What is data security? Key principles and protection strategies
Data security means protecting corporate and personal information against unauthorized user access, but not everyone knows what that takes. We’ll explain all things data security: what it is, what risks are involved, common protection tips, and ways dedicated software can help maximize your overall Cyber Safety.

Data security is especially important if you or your business relies on the cloud to store sensitive information. That’s because without good data security, the information you’re storing is more vulnerable to data breaches and cyberattacks.
This guide will help you understand why data security is important and introduce real-world data security risks. Plus, you’ll learn about helpful data security practices you can incorporate to help protect your information.
What is data security?
Data security is the process of protecting sensitive information (both corporate and personal data) from unauthorized access, breaches, or theft. Doing this requires implementing security safeguards such as encryption and specific user access controls to protect sensitive data.
Data security also encompasses policies and procedures for data management and retention, as well as compliance with legal and regulatory requirements specific to where the data is being stored.
What’s the difference between data security and data privacy?
The biggest difference between data security and privacy is that data security involves how your data is protected against any type of unauthorized access, while data privacy relates to who can access it, how, and where it can be used.
Data security often involves tools such as encryption and firewalls to protect important information from being leaked or hacked in a breach. For data privacy, organizations are typically more concerned with set policies on how and for how long they can retain your data, or on how to remain in compliance with local, federal, and industry privacy regulations.
What are the core principles of data security?
The core principles of data security are confidentiality, integrity, and availability. Together, these three principles (often called the Information Security Triad or the CIA Triad) inform how organizations ensure sensitive information remains accurate and unaltered, safe from people who shouldn’t have access, and accessible to authorized users when it’s needed.
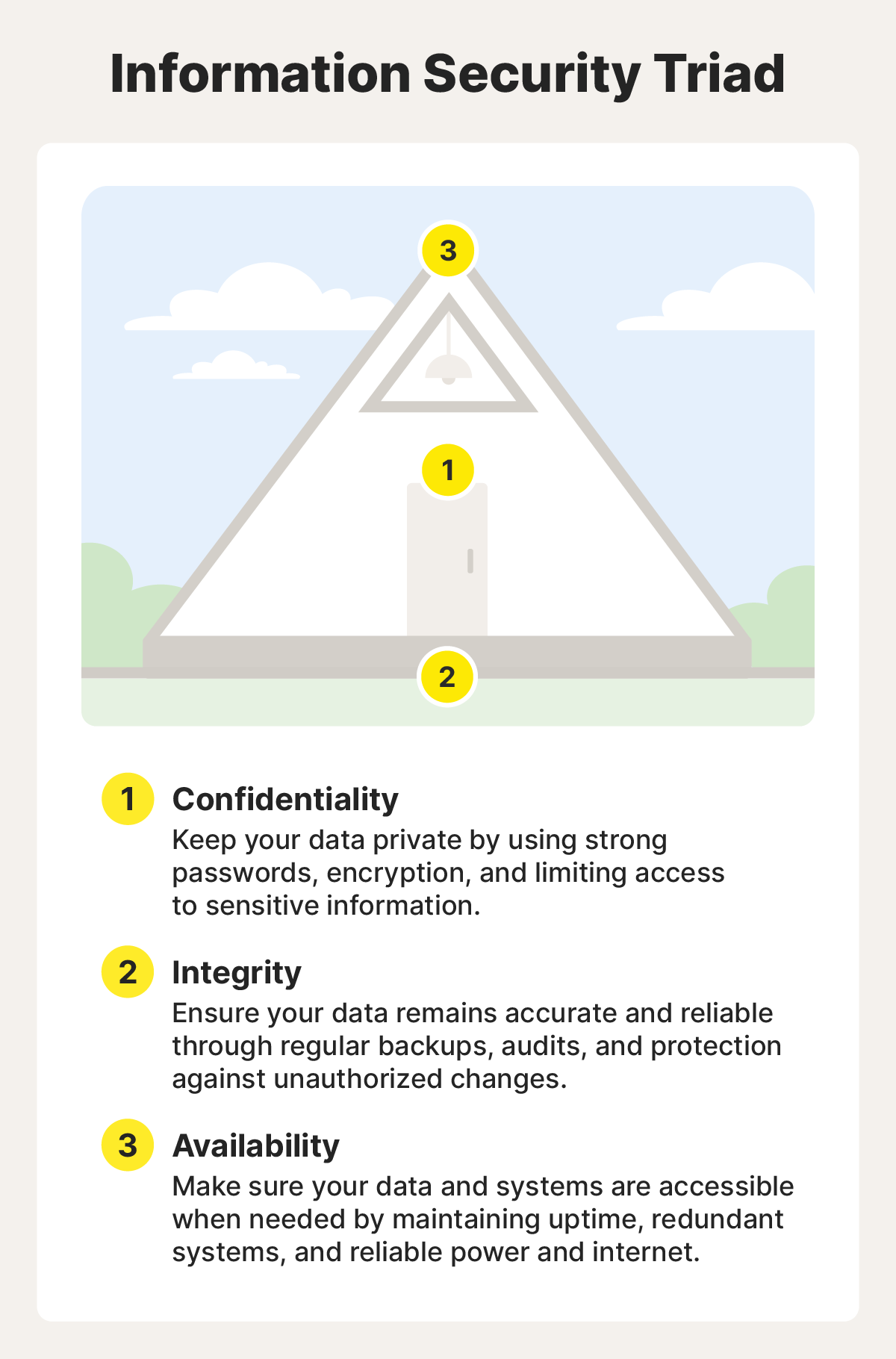
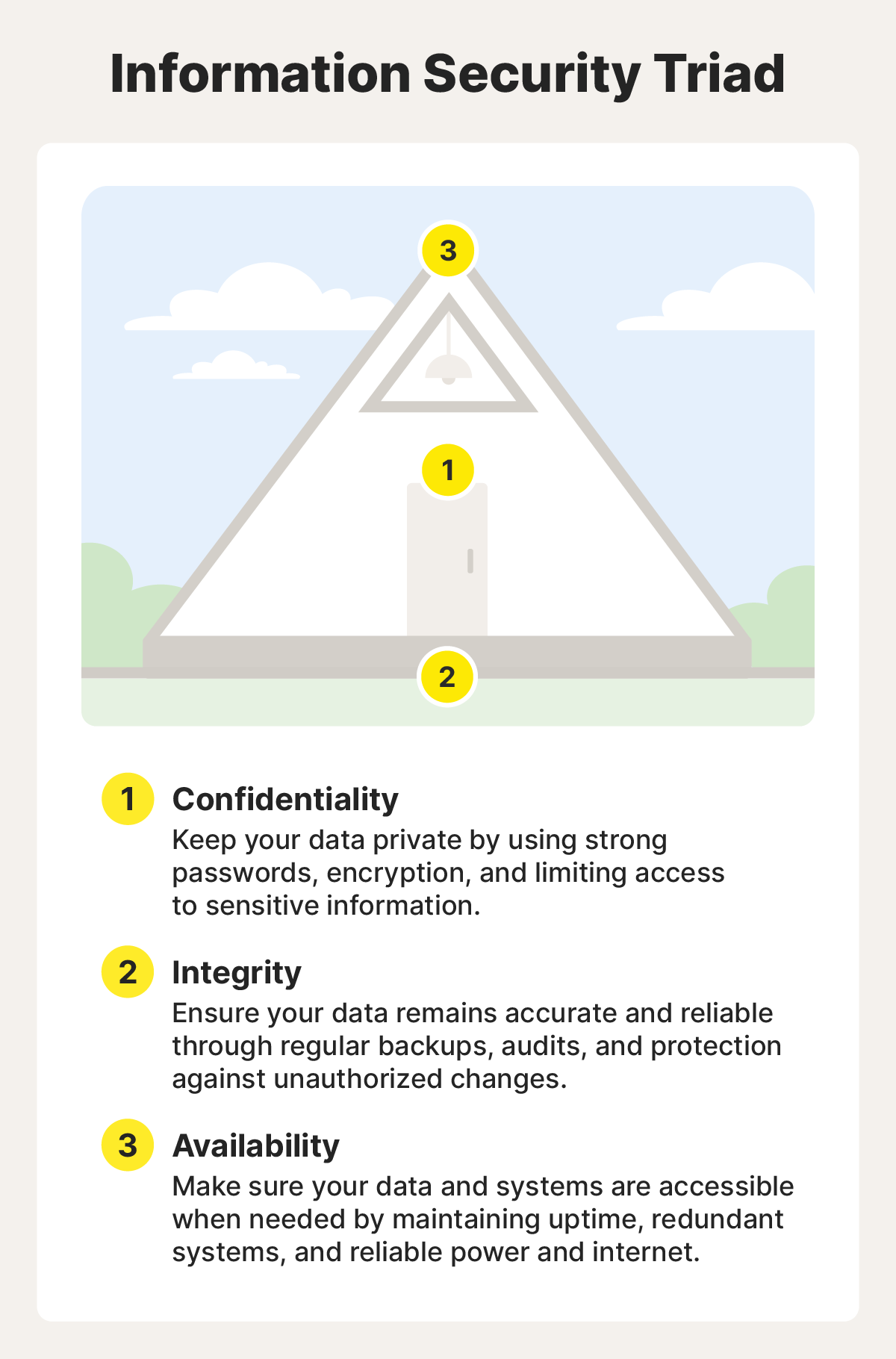
Confidentiality
The principle of confidentiality ensures that data is accessible only to authorized users. It often requires safeguards like strong and secure passwords, encryption, and multi-factor authentication (MFA).
In practice, a company might restrict access to customer records using role-based permissions and MFA, ensuring only authorized employees can view sensitive information. They may also encrypt the data so that even if it’s accessed by a bad actor, it remains unreadable.
Integrity
The second aspect of the triad, integrity, ensures that information is accurate and doesn’t get tampered with. The goal is to keep data protected from modifications that might compromise its reliability, such as a system error that could result in corrupted, unusable files.
For instance, a healthcare provider might use audit logs and version control to track every change made to patient records, ensuring any updates are accurate and can be reviewed or reversed if needed.
Availability
Availability makes data accessible (to authorized people only) when needed, without delay or interruption. This can be done by implementing data security measures, such as system backups and disaster recovery plans, to prevent downtime or data loss during hardware failures or attacks.
For example, in season 2 of the HBO medical drama The Pitt, hospital leadership shuts down the hospital’s internal digital systems as a pre-emptive defense against a ransomware attack. To keep critical patient information accessible during the outage, staff switch to fallback manual workflows, such as using paper records and relying on clerks to track patient information.
This storyline highlights two aspects of availability: medical staff can still access the information they need to treat patients, and leadership protects the data’s long-term availability by shutting down the systems before attackers can lock them down or cause a data breach.
Why is data security important?
In addition to improved protection against data breaches, social engineering, and malware and session hijacking attacks, data security also serves as your first line of defense against today’s hackers. And with at least 375 million people in the U.S. affected by data breaches in 2025 alone, there has never been a better time to start taking it seriously.
Below are some of the key benefits of investing in data security measures:
- Protects sensitive data: Strong data security keeps your personal and financial data safe from breaches and unauthorized access.
- Builds trust: Having data security measures in place demonstrates to customers and other stakeholders that you take their data seriously.
- Ensures legal compliance: Securing your data helps you remain compliant with regulatory requirements such as HIPAA and GDPR, and it also saves you money by avoiding fines and legal costs associated with data breaches.
- Prevents financial loss: Data security can lower your risk of costly expenses or lost business related to security incidents.
- Safeguards intellectual property: Secure data keeps trade secrets and sensitive business details private and away from prying eyes.
Techniques to secure data for individuals
To secure your personal data, use a mix of preventive tools, smart password practices, account-level protections, and recovery strategies.
Below is some more information about tools and strategies you can use to protect the information you care about most, whether that’s smart home data, financial details, or PII.
- Data backups: Whether on your physical device, in the cloud, or on an external hard drive, having a duplicate copy of your information can ensure that you’ll be able to recover information lost in the event of a cyberattack or unexpected system malfunction.
- Firewalls: Firewalls mitigate data security issues by acting as the gatekeeper to your home network; they filter traffic and restrict access from unauthorized parties, alerting you if suspicious activity arises.
- Password hygiene: Strong, differentiated passwords are a defense against hackers taking advantage of techniques such as credential stuffing and password spraying to get their hands on your personal information.
- Two-factor authentication (2FA): 2FA adds an extra layer of security to accounts and devices. It can incorporate biometrics — such as facial features or fingerprints — to verify the identities of users attempting to access.
- Virtual private networks: With tools such as VPNs, people can hide their IP addresses and help camouflage the online trails that cybercriminals like to follow.
- Security updates and patches: By quickly addressing and fixing vulnerabilities in systems or software, you close any loopholes that could be exploited by hackers.
Techniques to secure data for businesses
Businesses must think strategically about protecting data. In addition to satisfying customers, they need to comply with government-enforced regulations, including rules governing the storage of card payment and health information, along with the systems used to do so.
Here are some common data security methods for businesses:
- Access management: Identity and access management involves regulating who may view certain types of data and where they can access it. These guidelines, often outlined in a data security policy, help ensure that confidential data remains inaccessible to unauthorized parties.
- Data erasure: Data erasure is a secure method of permanently disposing of old or unneeded information to keep customer data and trade secrets hidden. Unlike simple deletion, this process ensures files are completely encrypted and unrecoverable.
- Data masking: Similar to encryption, data masking software hides data by interchanging numbers and letters with fake characters. This hides targeted information from cybercriminals trying to gain access, but once the intended party opens or receives the data, it reverts to its original form.
- Data resilience: Data resilience refers to a company’s ability to build a data infrastructure that can withstand and recover from system failures. The data security software and hardware a business uses should be able to survive external threats like natural disasters or power outages without compromising information.
Data security regulations
Regulations protect data security and require organizations to safeguard information properly. In the U.S., federal rules cover health, financial, and consumer data, though state privacy laws vary in strictness. And the EU’s General Data Protection Regulation (GDPR) enforces broader protections.
Here’s a breakdown of the common data security regulations in the U.S. and EU:
- California Consumer Privacy Act (CCPA): The CCPA gives California residents the right to understand what information is collected on them and to request that it be deleted.
- Delete Act: Requires data brokers to register with the California Privacy Protection Agency and, starting in August 2026, to respond to deletion requests that come in through a tool called the Delete Request and Opt‑out Platform (DROP).
- General Data Protection Regulation (GDPR): Sets strict rules in the EU for data processing, consent, and notification.
Additionally, there are industry-specific regulations, such as the Health Insurance Portability and Accountability Act (HIPAA) for healthcare data and the Gramm-Leach-Bliley Act (GLBA), which protects data within financial institutions.
How does AI affect data security?
As AI continues to impact most industries and is increasingly integrated into existing systems, new data security concerns are emerging. AI isn’t inherently dangerous, but because AI tools process massive amounts of information, it’s more important than ever to make sure sensitive information is kept secure.
Deepfakes are a prime example. If photos or images get into the wrong AI-assisted hands, they can be made into very convincing pictures or videos that can be exploited.
Many AI platforms include several layers of data protection. For instance, OpenAI’s tools, such as ChatGPT, adhere to data security regulations and support access controls and permissions. They also regularly undergo third-party security testing.
Some systems include automated compliance monitoring that lets them check data handling in real time to be sure it’s aligned with privacy laws. AI can also anonymize and sanitize data to remove personally identifying information (PII) and reduce its exposure. However, it’s still important that users avoid intentionally sharing PII with chatbots.
Secure your data with Norton
Data security protects your privacy, identity, and digital property. If you’re ready to take control of your business or personal data security, Norton can help.
Norton 360 Deluxe offers a full suite of security features that help you avoid threats like viruses and hackers while safely storing your passwords and other credentials. Plus, you can back up important files to the cloud, get alerts if your data ends up on the dark web, and leverage a VPN for added security.
FAQs
What is cloud data security?
Cloud data security is the practice of protecting data when it is stored in cloud environments. This often uses tools like encryption and access controls to prevent unauthorized access or breaches.
What is data security posture management?
Data security posture management is the process of continuously assessing and improving data security across all of your digital systems. The goal is to uncover any vulnerabilities, enforce policies, and reduce security risks.
What is the Payment Card Industry Data Security Standard?
The Payment Card Industry Data Security Standard (PCI DSS) is a set of requirements that serve to ensure a business securely handles credit card data and keeps it safe from fraud or theft.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.









Want more?
Follow us for all the latest news, tips, and updates.