Cybercriminals: Who they are and how to protect yourself
Cybercriminals are constantly launching attacks against businesses, governments, and individuals. Keep reading to learn more about cybercriminals, their motivations, and how tools like Norton 360 Deluxe can help protect against hackers, malware, and other online threats.

What are cybercriminals?
Cybercriminals use computers and the internet to commit crimes. Their motivation may be to commit vandalism, make money, cause political upheaval, or accomplish some other aim. They can use malware, phishing, brute force attacks, information found on the dark web, or other hacking techniques to further their goals.
Cybercriminals operate around the world and commit a range of illegal activities like:
- Buying and selling illegal goods
- Spreading malicious programs like Trojans, rootkits, and spyware
- Stealing identities, money, and other proprietary info
- Cyberstalking and doxxing people
6 common kinds of cybercriminals
Not all cybercriminals are the same. And while their motives and means vary, all of them can cause damage to your devices. Below is a breakdown of some common cybercriminal types to help you recognize the signs and avoid being targeted.
Hackers
The most basic definition of a hacker is someone who uses a computer to look for and take advantage of weak spots in computer systems. While some hackers provide their services as a way of helping governments and businesses patch vulnerabilities, many of them are motivated by money and power.
To gain access to the data they want, hackers deploy malware or engage in social engineering to trick users into giving up their credentials. Once the hacker has access, they may steal as much data as possible before they’re caught or set up a backdoor that provides unfettered access to the system.
Hackers often sell the data to the highest bidder (usually a rival company or government), hold it for ransom, or release it for free to damage reputations and spill secrets.
Scammers
Scammers use social engineering tactics to convince people to provide them with information or money without giving their victims what they promised.
Most internet scams allow cybercriminals to steal money from other people. Some common scam tactics include:
- Phishing: Scammers send fake messages and emails to get people to provide information so the scammer can steal their money or identity.
- Ransomware: These programs let scammers encrypt someone’s data and refuse to decrypt it until they pay a ransom.
- Scareware: A scammer will inject code into someone’s computer that tells them there’s been a security breach and that they need to download more software to stop it.
- Travel scams: With bogus “free” or “discounted” travel offers, scammers can steal credit card information.
- Online shopping scams: By building a spoofed website, scammers can get access to personal information, credit card numbers, and more.
Hacktivists
Hacktivists are cybercriminals who commit crimes in the name of a political, religious, or other ideology. The most common targets of hacktivism are governments, multinational corporations, religious groups, and individuals in power. To accomplish their goals, hacktivists will force their way into websites to crash them, steal information to release it to the public, and even dox people they believe need to be exposed.
While the intentions of some of these individuals may be good, in most cases, they are still breaking the law. Since 2022, the lines between some hacktivist groups and state-sponsored hackers have blurred. Some reports show that there may be direct links between military hackers, civilian hacking groups, and state actors.
Disgruntled employees
For the disgruntled employee, the entire point behind a cyberattack is to cause financial and reputation damage to the organization they work for or used to work for. Many disgruntled employees who launch these attacks against their employers do so because they feel mistreated or fired without cause.
Depending on their access, these employees can cause tremendous damage very quickly. They may damage the company’s internal network, delete data, steal information, and then sell it to rival organizations (or release it to create PR problems).
While it’s easy to assume that this kind of damage can only be caused by employees in the IT department, nearly anyone with some money and access to the dark web can purchase malicious software and upload it to a network.
State actors
State actors are cybercriminals a government employs to commit cybercrime and espionage against other governments and their citizens. With state sponsorship, these cybercriminals commonly have access to a much larger resource pool than others, leading to more dangerous attacks.
Troll farms working to subvert elections and spread disinformation around the world are one example of state actors.
Script kiddies
Script kiddies are cybercriminals (usually younger and less experienced than hackers and other cybercriminals) who launch attacks using the code and programs developed by other people. Their lack of experience doesn’t mean they aren’t dangerous—without the full knowledge of how the code they use works, they can do a lot of damage very quickly.
Lots of script kiddies don’t have a true motivation other than chaos and curiosity. They use other people’s code simply to see the damage it can cause. Their recklessness, impulsiveness, and inexperience mean they get caught more frequently than other criminals, because they can’t, or don’t, mask their actions.

Types of cybercrime
As we’ve seen with types of cybercriminals, internet crimes run the gamut from merely annoying to extremely dangerous. There are many variations on the crimes listed below, but the majority of cybercrime falls into one of the following categories:
- Malware attacks
- Online fraud
- Financial theft
- Identity theft
- Cyberwarfare and cyberespionage
- Cryptocurrency scams
- Downloading, selling, or distributing illegal items and content
- Cyberstalking
Let’s take a closer look at these common examples of cybercrime and the impact they can have.
Malware attacks
Malware, short for “malicious software,” are programs designed to cause harm to a system or to provide access to systems by hackers. There are many types of malware, including:
- Computer viruses
- Ransomware
- Botnets used for DDoS attacks
- Worms
- Rootkits
Cybercriminals create (or buy) malware to attack individuals, businesses, and governments to steal information, destroy data, or reap financial gains.
Online fraud
Fraud is among the most common (and expensive) forms of computer crime. The FTC reported over $5.8 billion in consumer fraud in the U.S. in 2021. Some examples of fraud include:
- Imposter scams
- Online shopping scams
- Credit and debit card fraud
- Identity theft
- Fake job opportunities
The losses caused by fraud are more than financial, though. Stolen identities can mean a loss of job and credit opportunities, not to mention the substantial time it takes victims to report fraud to creditors and authorities.
Financial theft
Because money is one of the primary motivations for cybercriminals, financial theft is very common. Criminals can gain access to victims’ money by:
- Phishing
- Hacking personal devices
- Infiltrating banks and credit card company systems
- Using ransomware
- Scamming people with fake investments
- Extortion
Identity theft
In 2021, the FTC received 1.4 million reports of identity theft, making it one of the most common types of fraud in the country. The variety of identity theft scams makes it difficult to prevent, especially if you aren’t taking steps to keep your data safe.
Cybercriminals can steal your identity with phishing techniques and hacking, and they’ll use the information for themselves or sell it to others. It could mean someone else is using your name to get jobs, make purchases, or even commit crimes.
Invest in identity theft protection, like the kind you can get with Norton 360 with LifeLock Select, to help block hackers from accessing your devices, protect your browsing history with a VPN, and respond quickly if a cybercriminal steals your identity.
Cyberwarfare and cyberespionage
Espionage and warfare are usually the realm of state-sponsored groups, but hacktivists and individuals can also attack infrastructure and other governmental resources digitally. While some forms of cyberespionage and warfare are designed to humiliate or embarrass a target, perhaps by changing imagery or writing on a public-facing website, other types of cyberwarfare result in damaged systems, stolen data, or infiltrated networks that can be spied on.
Cryptocurrency scams
Cryptocurrency scams have led to billions in losses for large funds and individual investors. One of the most common cryptocurrency scams is cryptojacking, where a cybercriminal commandeers a victim’s computing power to mine Bitcoin directly. Or they may convince their victim to let someone else use their computing power to mine crypto in return for a share of the profits.
However, the scammer never shares those profits and never uses the investor’s money to rent servers to mine cryptocurrency. Instead, they steal the money and use that computing power to mine more for themselves.
Downloading, selling, or distributing illegal items or content
Using the internet to download stolen versions of copyrighted material, along with free games, movies, and music, is one of the most popular forms of cybercrime. Along with those types of content, illegal pornography, corporate data, drugs, and malware are also available to people who know where to find it.
Cyberstalking
A cyberstalker uses the internet to track, harass, and otherwise intimidate someone else. Cyberstalking can take many forms, including sending threats, doxxing, posing as the victim, or destroying data. While many cyberstalkers choose people they know, others target people on the opposite side of the political spectrum or a part of a group the cybercriminal dislikes.
Cost and impact of cybercrime
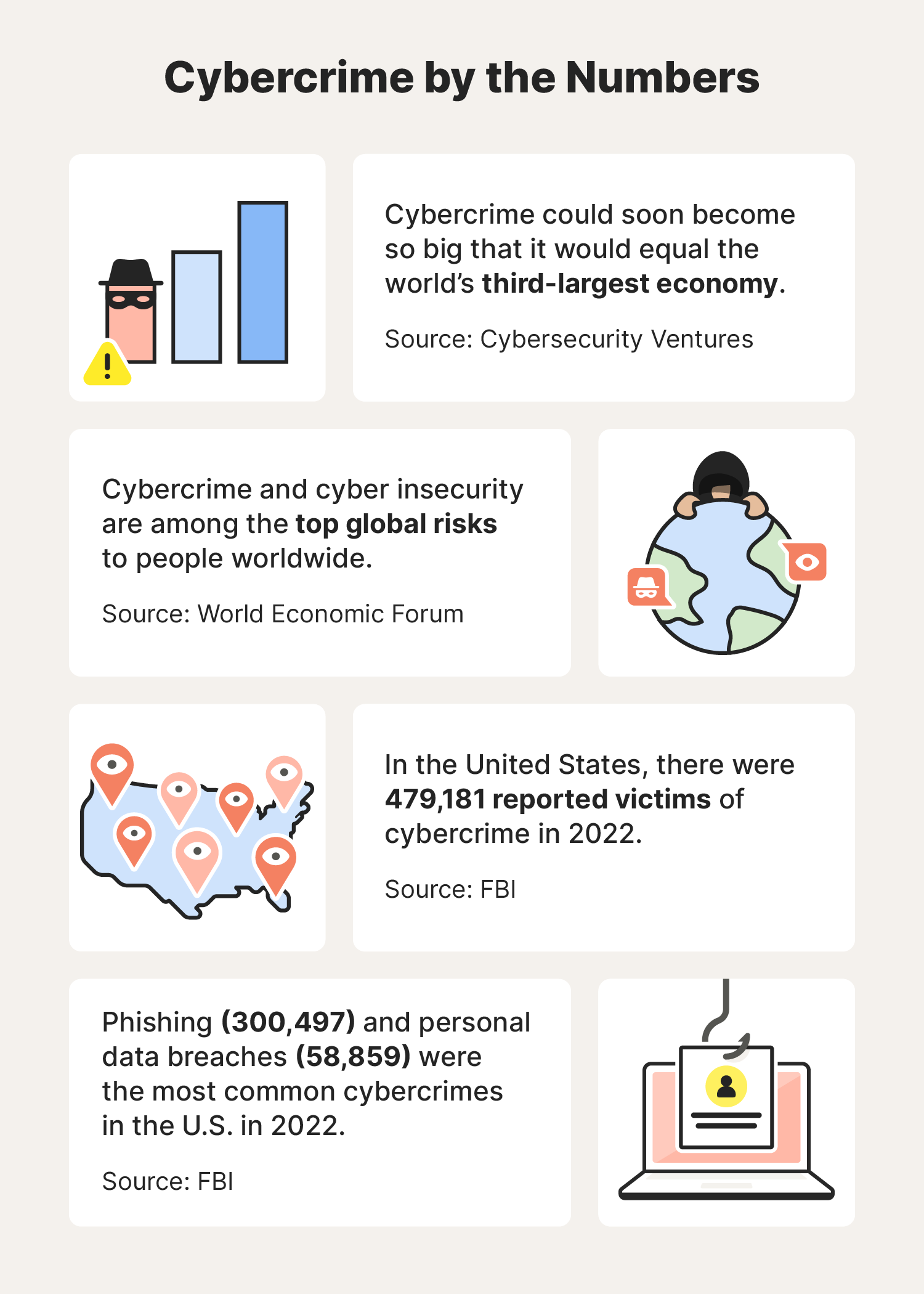
The cost of cybercrime is huge, with one estimate putting the impact at $600 billion in 2018 alone. Other cybercrime reports estimate that the total cost of cybercrime could soon grow to a size roughly equivalent to that of the third-largest economy in the world. A troubling cybersecurity statistic is that there were almost 500,000 victims of cybercrime in the U.S. in 2022.
Governments worldwide have created laws to punish cybercriminals, but cooperation between governments is lagging. The U.S. Government Accountability Office believes that the positive impacts of sharing information and training other countries to deal with cybercrime are important steps that haven’t been fully evaluated yet.
How to report a cybercriminal
You should always report cybercrime to the proper authorities. By doing so, you can help them learn more about individual criminals and the intricacies of the scams and crimes they commit. If they stole from you, reporting it may be the only way for your bank and credit card company to reimburse or remove fraudulent charges. Follow these steps to help reduce the impact of cybercrimes:
- Report a cybercrime to law enforcement. Local law enforcement and federal agencies may be able to help if the criminal is working in your area. They can also catalog and pass on cybersecurity reports and relevant information to other investigators. The FTC has a website for reporting cybercrime that will also guide you to resources for recovering stolen money and securing stolen identities.
- Report cybercrime to relevant platforms. You should report cybercriminals to the platforms they use to commit their crimes. This can help these companies identify weak spots in their security.
5 tips for protecting against cybercriminals
Learning to protect yourself from cybercrime can be pretty straightforward, but there is no guarantee that even the best preventative measures will work all of the time. But taking a few simple cybersecurity steps, like those listed below, can make you a more challenging target.
- Use strong passwords: Password security means never repeating passwords, never sharing passwords with anyone, and always using passwords that are long and complex. Using a password manager can help you keep track of your passwords.
- Keep software updated: Developers release updates to fix potential vulnerabilities that cybercriminals could exploit. Using the auto-update features on your devices helps keep your software updated to protect you from threats.
- Beware of phishing attempts: While some types of phishing are obvious, others are subtle and seemingly harmless. Don’t click on links from people you don’t know, and never give out information that can enable someone to impersonate you.
- Educate yourself and stay informed: The world of cybercrime moves fast. As new types of malware are developed, and new ways of scamming people are refined, dealing with cybercrime feels inevitable. Research cybercrime every few months to help you keep up with the newest ways criminals might try to take advantage of you.
- Use reliable security software: The simplest and most powerful way to protect yourself from cybercrime is with security software. Security software like Norton 360 Deluxe helps stop malware from getting onto your devices, warn you about potential threats on unsafe sites, and alert you if your data is on the dark web.

Keep yourself safe from cybercrime
There’s no way to completely eliminate the threat of cybercriminals, but by safeguarding your personal information and using security software, you can reduce your exposure. Norton 360 Deluxe helps protect you online by scanning your devices and blocking malware and hackers.
Equipped with a range of privacy and security tools including a password manager and VPN, you can create and use stronger passwords while encrypting your online activities wherever you are. Get ironclad online protection today.
FAQs about cybercriminals
Still have questions about cybercrime and cybercriminals? We have answers.
What is cybercrime?
Cybercrime is any crime committed using an electronic device or the internet. These crimes range from identity theft, injecting malware onto websites, creating disinformation campaigns, and selling illegal items and content. Cybercriminals may act independently, with other criminals, or even on behalf of a government.
What are some cybercrime examples?
The most common cybercrimes include:
- Creating and distributing malware
- Identity theft
- Debit or credit card fraud
- Data breaches
- Compromised passwords
- Unauthorized social media and email access
What is the difference between a hacker and a cybercriminal?
A cybercriminal is, by definition, someone who is committing a crime using computers or the internet. Hackers may commit crimes, but they can also work legally with government agencies and businesses (or independently) to look for and patch weaknesses.
Do cybercriminals get caught?
Yes, some cybercriminals do get caught. As international cooperation to target cybercriminals increases, the likelihood that they get caught grows.
Who are the most common victims of cybercrime?
Businesses in the financial, healthcare, and manufacturing industries are a few of the most common targets for cybercrime. According to the FBI, individuals between the ages of 30 and 39 reported the most cybercrimes against them.
What do cybercriminals do with stolen information?
What cybercriminals do with stolen information depends on what they take. If they steal corporate secrets, they may try to sell them to a rival company. If they take data from a government, they can release it or sell it to another country. When cybercriminals steal personal information, they may use it to commit identity theft or to ransom a person’s data.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.







Want more?
Follow us for all the latest news, tips, and updates.