cybersecurity. The emails will travel through two spam filters to reach your inbox. So if it gets through one spam filter, the other should catch it.
Effective spam filters can help protect your devices against malware threats, phishing attacks, and undesirable content. Look for an anti-spam filter that works with your email provider and addresses your unique needs.
6. Unsubscribe from email lists
Unsubscribing from email lists is an ideal way to keep a low profile and protect your email. Marketers often get your email address from online forms, social media, and scraping tools or purchase your information from other companies. So, the less you subscribe to, the fewer places marketers and spammers can find your address.
The Federal Trade Commission requires companies that send commercial or bulk emails to comply with the CAN-SPAM Act. The law helps set rules and requirements for messages sent. One of the rules is that companies must always provide information on how to opt out of their marketing emails. Non-compliance with these regulations can incur penalties of up to around $53,000.
While the law doesn’t prevent marketers from sending spam emails, it does provide a way to stop them from filling your inbox if you choose.
7. Check if your email is on the dark web
The dark web is a hidden part of the internet that isn’t indexed by traditional search engines and is often associated with illegal activities, including the sale of stolen data. If your email address shows up on the dark web, it likely means it was exposed in a data breach or leak and circulated among cybercriminals.
As a result, you may experience a surge in spam emails, with scammers using your compromised information to target you with phishing attempts.
One way to stay safer is to get Norton 360 Deluxe, which comes with a Dark Web Monitoring§ tool. If we find your email or other personal data exposed, we’ll let you know so you can take steps to protect yourself like changing your passwords.
8. Use email aliases for sign-ups
A simple way to reduce unwanted emails is by using an alias. An email alias is a secondary address that forwards messages to your primary inbox without exposing your actual email. For example, if your main email is jane.doe@gmail.com, you could use an alias like jane.doe.sales@gmail.com for business inquiries.
Aliases help keep your inbox organized and secure. You can create unique addresses for newsletters, online accounts, or other sign-ups, reducing spam by keeping suspicious messages separate. If an alias starts receiving too much spam, you can delete or disable it without affecting your main email.
Here are some alias options by email provider:
- Gmail: Add “+” and a word to modify your existing address when signing up for services (e.g. jane.doe+sales@gmail.com) — you’ll receive any newsletters or communications as usual. Or sign up for a completely new address.
- Outlook: Create aliases directly in your Microsoft account settings.
- Yahoo Mail: Use the “Disposable Email Address” feature.
- Apple Mail: If you’re signed in with an iCloud+ account, use “Hide My Email” to generate random email addresses when signing up for services.
9. Disable autoload for images
Autoload images are embedded in emails and automatically load when you open the message. While they may seem harmless, these images can contain tracking pixels that notify spammers when you’ve opened their email, confirming your address is active and making you a target for more spam.
To protect your privacy and reduce spam, consider disabling autoload for images in your email settings. For most email services, go to your settings or preferences, find the “Images” or “External Content” section, and choose the option to block or disable automatic image loading.
10. Opt out of data broker directories
A data broker gathers and sells personal information, like your email address, to marketers or advertisers. Some data brokers, like people search sites, may even share this info for free. It could be used to target you with ads, which can lead to an influx of spam emails. Opting out of these directories helps limit the exposure of your personal data and can reduce junk mail.
To opt out, start by identifying which data brokers have your information. Websites like PrivacyRights.org can help. Visit each broker’s opt-out page, follow their specific instructions, and provide the required information to remove your data.
If you’re not sure where your personal information is stored or don’t have time to pore through data broker sites, use a service to track it down. Norton 360 Deluxe offers a Privacy Monitor feature that scans common people-search sites for your information and helps you request to opt out. With other tools like anti-scam protection and a VPN, this cybersecurity package helps ensure your data stays safer and more private.
11. Change your email address
If your inbox is overflowing with spam, important emails are getting lost, or your email address has been compromised in a data breach, it’s time to consider changing your email address.
When setting up a new email, it might be helpful to forward emails from your old account during the transition period. It’s a practical step during the transition, as it means you still receive important messages while you update your contacts and accounts. Gradually phasing out the old address helps make the switch smoother and minimizes disruptions.
Why am I getting spam emails?
You could be getting spam emails because your email address was exposed in a data breach, sold by data brokers or on the dark web, or collected from public sources. Spammers target these lists to flood your inbox with unwanted and potentially harmful messages.
Common spam email security threats
Spam emails aren’t just annoying — they’re also dangerous, as some contain viruses, malware, and other threats.
Here are a few risks to watch out for:
- Trojan attacks: Trojan viruses disguise themselves as legitimate programs, often hiding in free software downloads or email attachments. Once opened, they install malicious code like spyware or viruses to harm your computer.
- Zombie malware: Zombies are malware hidden in email attachments that hijack your computer to send spam or attack websites, often causing slow performance or battery drain. To avoid them, don’t open attachments or click links in spam emails.
- Phishing emails: Phishing emails often mimic legitimate sources to trick you into entering personal information on fake websites accessed through a sketchy link. They may ask you to verify your password or credit card details. Always verify an email’s legitimacy before clicking links or sharing sensitive information.
- Lottery scams and fake offers: Scammers may use fake lottery winnings and exclusive offers to trick you into sharing personal information. Watch for subject lines with urgent phrases like “immediate” or “act now,” as these are common red flags for scams. And if you haven’t entered the said competition, it’s nearly certainly a scam.
How to spot spam emails
It’s important to know how to recognize the warning signs of spam. Identifying suspicious elements in an email can help you spot spam or scams before it becomes a problem.
Here are some key things to look for:
- Generic greetings: Spam emails often use vague greetings like “Dear Customer” instead of addressing you by name.
- Suspicious sender address: If the sender’s email address looks unfamiliar, is misspelled, or contains random numbers or characters, it could be a sign of spam, or worse.
- Poor grammar and typos: Spam phishing emails often contain noticeable grammar mistakes, awkward phrasing, or misspelled words.
- Threatening language: Emails that use scare tactics or threats, such as saying your account will be locked or your security is at risk, are common characteristics of scammy spam emails.
- Unsolicited offers: Offers for products or services you didn’t request, especially if they seem too good to be true, are likely spam emails.
- Suspicious links or attachments: Be cautious of emails that contain links or attachments you weren’t expecting, as they might lead to malicious websites or contain harmful files.
Protect against spam email threats with Norton
By following the steps above, you can reduce the number of spam emails you receive and the cybersecurity risks associated with them. Now, get Norton 360 Deluxe for added protection against spam email threats. Norton provides real-time protection against malware that spam emails may contain, so even if that pesky spam gets past your defenses, it doesn’t leave you defenseless.
In addition, Norton 360’s AI-powered scam detection capabilities can help you spot cleverly disguised scams and phishing attacks in spam emails before you fall victim.
FAQs
How can I permanently stop spam emails?
It’s nearly impossible to eliminate all spam emails from your inbox, but you can significantly reduce them by marking unwanted messages as spam, blocking senders, unsubscribing from unnecessary lists, using a third-party spam filter, and keeping your email address private.
What’s the difference between a spam email and a phishing email?
Spam emails are unsolicited messages that can have legitimate purposes, like marketing, while phishing emails are deceptive attempts to steal personal information or money. Some spam emails can also be phishing attempts.
How do I know if a spam email is dangerous?
A spam email is likely dangerous if it asks for personal information, includes suspicious links or attachments, has urgent or threatening language, or comes from an unfamiliar sender.
§ Monitoring is not available in all countries and varies based on region.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.






Want more?
Follow us for all the latest news, tips, and updates.