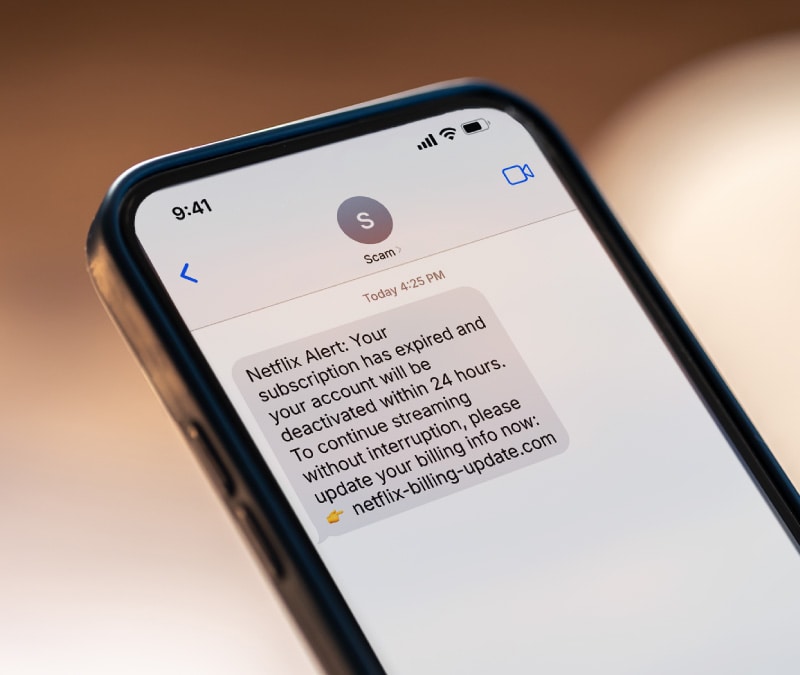
Clicked on a phishing link? Here’s what to do
Clicking a phishing link doesn’t automatically spell disaster. Learn what happens and how to protect yourself from harm.
Published May 06, 2025

























Want more?
Follow us for all the latest news, tips, and updates.