Computer viruses: How they spread and tips to avoid them
A computer virus is a malicious code or program designed to spread from one computer to another, causing damage to data and system operations. Learn how viruses work, signs to look out for, and the main types. Then, get Norton AntiVirus Plus to shield your device against online threats and help protect your digital life.

What is a computer virus?
A computer virus is a type of malware created to replicate and spread itself across computers. Computer viruses spread digitally from host to host, infecting systems and replicating themselves as they go, similar to how a flu virus spreads through a population.
And, just as a flu virus relies on a host cell for reproduction, a computer virus requires specific programming—often embedded in files or documents—to replicate and spread through digital systems.
Below, we’ll discuss common computer virus symptoms, examples of well-known viruses, and tips to get rid of a virus if your device gets infected.
What causes a computer virus?
Hackers spread computer viruses by creating malicious code that can get inside a computer system, modify it, and spread to other computers. A virus infects devices and spreads by attaching itself to legitimate programs or documents that support macros, enabling it to execute its code.
Most people unknowingly spread viruses from one computer to another by opening links to infected sites, installing unsafe software, or not taking the right steps to protect themselves from computer viruses.
How do computer viruses spread?
Malicious software spreads when unsuspecting users interact with infected digital assets. When a virus makes its way onto a device, it creates copies of itself and begins filling the computer's hard drive, spreading to other devices, or both. Viruses are commonly spread through email, text messages, and by downloading infected software.
Here’s how computer viruses work.
1. A virus infects a file or system
Computer viruses attach themselves to a piece of software, an online program, a file, or a piece of code. They can spread through email and text message attachments, files you download online, or scam links sent on social media.
2. An unsuspecting user executes the virus's code
Once attached, the virus lies dormant until an unsuspecting user executes the code or program. The user must run the infected program to infect your computer, activating the virus code. This means a virus can remain dormant without showing any noticeable signs.
3. The virus spreads
Once a computer is infected, the virus can spread to other computers on the same network and cause damage by stealing passwords, logging keystrokes, corrupting files, or sending spam emails to contacts. While some viruses can be relatively harmless, others can have profound and damaging effects, leading to data loss, permanent hard disk damage, or financial losses.
What are the signs of a computer virus?
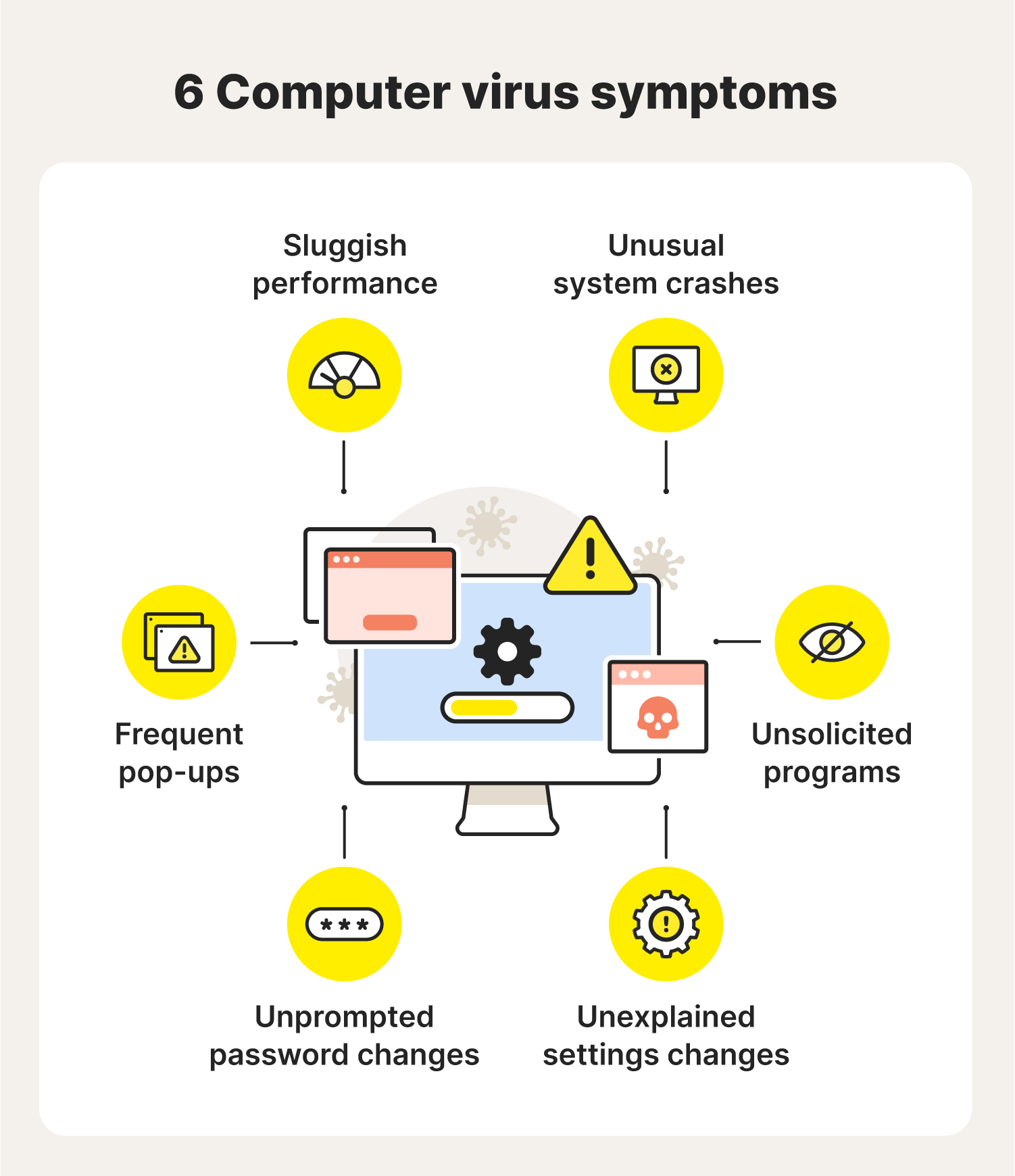
While computer viruses can work discreetly, they often come with a few tell-tale signs. Slow performance, unexpected pop-ups, and unexplained changes in settings can indicate a potential threat.
Recognizing a computer virus infection begins with paying attention to unusual system behavior. Watch for the following computer virus warning signs:
- Frequent pop-ups: Intrusive or suspicious pop-up windows are common signs of a computer virus. These pop-ups might encourage you to visit unusual sites or prod you to download fake antivirus software.
- Sluggish performance: A slow computer, or slower-than-normal processing speed, could be a sign that your computer has a virus.
- Unusual system crashes: Frequent and unexpected crashes or freezes on your device can indicate a computer virus has damaged your hard drive. It may also prevent your device from coming back on.
- Unknown programs: If new, unsolicited, and unfamiliar software or icons appear on your desktop when you start your computer, it may indicate a virus.
- Unprompted password changes: Unexplained password changes that prevent you from logging into your computer are often signs of a virus. (Maintaining strong password security can help prevent this.)
- Unexplained settings changes: An infected computer may lead you to find alterations to system settings that you didn’t do yourself.
Types of computer viruses
There are various types of computer viruses, each with its own signatures and threats. While there are countless computer virus names, types, and sub-varieties, these are some of the most common.
Boot sector virus
This type of virus can take control when you start—or boot—your computer. It can spread by plugging an infected USB drive into your computer.
Web scripting virus
This type of virus exploits the code of web browsers and web pages. If you access such a web page, the virus can infect your computer.
Browser hijacker
A browser hijacker takes over certain web browser functions that may automatically direct you to a potentially compromised website.
Resident virus
This is a general term for any virus that inserts itself into a computer system’s memory. A resident virus can execute anytime when an operating system loads.
Direct action virus
Direct action viruses are activated when you execute a file containing a virus. Otherwise, the virus remains dormant.
Polymorphic virus
A polymorphic virus changes its code each time an infected file is executed. It does this to try to evade antivirus programs.
File infector virus
This common virus inserts malicious code into executable files that are used to perform certain functions or operations on a system.
Multipartite virus
This kind of virus infects and spreads in multiple ways. It can infect both program files and system sectors.
Macro virus
Macro viruses are written in the same macro language used for software applications. Such viruses spread when you open an infected document, often through email attachments.
How to avoid computer viruses
Use strong antivirus software to help avoid computer viruses. Here are some more tips to help secure your computer against malicious software.
Use reliable antivirus software
Use trusted virus protection software like Norton AntiVirus Plus, which automatically updates to help protect against new and emerging virus threats.
Enable automatic scanning
Configure your antivirus software to automatically scan email attachments or file downloads. You can usually find this feature in the settings or preferences menu of the antivirus program.
Stay on top of software updates
Staying on top of your software updates is a simple way to patch up potential vulnerabilities on your computer. Be sure your operating system, browsers, and other software are regularly updated.
Be wary of email attachments
Email attachments are a common target for viruses to attach themselves to. Avoid opening attachments or clicking links from unknown or suspicious senders, because it could be a phishing attack. Use your antivirus software to scan attachments before opening them.
Don’t click on pop-ups
Unprompted or unwanted pop-ups can contain viruses. Avoid clicking pop-ups on your phone or computer while online. And don’t visit unsafe or dangerous websites.
Download wisely
Only download software and files from trustworthy sources, and always scan the files you download using your antivirus software.
Backup your data
It’s wise to regularly back up your data and important files to an external drive or a secure cloud storage service. That way, you can lessen the impact of potential data loss if your computer is impacted by a virus or another form of malware, like a type of ransomware.
Defend your digital space
Once you understand how computer viruses work, you can take the simple (but crucial) steps to stop them. Maintaining software updates, ensuring you have proper email security and downloads, and backing up important data are practical ways to secure your digital space.
But parts of the internet are awash with viruses, and new stains are appearing all the time. That's why you should use reliable antivirus software like Norton AntiVirus Plus—it carefully scans your devices to help block viruses, malware, ransomware, and hackers to keep you safer online.
FAQs about computer viruses
Still have questions about computer viruses? Find answers below.
Is ransomware a virus?
While often confused as a virus, ransomware is a type of malware that encrypts files on a user's system, making them inaccessible until they pay a ransom to the attacker. While not a traditional virus, it significantly threatens data security.
Is a trojan a virus?
A trojan is a type of malware that disguises itself as legitimate software to deceive users. While trojans share similarities with viruses, they do not self-replicate.
What is a computer worm?
A computer worm is a standalone type of malware that replicates itself to spread across networks, often exploiting vulnerabilities. Unlike viruses, worms don't need a host program to attach to and can operate independently, making them a distinct type of malware.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.








Want more?
Follow us for all the latest news, tips, and updates.